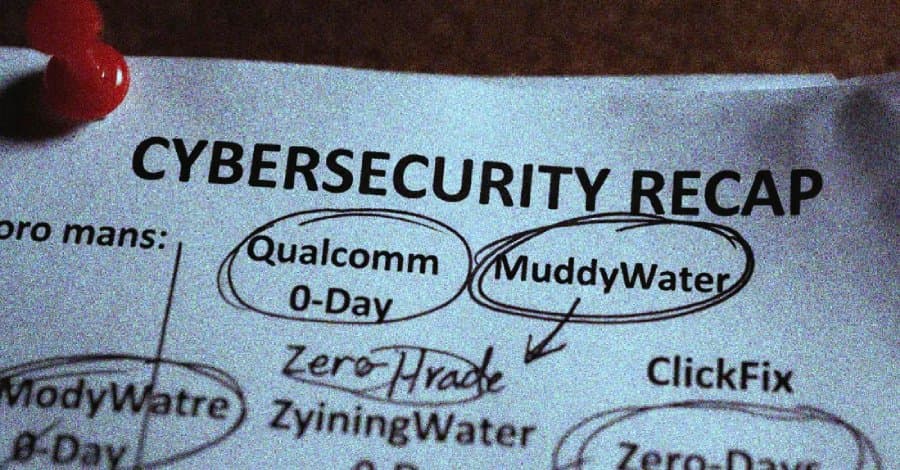
A comprehensive analysis of this week's most significant cybersecurity threats, including a Qualcomm chip vulnerability being exploited in the wild, sophisticated iOS exploit chains, and a new attack that bypasses Wi-Fi client isolation protections.
Weekly Security Roundup: Qualcomm Flaws, iOS Exploit Chains, and AirSnitch Wi-Fi Attacks
Another week in cybersecurity brings another wave of sophisticated attacks and vulnerabilities that organizations need to address. From zero-day exploits in widely used chips to AI-powered malware development, the threat landscape continues to evolve at a rapid pace. This week's highlights include a Qualcomm vulnerability being actively exploited, powerful iOS exploit chains targeting older devices, and a new research showing how Wi-Fi client isolation can be bypassed.
Qualcomm Chip Vulnerability Under Active Exploitation
Google has confirmed that CVE-2026-21385, a high-severity vulnerability affecting Qualcomm chips used in Android devices, is being exploited in the wild. The flaw, which carries a CVSS score of 7.8, is a buffer over-read in the Graphics component that could result in memory corruption and arbitrary code execution.
"There are indications that CVE-2026-21385 may be under limited, targeted exploitation," Google acknowledged in its monthly Android security bulletin. While the company hasn't provided details on how the vulnerability is being exploited, the confirmation of active exploitation means this should be prioritized for patching.
Organizations using Android devices with Qualcomm chips should:
- Immediately apply available security patches
- Monitor for suspicious activity on affected systems
- Consider network segmentation for critical devices until patches are applied
The vulnerability affects numerous Android devices, making it particularly concerning given the widespread use of Qualcomm chips in the mobile ecosystem. Google's Android Security Bulletin provides detailed information on affected devices and available patches.
Coruna iOS Exploit Kit Shows Sophistication of Mobile Threats
Google researchers disclosed details of a sophisticated exploit kit called Coruna (also known as CryptoWaters) that targets Apple iPhone models running iOS versions between 13.0 and 17.2.1. What makes Coruna particularly notable is its complexity and journey through multiple threat actor groups.
The exploit kit features five full iOS exploit chains and a total of 23 exploits, making it one of the most comprehensive iOS attack tools discovered to date. Its evolution is equally concerning:
- Started as a commercial surveillance vendor tool in February 2025
- Picked up by what appears to be a Russian espionage group targeting Ukrainians in July 2025
- Ended up in the hands of financially motivated attackers in China targeting crypto wallets by the end of 2025

"Coruna began its life as a surveillance exploit kit, but by the time it reached the Chinese cybercrime gang, it was heavily focused on financial theft," researchers noted. The unclear transmission path between these diverse threat actors suggests the existence of a thriving market for selling and repurposing sophisticated exploit kits.
Organizations should:
- Ensure all iOS devices are updated to the latest supported versions
- Implement strict mobile device management policies
- Monitor for unusual network traffic from mobile devices
- Consider restricting older iOS versions that may be vulnerable
AirSnitch Attack Exposes Wi-Fi Client Isolation Weaknesses
Researchers have developed a new attack called AirSnitch that breaks the encryption designed to separate Wi-Fi clients, potentially undermining a fundamental security protection in many networks. The attack leverages three weaknesses in client isolation implementations:
- Abuse of group keys shared between all clients in the same Wi-Fi network
- Bypassing client isolation by tricking the gateway into forwarding packets at the IP layer
- Manipulating internal switches and bridges to forward victim traffic to the attacker
"We found that Wi-Fi client isolation can often be bypassed," said Mathy Vanhoef, a prominent security researcher. "This allows an attacker who can connect to a network, either as a malicious insider or by connecting to a co-located open network, to attack others."

