RFM (Router Flow Monitor) represents a significant advancement in lightweight network flow analysis, leveraging eBPF technology to provide efficient, low-overhead monitoring for Linux routers with seamless Prometheus integration.
In the evolving landscape of network monitoring, tools that balance depth of insight with minimal resource overhead have become increasingly valuable. RFM (Router Flow Monitor), an eBPF-based network flow analysis agent for Linux routers, emerges as a compelling solution for organizations seeking granular visibility without the complexity and resource demands of traditional monitoring systems. This project demonstrates how modern kernel technologies can transform network observability, particularly for environments already invested in Prometheus-based monitoring ecosystems.
At its core, RFM represents a philosophical shift in network monitoring design. Rather than attempting to replicate the comprehensive feature sets of established solutions like ntopng or pmacct, RFM embraces a focused approach: providing essential flow telemetry with exceptional efficiency. The project's architecture centers on eBPF programs attached to network interfaces via TC (Traffic Control), collecting per-flow statistics through configurable sampling while maintaining a remarkably small footprint—approximately 10 MB RSS when running as a single binary.
The technical implementation reveals thoughtful engineering decisions that contribute to RFM's efficiency. By using TCX for attaching BPF programs as link-based attachments, the tool takes advantage of newer kernel capabilities while maintaining compatibility with Linux 6.12+. The BPF behavior remains map-driven, with sampling rates and feature flags residing in a shared rfm_config map rather than being compiled-in constants. This design allows for runtime configuration adjustments, though the current implementation primarily writes configuration during startup.
Data flow in RFM follows an elegant pattern: TC programs classify each packet by direction, protocol family, and 5-tuple after parsing ethernet, VLAN, and QinQ headers. Every packet updates per-CPU interface counters, while sampled packets (1-in-N as configured) emit flow events to a ring buffer. In userspace, the collector reads these events, converts CLOCK_BOOTTIME timestamps to wall clock time, and aggregates flows into an in-memory table keyed by (ifindex, direction, protocol, src/dst address, src/dst port). This approach balances detail with performance, allowing administrators to adjust sampling rates based on their specific monitoring requirements.
What distinguishes RFM from other flow monitoring tools is its optional enrichment capabilities. The system can enhance basic flow data with information from two sources: a live BMP-fed RIB (Routing Information Base) and/or MMDB ASN/city databases. This enrichment occurs in userspace, allowing the kernel eBPF programs to remain lean and focused on packet processing. When both backends are enabled, ASN lookup prioritizes the RIB with MMDB as a fallback, while city information comes exclusively from MMDB. This design provides flexibility for organizations with varying data enrichment needs.
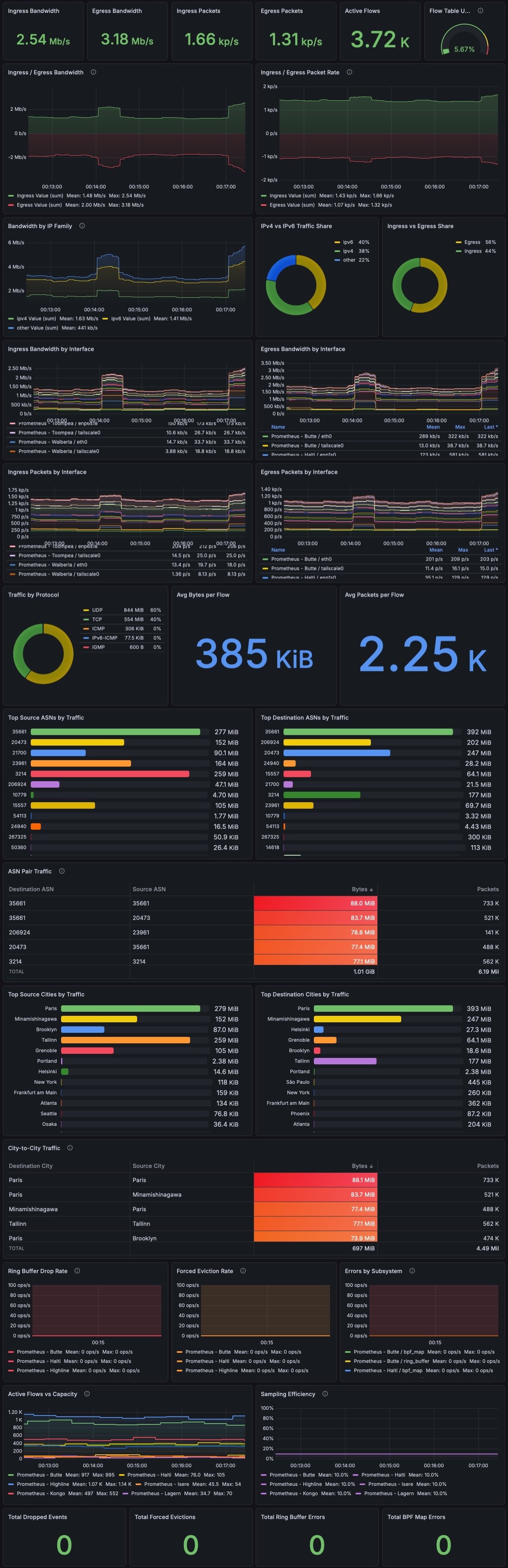
The Prometheus integration represents another thoughtful design choice. Rather than attempting to support multiple output formats, RFM concentrates on providing metrics in a format readily consumable by the increasingly popular Prometheus monitoring system. The exporter reads BPF interface counters directly and iterates through the flow table, rolling up flows by enrichment labels before emitting metrics. This approach eliminates unnecessary data transformations and leverages Prometheus' efficient pull-based model.
