Lumen Technologies' Black Lotus Labs has disrupted a massive botnet operation by null-routing traffic to over 550 command-and-control nodes associated with the AISURU/Kimwolf botnet. This sophisticated network has compromised more than 2 million Android devices and 832 SOHO routers, creating a vast residential proxy infrastructure that threat actors use to conduct DDoS attacks and evade detection by blending malicious traffic with legitimate residential internet traffic.
The scale of modern botnet operations has reached staggering proportions, as demonstrated by Lumen Technologies' Black Lotus Labs' recent disruption of the AISURU/Kimwolf botnet infrastructure. Since early October 2025, researchers have null-routed traffic to more than 550 command-and-control nodes, effectively cutting off communication between infected devices and their operators. This action represents a significant blow to one of the largest botnet operations in recent years.

The Kimwolf Android TV Infection Vector
The Kimwolf botnet specifically targets Android TV streaming devices, turning them into residential proxy nodes through a technique that exploits both device vulnerabilities and user behavior. According to QiAnXin XLab's detailed analysis, the malware spreads through two primary channels: direct installation or via sketchy applications that come pre-installed on budget Android TV boxes.
The infection process begins with the delivery of a software development kit called ByteConnect. This SDK operates as the core component that transforms compromised devices into proxy nodes. What makes this particularly effective is the targeting of devices with exposed Android Debug Bridge (ADB) services. ADB is a legitimate development tool that allows developers to debug applications on Android devices, but when left enabled with network access and no authentication, it becomes a powerful entry point for attackers.
The botnet's operators scan the internet for devices with exposed ADB ports, then use the protocol to push their malicious payload. Once installed, the malware establishes a persistent connection to command servers and begins offering the device's bandwidth for sale on residential proxy marketplaces.
The Residential Proxy Economy
Residential proxies represent a particularly valuable asset for cybercriminals because they provide IP addresses that appear to come from legitimate home internet connections. Unlike datacenter IP addresses, which are easily identified and blocked by security systems, residential IPs blend seamlessly into normal internet traffic patterns.
Synthient's research revealed that Kimwolf actors actively attempt to offload proxy bandwidth in exchange for upfront cash, operating within a well-established underground economy. These services are typically advertised on Discord servers and other private channels, where botnet operators connect with customers who need residential IPs for various purposes, ranging from legitimate market research to malicious activities.
The value proposition is simple: customers gain access to IP addresses that bypass geographic restrictions, avoid IP-based blocking, and appear as legitimate residential traffic. For the botnet operators, this creates a steady revenue stream from compromised devices.
Aisuru Botnet Infrastructure
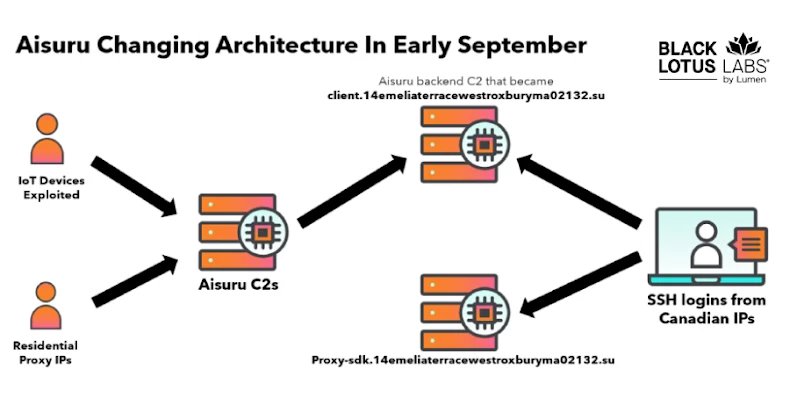
While Kimwolf focuses on Android devices, its counterpart Aisuru operates a broader infrastructure. Black Lotus Labs identified the backend C2 infrastructure at 65.108.5[.]46, which coordinated SSH connections from multiple Canadian IP addresses. These connections targeted 194.46.59[.]169, which resolved to a domain with an unusual name: proxy-sdk.14emeliaterracewestroxburyma02132[.]su.