The implications are significant for organizations relying on Wi-Fi client isolation as a primary security control. To mitigate this risk:
- Implement additional network segmentation beyond Wi-Fi client isolation
- Use encrypted protocols for all sensitive communications
- Consider physical security controls for access points
- Monitor for unusual traffic patterns between supposedly isolated clients
AI-Powered Malware Development Raises Concerns
The Pakistan-aligned threat actor Transparent Tribe has been using AI-powered coding tools to develop malware targeting Indian government entities and embassies. These tools, written in niche programming languages like Nim, Zig, and Crystal, demonstrate how AI is being weaponized to create more evasive malware.
"Rather than a breakthrough in technical sophistication, we are seeing a transition toward AI-assisted malware industrialization that allows the actor to flood target environments with disposable, polyglot binaries," security researchers noted.

This trend highlights the need for:
- Enhanced detection capabilities for unusual programming languages
- Behavioral analysis rather than signature-based detection
- Regular updates to security tools to recognize new obfuscation techniques
- Developer awareness of secure coding practices to prevent introduction of vulnerabilities
Iranian Hackers Target U.S. Entities Amid Geopolitical Tensions
The Iranian hacking group MuddyWater (also known as Seedworm) has been targeting several U.S. companies, including banks, airports, non-profits, and software companies, in a campaign that began in early February 2026. This activity coincides with heightened geopolitical tensions in the Middle East.
"The trajectory is clear: what began as nation-state-level ICS capability in 2012 has become, by 2026, something any motivated actor can attempt with free tools and an internet connection," researchers noted. "The technical barrier has collapsed. The threat pool has expanded. And the US attack surface has never been larger."
In a related development, a Hamas-affiliated actor known as Arid Viper has distributed a trojanized version of the Red Alert rocket warning Android app to Israeli users via SMS messages impersonating official communications. The malware monitors and abuses granted permissions to collect sensitive data.
Organizations should:
- Review and enhance security postures, especially for critical infrastructure
- Implement multi-factor authentication across all systems
- Conduct regular security awareness training
- Monitor for geopolitical threat intelligence relevant to your organization
Ransomware Actors Shift Tactics, Use Legitimate Tools
Ransomware operators are increasingly using Microsoft's AzCopy utility for data exfiltration, turning a trusted Azure tool into a stealthy mechanism for stealing information. This represents a continuation of the "living-off-the-land" approach that makes malicious activity harder to detect.
"The adoption of AzCopy and other familiar tools by attackers represents a similar logic to living-off-the-land in the final and most critical phase of an operation: exfiltrating data out of an organization," researchers explained. "Spinning up an Azure storage account takes minutes and requires only a credit card or compromised credentials."

This trend underscores the importance of:
- Monitoring for unusual use of legitimate administrative tools
- Implementing strict controls over data exfiltration
- Regular auditing of privileged accounts
- Network segmentation to limit lateral movement
Key Vulnerabilities Requiring Immediate Attention
Several critical vulnerabilities were disclosed this week that organizations should prioritize:
- CVE-2026-2796 (Mozilla Firefox): Multiple vulnerabilities addressed in Firefox 148
- CVE-2026-1492 (WPEverest): Critical flaw (CVSS 9.8) allowing creation of rogue admin accounts
- CVE-2026-27636 & CVE-2026-28289 (FreeScout): Mail2Shell vulnerabilities
- Multiple Cisco vulnerabilities: Including CVE-2026-20079 in Cisco Secure Firewall Management Center
- AWS-LC vulnerabilities: Multiple issues in Amazon's cryptographic library
Positive Developments in Cybersecurity
Not all news this week was negative. Law enforcement and security companies achieved significant wins:
Tycoon 2FA and LeakBase Dismantled: A coalition of security companies and law enforcement agencies successfully took down the infrastructure hosting Tycoon2FA, one of the largest adversary-in-the-middle phishing operations, and LeakBase, a major forum for cybercriminals.
Anthropic-Mozilla Partnership: Anthropic discovered 22 new security vulnerabilities in Firefox using its Claude Opus 4.6 LLM, with 14 classified as high severity. The vulnerabilities were addressed in Firefox 148.
Declining Ransomware Payments: According to Chainalysis, total ransomware payments stagnated in 2025, with the payment rate dropping from 63% in 2024 to just 29% last year, suggesting organizations are increasingly refusing to pay ransoms.
Conclusion
This week's security landscape highlights several important trends: the increasing sophistication of mobile exploits, the weaponization of AI for malware development, and the continued evolution of ransomware tactics. The AirSnitch research serves as a reminder that even fundamental security controls like Wi-Fi client isolation may have vulnerabilities that require additional mitigation strategies.
Organizations should prioritize patching for the Qualcomm vulnerability and other critical flaws, enhance their monitoring for unusual activity, and maintain robust security practices even as the threat landscape continues to evolve. The positive developments in takedown operations and vulnerability research show that progress is being made, but constant vigilance remains essential.
For organizations looking to enhance their security postures, consider exploring tools like DetectFlow for real-time log analysis and ADTrapper for Active Directory threat detection.
As always, maintaining a strong security posture requires a combination of technology, processes, and people. Stay informed, patch promptly, and maintain a healthy skepticism toward unexpected communications and requests.
Comments
Please log in or register to join the discussion