Konni group exploits spear-phishing to deploy EndRAT malware and hijacks KakaoTalk sessions to propagate attacks through trusted contacts.
North Korean threat actors have developed a sophisticated attack campaign that transforms infected victims into unwitting malware distributors through their KakaoTalk messaging accounts, according to new research from South Korean cybersecurity firm Genians.
Spear-Phishing Opens the Door
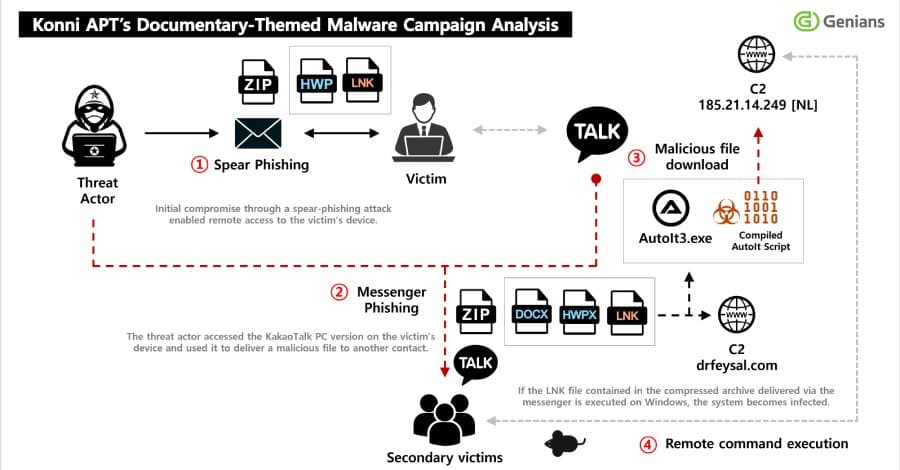
The attack begins with a carefully crafted spear-phishing email disguised as an official notice appointing the recipient as a North Korean human rights lecturer. This social engineering tactic exploits trust and authority to convince targets to open a malicious ZIP file attachment containing a Windows shortcut (LNK) file.
Once executed, the LNK file downloads a next-stage payload from external servers and establishes persistence through scheduled tasks. To maintain stealth, the malware displays a decoy PDF document while executing malicious code in the background.
EndRAT: The Core Malware Payload
The downloaded malware is EndRAT (also known as EndClient RAT), written in AutoIt. This remote access trojan provides attackers with comprehensive control over compromised systems, including file management, remote shell access, data transfer capabilities, and persistence mechanisms.
Analysis of infected hosts revealed multiple malicious artifacts, including AutoIt scripts corresponding to RftRAT and RemcosRAT families. The presence of multiple RAT variants suggests the attackers considered these victims particularly valuable and deployed redundant malware families to ensure continued access even if one is detected.
KakaoTalk Hijacking for Lateral Spread
The most concerning aspect of this campaign is how attackers leverage compromised KakaoTalk desktop applications. After establishing initial access, the threat actors use the victim's authenticated KakaoTalk session to selectively send malicious ZIP files to specific contacts in their friend list.
These files are disguised with filenames suggesting North Korea-related content, exploiting the trust between contacts to increase the likelihood of successful infection. This approach effectively turns victims into distribution nodes, expanding the attack's reach through trusted social networks.
Historical Context and Evolution
This is not Konni's first use of KakaoTalk for malware distribution. In November 2025, the group abused signed-in KakaoTalk sessions to send malicious payloads while simultaneously wiping victims' Android devices using stolen Google credentials.
The current campaign demonstrates an evolution in tactics, combining long-term persistence, information theft, and account-based redistribution into a multi-stage operation. By maintaining access to compromised systems for extended periods, attackers can gather sensitive documents while continuously propagating the malware through social engineering.
Technical Analysis and Indicators
The attack chain follows this progression:
- Spear-phishing email with malicious ZIP attachment
- LNK file execution triggering external payload download
- Scheduled task creation for persistence
- Decoy PDF display to distract victims
- EndRAT deployment with full remote access capabilities
- KakaoTalk session hijacking for lateral distribution
This campaign highlights the growing sophistication of state-sponsored threat actors who combine technical exploitation with social engineering to create self-propagating malware networks. Organizations should implement email filtering, endpoint detection, and user awareness training to defend against such multi-stage attacks.
The use of trusted communication platforms like KakaoTalk for malware distribution represents a significant escalation in attack methodology, as it bypasses traditional network defenses by exploiting human trust relationships rather than technical vulnerabilities.
Comments
Please log in or register to join the discussion