This domain name itself tells a story about the operators' attempts at obfuscation. The seemingly random address format mimics legitimate residential location data, potentially making it harder to identify as malicious infrastructure. Remarkably, this domain surpassed Google in Cloudflare's top 100 domains list during November 2025, indicating the massive scale of connections flowing through this infrastructure. Cloudflare subsequently removed it from their public list.
In early October 2025, researchers identified another C2 domain: greatfirewallisacensorshiptool.14emeliaterracewestroxburyma02132[.]su. This domain resolved to 104.171.170[.]21, an IP address belonging to Resi Rack LLC, a Utah-based hosting provider that markets itself as a "Premium Game Server Hosting Provider."
The Resi Rack Connection
The involvement of Resi Rack LLC adds a troubling dimension to this case. According to investigative reporting by security journalist Brian Krebs, individuals associated with Resi Rack have been actively selling proxy services derived from botnet-infected devices for nearly two years.
The connection emerged through analysis of a Discord server called resi[.]to, which served as a marketplace for various proxy services. This server, now disappeared, was operated by someone using the handle "d" (likely short for "Dort"), with another individual known as "Snow" believed to be the botmaster coordinating the operation.
What makes this particularly concerning is that Resi Rack's co-founders allegedly participated in selling these proxy services directly through Discord. This blurs the line between legitimate hosting infrastructure and criminal enterprise, suggesting that some aspects of the botnet operation may have been operating under the guise of legitimate business activities.
The 300% Surge and Exploitation Cycle
Black Lotus Labs observed a dramatic 300% surge in new Kimwolf bot additions over a single week in early October 2025. This spike eventually contributed to a total infected device count reaching 800,000 by mid-month. Nearly all these new bots appeared for sale on a single residential proxy service, indicating coordinated mass deployment.
The botnet's operators employed a particularly clever exploitation technique between October 20 and November 6, 2025. They scanned PYPROXY and other proxy services for vulnerable devices, exploiting a security flaw that allowed interaction with devices on the internal networks of residential proxy endpoints.
Here's how this attack chain worked:
- Initial Compromise: The botnet identifies devices with exposed ADB or other vulnerabilities
- Proxy Integration: The compromised device becomes a node in a residential proxy network
- Internal Scanning: The botnet exploits flaws in proxy services to scan the internal network of that proxy endpoint
- Lateral Movement: Additional devices on the same residential network are discovered and compromised
- Expansion: The newly compromised devices join the botnet, creating exponential growth
This approach creates a self-reinforcing cycle where each infected proxy node becomes a launchpad for further infections within its local network.
Resilience Through Infrastructure Shuffling
When Black Lotus Labs successfully null-routed the greatfirewallisacensorshiptool domain, the operators quickly adapted. The domain moved to 104.171.170[.]201, another IP address under Resi Rack LLC's control. As this new server came online, researchers observed a massive spike in traffic to 176.65.149[.]19:25565, a server used to host the malware.
This server shared an ASN (Autonomous System Number) with Aisuru botnet infrastructure, confirming the interconnected nature of these operations. The rapid infrastructure shuffling demonstrates the operators' sophistication and their access to hosting resources that can quickly absorb null-routing actions.
The SOHO Router Threat Vector
The botnet landscape extends beyond Android devices into the realm of small office/home office (SOHO) routers. A report from Chawkr detailed a sophisticated proxy network containing 832 compromised KeeneticOS routers operating across Russian ISPs including Net By Net Holding LLC, VladLink, and GorodSamara.

These routers exhibited consistent SSH fingerprints and identical configurations, pointing toward automated mass exploitation. The attackers likely leveraged stolen credentials, embedded backdoors, or known security flaws in the router firmware. Each compromised router maintained both HTTP (port 80) and SSH (port 22) access, providing multiple avenues for control and data exfiltration.
