A newly discovered vulnerability in Windows 11 and Server 2022/2025 allows attackers to bypass BitLocker encryption protection through a surprisingly simple exploit method, prompting speculation about potential backdoor functionality in Microsoft's codebase.
The security research community has been abuzz with the discovery of YellowKey, a BitLocker bypass vulnerability that represents one of the most significant encryption flaws to emerge in recent years. Discovered by researcher Nightmare-Eclipse and documented in a GitHub repository, this vulnerability affects Windows 11 and Server 2022/2025, allowing attackers to access BitLocker-protected volumes without proper authentication.
The Vulnerability Explained
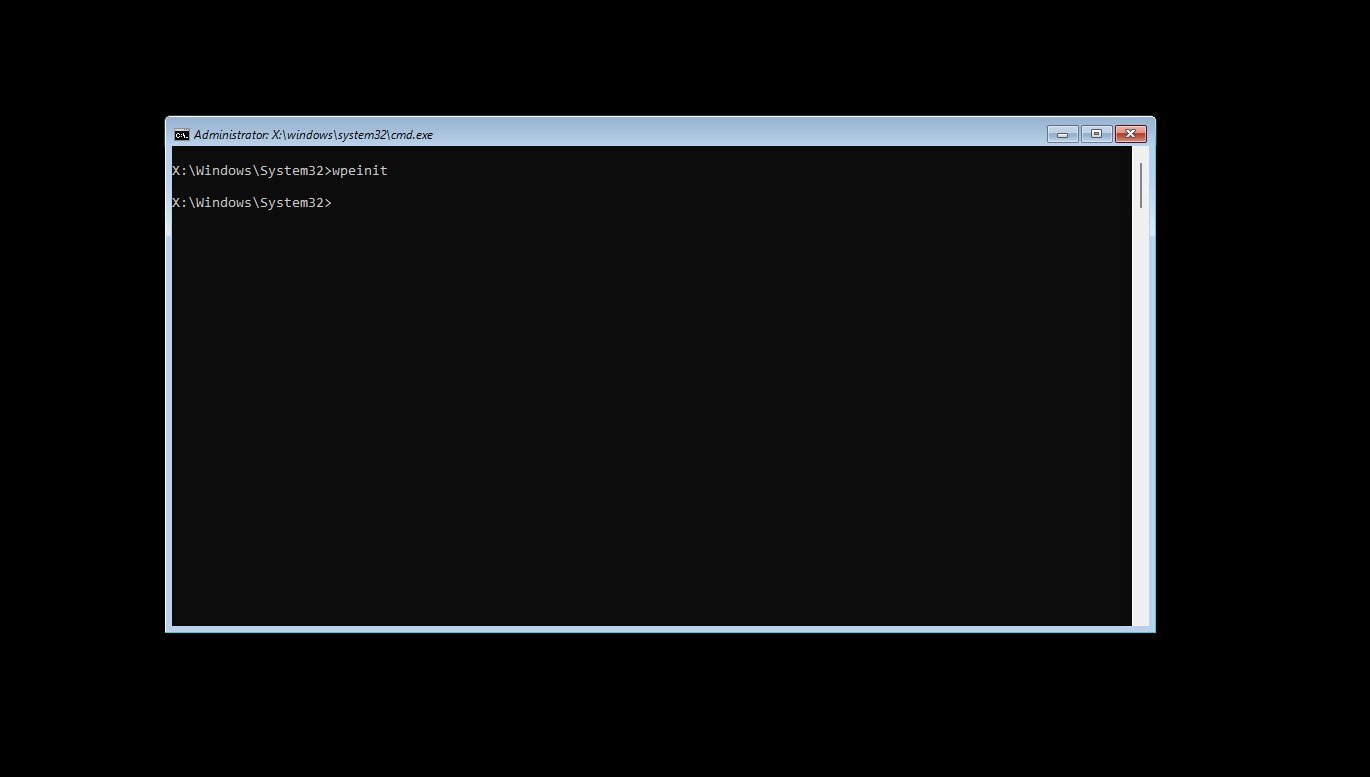
At its core, YellowKey exploits a component within the Windows Recovery Environment (WinRE) that, when triggered through a specific sequence of actions, spawns an unrestricted shell with access to encrypted volumes. The exploit method is remarkably straightforward:
- Copy the FsTx folder to "YourUSBStick:\System Volume Information\FsTx" (NTFS is preferred but FAT32/exFAT may also work)
- Boot the target Windows system into the Recovery Environment (using SHIFT + restart)
- At the precise moment of restart, release SHIFT and hold CTRL
- This action spawns a shell with unrestricted access to the BitLocker-protected volume
What makes this vulnerability particularly concerning is its flexibility. As the researcher notes, "you don't even need to plug an external storage device, you can just pull out the disk, copy the files in the EFI partition, put it back and it will still work. That's how bad it is."
Backdoor or Oversight?
The researcher raises provocative questions about the nature of this vulnerability, suggesting it might be intentionally placed rather than an oversight. Several factors contribute to this suspicion:
- The vulnerable component exists only within WinRE images and cannot be found elsewhere online
- A component with the exact same name exists in normal Windows installations but lacks the functionality that triggers the vulnerability
- The vulnerability affects Windows 11 and Server 2022/2025 but not Windows 10
"The component that is responsible for this bug is not present anywhere (even in the internet) except inside WinRE image and what makes it raise suspicions is the fact that the exact same component is also present with the exact same name in a normal windows installation but without the functionalities that trigger the bitlocker bypass issue," the researcher explains.
Implications for Data Security
This vulnerability undermines one of Microsoft's cornerstone security features—BitLocker encryption—which is widely used by enterprises and individuals to protect sensitive data. The implications are far-reaching:
- Data Breach Risk: Confidential information stored on encrypted volumes could be accessed without proper authorization
- Forensic Challenges: Digital investigations may be complicated as encrypted volumes could be accessed illicitly
- Enterprise Vulnerability: Organizations relying on BitLocker for compliance may face unexpected security gaps
- Trust Erosion: The discovery could reduce confidence in Microsoft's security implementations
The Bigger Picture
The YellowKey vulnerability emerges at a time when encryption is more critical than ever. With increasing threats to data privacy and security, features like BitLocker are essential protections for both individuals and organizations. The fact that such a fundamental flaw exists in a core security feature is particularly troubling.
The researcher credits Microsoft's security teams (MORSE, MSTIC, and Microsoft GHOST) for helping make this public disclosure possible, suggesting a responsible approach to vulnerability disclosure. This collaboration between researchers and Microsoft is a positive sign for the security ecosystem.
Mitigation and Future Outlook
While the vulnerability is serious, it's important to note that it requires physical access or the ability to modify boot media, which limits some attack vectors. Organizations should consider additional security measures beyond BitLocker, such as physical security controls and boot protection mechanisms.
Microsoft has not yet released an official statement or patch regarding YellowKey. As with any newly discovered vulnerability, users should monitor official Microsoft security channels for updates and mitigation strategies.
The discovery of YellowKey serves as a reminder that even the most trusted security features can have unexpected vulnerabilities. It also highlights the importance of ongoing security research and the value of independent security researchers in identifying and addressing potential flaws in widely used software.
Comments
Please log in or register to join the discussion