A researcher has discovered a critical security flaw in Windows 11 and Server 2022/2025 that allows BitLocker encryption to be bypassed using a simple USB stick and a keyboard combination. The vulnerability, named YellowKey, works by exploiting the Windows Recovery Environment and affects systems using TPM-only mode, which is the default on most consumer machines. The researcher believes this may be an intentional backdoor rather than an oversight, as Windows 10 remains unaffected.
Windows 11 BitLocker Vulnerability Exposes Systems via USB Recovery Exploit
Critical Security Flaw Discovered in Windows 11 Recovery Environment
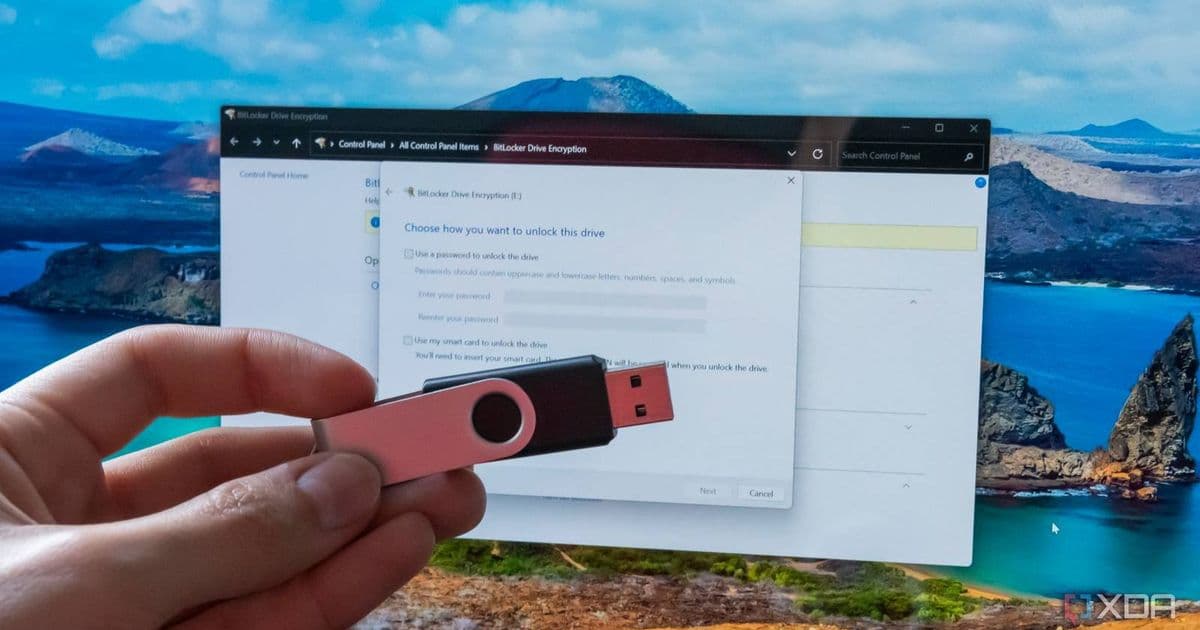
On May 12th, security researcher Nightmare-Eclipse published a proof-of-concept exploit called "YellowKey" that demonstrates a serious vulnerability in Windows 11 and Server 2022/2025. The exploit allows attackers to bypass BitLocker encryption protection, one of Windows' most critical security features, using nothing more than a USB stick and a simple keyboard combination during system reboot.
The vulnerability specifically affects systems using BitLocker in TPM-only mode, which is the default configuration on most consumer Windows 11 installations. This means that millions of devices could be vulnerable to this attack, potentially exposing sensitive data to unauthorized access.
How the YellowKey Exploit Works
The YellowKey exploit is remarkably simple in execution, which makes it particularly concerning. The entire proof-of-concept consists of a folder that can be copied to a USB stick. The attack is triggered when an attacker holds the CTRL key during a normal reboot, forcing the system to enter the Windows Recovery Environment (WinRE).
Once in the WinRE, the exploit leverages a component that exists only within the recovery image. According to the researcher, a component with the same name exists in normal Windows installations but lacks the specific functionality that enables the bypass. This difference between the recovery environment and the main OS is a key part of what makes the vulnerability possible.
Independent verification of the exploit has already been confirmed by security researcher KevTheHermit, who successfully demonstrated it against Windows 11 build 10.0.26100.1 and shared the results on social media.
Potential Bypass of Enterprise Security Measures
What makes this vulnerability even more concerning is its potential to bypass certain enterprise security measures. The researcher notes that the USB stick isn't strictly necessary for the exploit to work. If an attacker can temporarily remove the disk from the target machine, write the FsTx folder to the EFI system partition, and then return the disk to the system, the exploit will still trigger.