Why Residential Proxies Evade Detection
The fundamental challenge in combating botnets like Kimwolf and Aisuru lies in the nature of residential proxy infrastructure. As Chawkr's analysis explains, these compromised endpoints operate below the radar of most security vendor reputation lists and threat intelligence feeds for several reasons:
Legitimate Classification: The IP addresses belong to legitimate residential ISPs, not datacenters or known hosting providers. Security systems typically trust residential traffic more than datacenter traffic.
Clean Reputation: Unlike datacenter IPs that may be shared among many customers and flagged for abuse, residential IPs typically have clean reputations because they represent individual home connections.
Traffic Pattern Blending: Malicious traffic originating from a residential IP appears identical to normal consumer activity. A DDoS attack launched from 10,000 residential IPs looks like 10,000 people streaming video or browsing the web.
Geographic Distribution: The global distribution of infected devices makes blocking entire geographic ranges impractical without causing significant collateral damage.
The Multi-Stage Attack Conduit
These compromised residential devices serve as more than just proxy nodes. They function as conduits for multi-stage attacks:
- Reconnaissance: Infected devices scan local networks for additional vulnerable devices
- Credential Harvesting: Proxy nodes can intercept and analyze traffic from devices on the same network
- C2 Communication: The residential IPs provide clean channels for command and control communication
- Attack Launching: DDoS attacks, credential stuffing, and other malicious activities originate from trusted residential IPs
- Evasion: When blocked, operators simply shift to different residential nodes
Practical Defensive Measures
For organizations and individuals seeking to protect against these botnets, several practical steps are essential:
Secure ADB Services: If you use Android TV devices or any Android-based embedded systems, ensure ADB is either disabled or properly secured. Never leave ADB enabled with network access without strong authentication.
Network Segmentation: Isolate IoT devices on separate network segments. This prevents compromised devices from scanning and attacking other devices on your network.
Firmware Updates: Regularly update router and IoT device firmware. Many botnets exploit known vulnerabilities that have patches available.
Monitor Outbound Traffic: Watch for unusual outbound connections, especially to domains with suspicious names or IPs associated with known malicious infrastructure.
Disable Unused Services: Turn off SSH, Telnet, and other management services on routers and IoT devices if they're not needed. If they must be enabled, use strong authentication and consider IP-based restrictions.
Behavioral Analysis: Implement security solutions that analyze traffic behavior rather than just relying on IP reputation. This helps detect malicious activity that blends into residential traffic patterns.
Industry Response and Disruption
The Black Lotus Labs' null-routing of 550+ C2 nodes represents a significant disruption, but it's important to understand what this achieves. Null-routing effectively blackholes traffic destined for those IP addresses or domains, cutting off communication between infected devices and their command servers.
However, this is not a permanent solution. The operators have already demonstrated their ability to quickly shift infrastructure. The battle requires continuous monitoring and coordinated action across multiple organizations.
The collaboration between security researchers, infrastructure providers like Cloudflare, and hosting companies will be crucial. When Cloudflare removed the malicious domain from their top 100 list and when hosting providers take action against abusive customers, it reduces the operators' ability to maintain stable infrastructure.
The Broader Trend
The Kimwolf and Aisuru botnets represent a broader trend in cybercrime: the weaponization of consumer devices and the creation of legitimate-looking business models around malicious infrastructure. By operating residential proxy services, botnet operators can:
- Generate steady revenue streams
- Blend their operations into legitimate business ecosystems
- Create legal ambiguity about their activities
- Maintain operational resilience through distributed infrastructure
This evolution makes detection and disruption more challenging. Security teams must adapt by focusing on behavioral indicators, network analysis, and coordinated infrastructure-level takedowns rather than simple IP blocking.
The fight against these botnets requires understanding not just the technical mechanisms, but the economic and social structures that support them. Only by addressing both the supply of vulnerable devices and the demand for residential proxy services can the security community make meaningful progress against these threats.
As the Black Lotus Labs team continues their work, this case serves as a reminder that modern cybersecurity threats operate at scale, leverage legitimate infrastructure, and require sophisticated, multi-layered responses from the entire security community.

Comments
Please log in or register to join the discussion