Critical government infrastructure compromised as threat actor releases full platform source code for free, with citizen databases sold separately
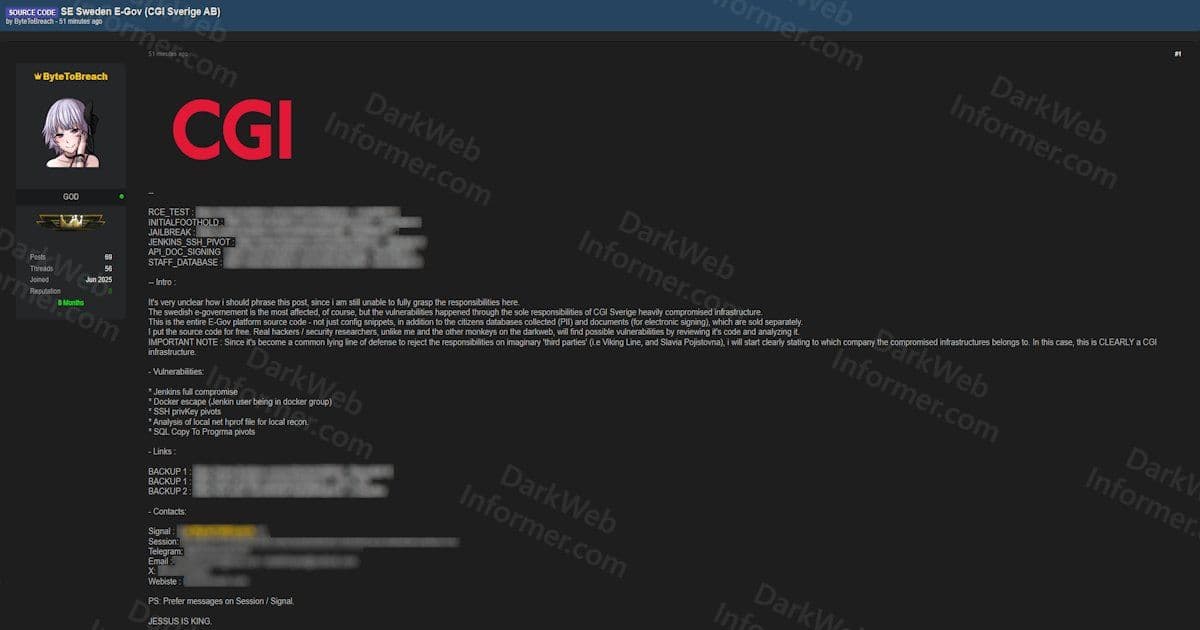
A major cybersecurity incident has struck Sweden's digital government infrastructure, with the complete source code of the country's E-Government platform now circulating freely on dark web forums. The breach, attributed to a threat actor known as ByteToBreach, represents a significant compromise of CGI Sverige AB's systems - the Swedish arm of global IT services provider CGI Group that manages critical government digital services.
The Breach Details
The attack, which occurred on March 12, 2026, at 18:25:21 UTC, exposed vulnerabilities across multiple layers of CGI Sverige's infrastructure. According to the threat actor's claims, the breach involved a comprehensive compromise that went far beyond simple data theft. The actor explicitly states that this is the "full E-Gov platform source code" - not just configuration snippets or partial files.
The technical methodology employed by the attackers reveals a sophisticated approach to lateral movement and privilege escalation. The disclosed attack chain includes:
- Full Jenkins compromise: The attackers gained complete control over CGI Sverige's Jenkins CI/CD infrastructure
- Docker escape via Jenkins user: The Jenkins service account had Docker group membership, enabling container escape
- SSH private key pivots: Attackers leveraged SSH credentials to move laterally across the network
- .hprof file analysis: Local heap dump files were analyzed for reconnaissance purposes
- SQL copy-to-program pivots: Database pivoting techniques were used to extract data
Scope of Compromised Data
Beyond the source code itself, the breach encompasses multiple categories of sensitive information. The threat actor has organized the compromised data into distinct packages:
Source Code Package (Released Free):
- Complete E-Government platform source code
- Staff database with employee records
- API document signing systems
- Jenkins SSH pivot credentials
- RCE test endpoints
- Initial foothold and jailbreak artifacts
Separate Sales Packages:
- Citizen PII databases (being sold separately)
- Electronic signing documents (being sold separately)
This separation strategy suggests the threat actor is attempting to maximize profit while still causing reputational damage by releasing the core platform code.
Pattern of Activity
Interestingly, ByteToBreach has claimed responsibility for multiple high-profile breaches in recent days. The actor references yesterday's Viking Line breach, indicating a pattern of targeting Nordic organizations. Additionally, the threat actor makes pointed references to other companies - specifically mentioning Viking Line and Slavia Pojistovna as examples of organizations that have blamed third parties for breaches.
This commentary suggests the attacker is deliberately highlighting what they perceive as misattribution of responsibility in previous incidents, emphasizing that "this compromise belongs clearly to CGI infrastructure."
Security Implications
The release of Sweden's E-Government platform source code carries severe implications for national cybersecurity. With the complete codebase now publicly available, malicious actors can:
- Analyze the code for additional vulnerabilities
- Create targeted attack tools specific to the platform
- Understand the architecture and potential weak points
- Develop bypass techniques for security controls
For a government platform handling citizen services, this level of exposure could enable sophisticated attacks on critical infrastructure, potentially affecting everything from tax services to healthcare systems.
Response and Mitigation
As of the time of reporting, neither CGI Sverige nor Swedish government authorities have issued formal statements about the breach. The free distribution of the source code through multiple backup download links suggests the attackers are confident in their ability to evade takedown efforts.
Organizations using similar platforms or third-party services should review their:
- CI/CD pipeline security
- Docker container configurations
- SSH key management practices
- Jenkins server hardening procedures
- Database access controls
Broader Context
This incident highlights the growing risks associated with government digital transformation initiatives. As more critical services move online and rely on third-party providers, the attack surface expands significantly. The compromise of a single infrastructure provider can have cascading effects across multiple government services and citizen data.
For Sweden specifically, this breach raises questions about the security posture of its digital government initiatives and the vetting processes for third-party vendors managing critical infrastructure. The fact that citizen PII and electronic signing documents were also compromised, even if being sold separately, indicates the breadth of the security failure.
The full impact of this breach will likely unfold over the coming weeks and months as security researchers and malicious actors alike analyze the leaked source code and potentially exploit newly discovered vulnerabilities.
Comments
Please log in or register to join the discussion