This method could circumvent the "no removable media" mitigation that some enterprise deployments implement to prevent exactly this type of physical attack. While reproducing the attack cleanly may require several attempts and potentially formatting the USB stick between tries, these are merely inconveniences for an attacker, not meaningful barriers to the exploit's success.
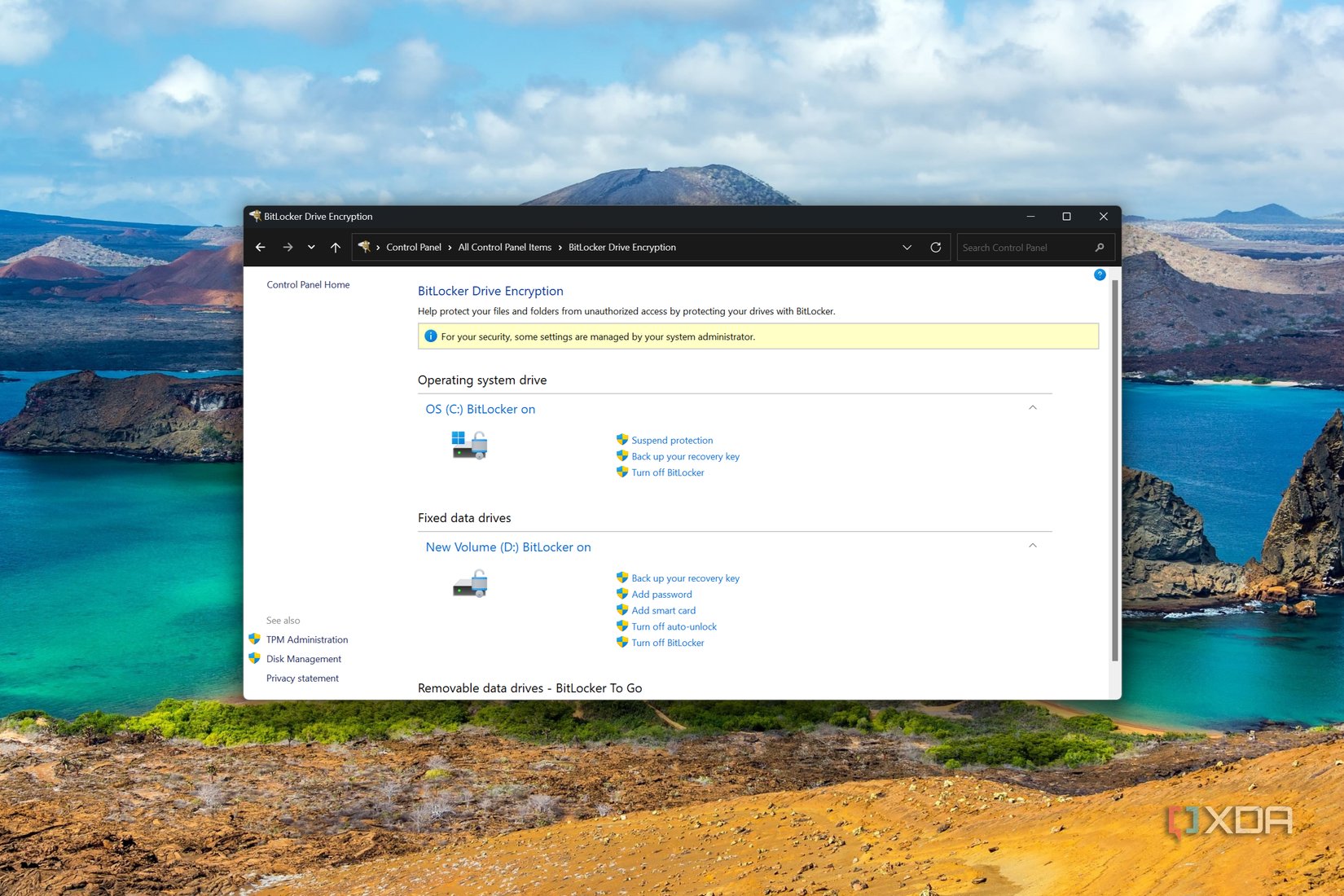 Screenshot of BitLocker settings in Control Panel showing multiple fixed drives are encrypted
Screenshot of BitLocker settings in Control Panel showing multiple fixed drives are encrypted
Windows 10's Unexpected Immunity
One puzzling aspect of this vulnerability is that Windows 10 appears to be completely unaffected. The researcher has not provided a definitive explanation for why this is the case, though it suggests that changes made between Windows 10 and Windows 11 in the recovery environment or related components may have introduced this vulnerability.
The lack of a clear explanation for Windows 10's immunity has led some to speculate that this might not be an oversight but rather an intentional feature. The researcher themselves has stated they "just can't come up with an explanation beside the fact that this was intentional," suggesting the possibility that this could be a backdoor rather than a simple coding error.