Configuration simplicity stands as another RFM strength. The tool uses a single TOML configuration file (default /etc/rfm/rfm.toml) with strict validation—unknown keys are rejected at load time to catch typos. The configuration structure clearly separates concerns, with distinct sections for BPF parameters, collector behavior, Prometheus settings, and enrichment options. This organization allows administrators to quickly understand and modify the tool's behavior without navigating complex nested configurations.
The inclusion of a Grafana dashboard demonstrates practical consideration for operational needs. While described as an "early" and "intentionally a starting point," the dashboard provides sufficient structure for basic operational views, including interface traffic breakdowns, protocol distribution, ASN and city summaries, and collector health metrics. This inclusion acknowledges that raw metrics, while valuable, benefit from thoughtful visualization to support effective monitoring practices.
RFM's comparison with alternative tools reveals its strategic positioning in the monitoring landscape. Unlike ntopng, which offers a comprehensive web interface and historical storage but requires supporting infrastructure like Redis and potentially databases, RFM delivers core functionality through a single binary. Similarly, while pmacct provides extensive flexibility through multiple daemons and configuration files, RFM simplifies deployment through its unified approach. For organizations already invested in Prometheus and seeking lightweight router flow monitoring, RFM offers an attractive middle path between the extremes of minimal monitoring and complex, feature-rich solutions.
The NixOS module inclusion further extends RFM's practical appeal, particularly for organizations embracing NixOS's declarative configuration management. The typed module options provide type safety and documentation, reducing configuration errors while maintaining the simplicity of the TOML-based configuration. This approach demonstrates awareness of modern infrastructure management practices and extends the tool's relevance beyond traditional Linux distributions.
Looking toward the future, RFM's planned features suggest continued evolution in network monitoring capabilities. The proposed Unix socket control plane would enable runtime management without restarting the agent, while IPFIX export would broaden compatibility with existing monitoring infrastructure. XDP firewall fast-path features could potentially merge monitoring and security functions, reducing overhead further. These planned enhancements indicate a commitment to expanding RFM's utility while maintaining its core design principles.
However, RFM's focused approach inherently involves trade-offs. The tool's simplicity means it lacks some advanced features found in more comprehensive solutions. Historical data storage, detailed protocol analysis, and extensive alerting capabilities would require integration with additional tools. Organizations with complex monitoring requirements might find RFM insufficient as a standalone solution, though it could serve effectively as a specialized component within a broader monitoring stack.
The licensing model reflects the practical realities of eBPF development. While the eBPF components use GPLv2 to satisfy kernel requirements, the remainder of the codebase uses AGPLv3. This approach balances the need to share kernel-level improvements with the flexibility for organizations to potentially use the tool internally without open modifications. The licensing, combined with the project's GitHub presence, suggests an open but commercially viable model.
RFM's significance extends beyond its immediate functionality. It represents a broader trend in observability tools leveraging kernel technologies to provide deeper insights with minimal overhead. As eBPF adoption continues to grow across the Linux kernel ecosystem, tools like RFM demonstrate how these technologies can transform network monitoring from a resource-intensive activity to a lightweight, integrated component of modern infrastructure.
For network operators managing Linux routers, particularly those already using Prometheus, RFM offers a compelling solution for gaining visibility into traffic patterns without introducing significant complexity or resource demands. The tool's design philosophy—focused, efficient, and integration-friendly—aligns with contemporary infrastructure management practices where observability should enhance rather than burden systems.
As network monitoring continues to evolve in response to increasingly distributed architectures and the growing importance of observability in operational excellence, RFM stands as a thoughtful implementation of modern kernel technologies applied to practical infrastructure challenges. Its combination of eBPF efficiency, Prometheus integration, and optional enrichment capabilities provides a template for how observability tools can deliver valuable insights while respecting the resource constraints of production environments.
Comments
Please log in or register to join the discussion