UUIDs solve the critical problem of generating globally unique identifiers in distributed systems where traditional auto-increment IDs fail due to predictability, scalability limits, and security risks.
When designing systems that span multiple servers, databases, or services, generating unique identifiers without central coordination becomes a fundamental challenge. Auto-increment integers work well in single-database setups but collapse in distributed environments: they create hotspots at the database level, expose implementation details through predictability, and require coordination that undermines scalability. This is where UUIDs (Universally Unique Identifiers) provide a robust solution through their 128-bit structure and probabilistic uniqueness guarantees.
A UUID’s strength lies in its design: the 128-bit space yields 2^128 possible values (approximately 3.4×10^38), making collisions statistically negligible even at massive scale. For context, generating 1 billion UUIDs per second would take over 100 years to reach a 50% collision probability. This property eliminates the need for central ID generators, allowing any service node to create identifiers independently—a critical advantage for microservices architectures and globally distributed databases.
However, not all UUID versions are equal, and choosing the wrong variant introduces hidden costs. UUID v1 combines a timestamp with the generator’s MAC address, providing time-ordering useful for database indexing but exposing hardware addresses and creating privacy concerns. UUID v4 relies entirely on random numbers, offering strong privacy and simplicity but resulting in non-sequential values that can cause index fragmentation in B-tree databases during high-volume inserts. Modern applications increasingly favor UUID v7, which replaces v1’s MAC address with random bits while preserving Unix millisecond timestamp ordering. This delivers the insertion performance benefits of time-ordered IDs without v1’s privacy drawbacks, making it ideal for primary keys in scalable databases like PostgreSQL or Cassandra.
The trade-offs extend beyond technical considerations. While UUIDs prevent ID guessing attacks (unlike sequential integers), their larger storage size (16 bytes vs 4-8 bytes for integers) impacts index size and memory usage—a factor to consider in extreme-scale scenarios. Some systems opt for alternatives like Twitter’s Snowflake or ULIDs when they require stricter ordering or smaller footprints, but UUIDs remain the universal choice when true decentralization and cross-system uniqueness are non-negotiable.
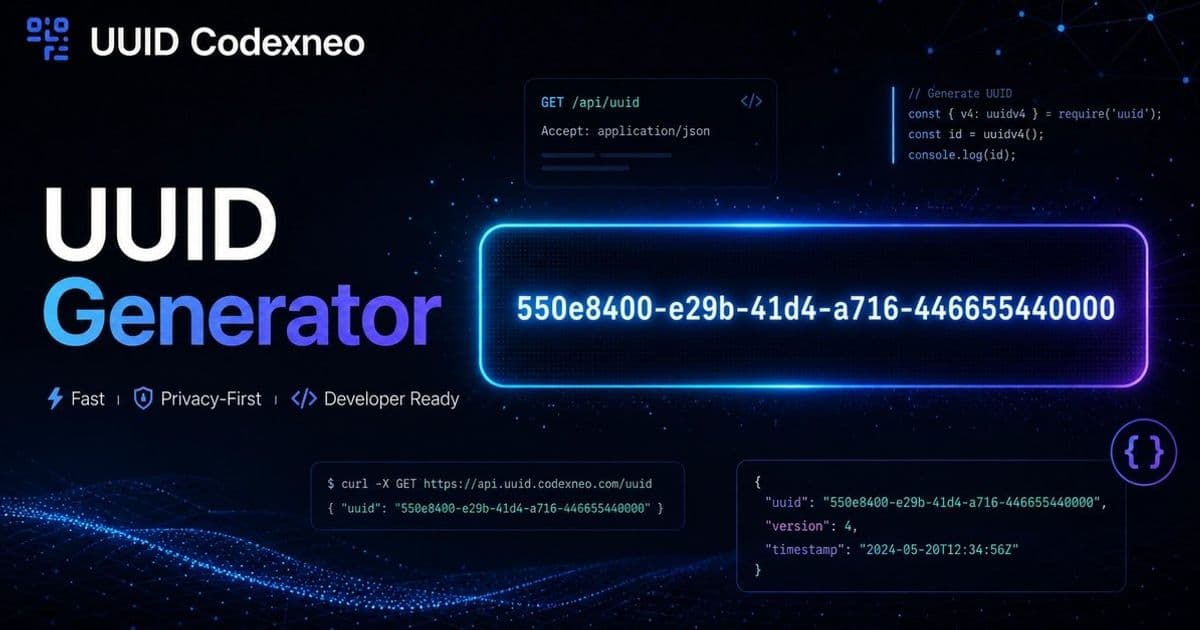
For developers implementing UUID generation, prioritize libraries that use cryptographically secure random number generators (CSPRNGs) for v4/v7 implementations. Tools like the open-source UUID Codexneo demonstrate best practices: client-side generation ensuring zero server tracking, API endpoints for serverless environments, and strict adherence to RFC 4122 standards. Remember that UUIDs aren’t merely "random strings"—they are a carefully engineered solution to one of distributed systems’ oldest problems. When your architecture spans trust boundaries or requires horizontal scaling, reaching for UUIDs isn’t just convenient; it’s often the only viable path to correctness.
Comments
Please log in or register to join the discussion