Secondary Exploit: GreenPlasma
Alongside YellowKey, the researcher also disclosed a secondary exploit called "GreenPlasma." This is a local privilege escalation vulnerability targeting the CTFMON subsystem that allows an attacker to gain SYSTEM privileges from a normal user account. While the researcher published an analysis of the technique, they intentionally removed the final escalation code from the public disclosure.
The researcher has been vocal about their belief that Microsoft has more information about these vulnerabilities than they're letting on. In a blog post, they stated: "I can't wait when I will be allowed to disclose the full story, I think people will find my crashout very reasonable and it definitely won't be a good look for Microsoft." Another post was even more direct: "Next patch [T]uesday will have a big surprise for you Microsoft. And remember, I never failed to deliver a promise."
Microsoft's Response and Available Mitigations
As of the time of writing, Microsoft has not issued a public acknowledgment of the YellowKey vulnerability or assigned a CVE number to it. The company provided a standard statement when contacted:
"Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible. We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community."
The nature of the vulnerability presents a challenge for Microsoft. Since the bug resides within the WinRE image rather than the main operating system, a standard cumulative update won't suffice. The company could potentially issue an out-of-band fix if they determine the issue warrants such urgency, but recovery partition updates have historically been problematic. This was demonstrated a few years ago when KB5028997 required many users to manually resize their recovery partition before the update would install successfully.
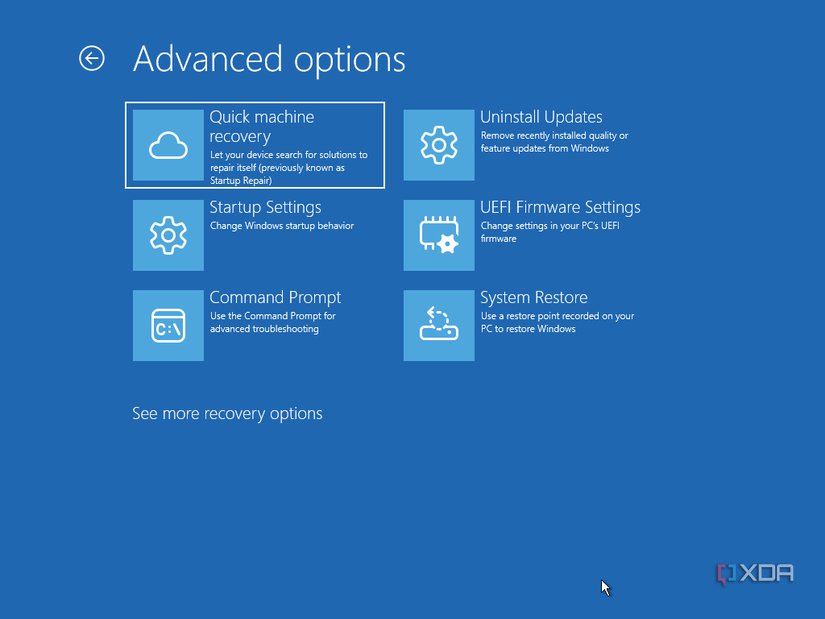 Screenshot of the Windows Recovery Environment showing various troubleshooting and recovery options
Screenshot of the Windows Recovery Environment showing various troubleshooting and recovery options
Recommended Actions for Users
Given the severity of this vulnerability and the lack of an immediate fix from Microsoft, users should consider taking the following precautions:
Assume all devices are unencrypted: Until a patch is available and deployed, treat all systems as if they lack encryption protection.
Implement additional security layers: Consider using additional security measures such as full disk encryption solutions that operate independently of the OS, or implementing physical security controls like secure boot and TPM protections beyond BitLocker.
Monitor for official patches: Keep a close eye on Microsoft's security updates and patch Tuesday releases for any addressing this vulnerability.
Consider disabling WinRE: For advanced users with specific needs, temporarily disabling the Windows Recovery Environment may prevent this exploit from being used, though this comes with its own set of risks and inconveniences.
Change critical passwords: As a precaution, users should consider changing passwords for sensitive accounts, especially if there's any possibility that their devices may have been compromised.
The discovery of YellowKey highlights the complex relationship between convenience and security in modern operating systems. While features like the Windows Recovery Environment provide valuable troubleshooting capabilities, they can also introduce potential security vulnerabilities that attackers may exploit. As Microsoft works to address this issue, users should remain vigilant and consider implementing additional security measures to protect their sensitive data.
The researcher has indicated that they may disclose additional information about these vulnerabilities in the future, which could provide more insight into their root cause and potential impact. Until then, the security community and users alike will be watching closely for Microsoft's response to this significant security concern.
Comments
Please log in or register to join the discussion