Cilium 1.19 marks ten years of eBPF-based networking with enhanced encryption, safer multi-cluster policies, and improved observability for large-scale Kubernetes deployments.
Cilium 1.19 has been released, marking ten years of development for the eBPF-based networking and security project. There isn't a flagship feature in this release; instead, it focuses on security hardening, tightening encryption, refining network policy behaviour, and improving scalability for large Kubernetes clusters.

The Cilium post on LinkedIn describes 1.19 as a special release celebrating 10 years since the first commit, with over 2,900 commits from 1,000+ developers. The 2025 annual Cilium report explains how Cilium has quietly become the dominant CNI in production Kubernetes environments, with over 60 per cent of surveyed deployments using Cilium and more than 75 per cent relying on Cilium-based data planes once managed services such as Azure CNI powered by Cilium and GKE Datapath V2 are included.
This position is linked in the report to deliberate technical selection rather than platform defaults, with respondents citing performance, eBPF based observability via Hubble, and advanced policy semantics as the main reasons for adoption, which aligns closely with the emphasis in 1.19 on stricter encryption modes, safer cross cluster defaults and deeper traffic tracing.
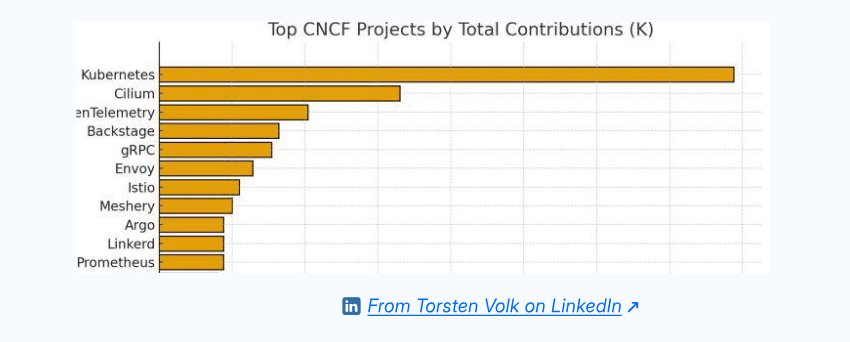
The report also show that contribution levels have stabilised at around 10,000 pull requests per year, and that Cilium is now the second largest CNCF project by contributions behind only Kubernetes.
A second theme in the report is the extension of Cilium and its related projects into new domains, particularly AI workloads and unified networking across Kubernetes and virtual machines. Large organisations such as Microsoft, Google and TikTok are described as using Cilium to power some of the largest AI training clusters and IPv6 only data centre deployments, while case studies from firms like ESnet and Nutanix highlight the value of consistent observability and policy controls across heterogeneous environments.
The same document positions Tetragon as an emerging runtime security layer, with work on Windows support, persistent enforcement and userspace hook points via uprobes and USDTs, which complements the 1.19 focus on stricter encryption and improved drop attribution in Hubble by moving more enforcement logic into a dedicated security plane.
Stricter Encryption Modes for Zero Trust Environments
The 1.19 release introduces strict modes for both IPsec and WireGuard. This change shifts encryption from a best-effort option to a hard requirement between nodes. In strict mode, unencrypted inter-node traffic is dropped. This satisfies internal policies that financial and public sector environments may have, aiming to remove reliance on implicit trust within a cluster network.
The project's summary notes that this change is primarily for "regulated or zero trust environments." LinkedIn discussions frame it as bringing Cilium's data plane behaviour closer to what security teams expect from modern service meshes.
This comes after a longer history of community debate, including a Reddit thread where one user described earlier Cilium architectures as forcing operators to "undermine cluster security" when trying to fit them into strict mTLS models. This indicates that the project is now responding directly to earlier criticism.
Ztunnel Integration: Service Mesh Without Sidecars
The release has a new beta integration of Ztunnel. Ztunnel enables transparent encryption and authentication of TCP connections between workloads without needing sidecar proxies. In the 1.19 release materials, the maintainers describe how namespaces can be enrolled into Ztunnel so that workloads can gain mutual authentication without application changes, again bringing Cilium closer to service-mesh ideals.
There is an implied rethink of earlier design choices in the decision to disable the existing mutual authentication feature by default and to point users needing mTLS towards the Ztunnel path. Other similar projects, like Istio, still rely on sidecar-based deployment. Comments from practitioners on Reddit emphasise the appeal of lighter-weight approaches that reduce per-pod overhead and configuration complexity, even if they are still in beta.
Safer Multi-Cluster Policy Defaults
There's a change in default semantics for multi-clustered setups when network policies do not specify a cluster. In Cilium 1.19.0, such selectors now default to allowing traffic only from the local cluster. This reduces the risk that a misconfigured policy will unintentionally expose services across a Cluster Mesh deployment.
The release also introduces multi-level DNS wildcard matches and the option for Cilium to return ICMPv4 "Destination unreachable" responses when policies deny connections. Together, these aim to make policies both more expressive and easier to debug.
Kafka protocol match fields and the ToRequires and FromRequires policy fields have been deprecated to remove underused complexity. This helps operators focus on patterns actually deployed at scale.
Multi-Pool IPAM Goes Stable
From an operational perspective, the promotion of Multi Pool IPAM to stable status has received positive feedback, especially from users working in large or segmented address spaces. In this release, Multi Pool IPAM is documented as working with both IPsec and direct routing, and is ready for broader production use.
Users on Reddit who previously reported that Cilium's advanced features were "a lot of work to get in place and running well" now have a clearer path to allocate addresses across multiple pools. This is critical in hybrid or multi-tenant clusters.
The addition of IPv6 as a tunnel-underlay option in dual-stack clusters and more granular control over IP masquerading are often mentioned in the same discussions. These changes increase the range of topologies that Cilium can support without resorting to fragile workarounds.
Enhanced Observability with Hubble
Observability improvements in Hubble, Cilium's observability component, comprise the final cluster of changes that appear repeatedly in community commentary. Hubble now allows tracing packets using IP options for specific flows and filtering traffic in the command line by encryption status. It can also tag drop events with the exact network policy that caused them.
These changes address long-standing complaints that eBPF-based data planes can be difficult to reason about during incidents. The ability to see exactly which policy dropped a packet transforms debugging from guesswork into a deterministic process.
Cilium 1.19.1 is available now, and more details are on the Cilium website.
Looking Forward: Cilium's Next Decade
The ten-year milestone represents more than just longevity. It demonstrates how a project can evolve from a networking plugin to a comprehensive security and observability platform. The focus on stricter encryption modes, safer multi-cluster defaults, and enhanced observability shows a project that has listened to its community and adapted to real-world security requirements.
As organizations continue to adopt Kubernetes at scale and push workloads into more regulated environments, Cilium's evolution from a simple CNI to a full-fledged network security platform positions it well for the next decade of cloud-native infrastructure.
The dominance in production environments, combined with the stabilization of contributions and the expansion into AI workloads and heterogeneous environments, suggests that Cilium has found a sustainable model for growth. The project's ability to balance innovation with stability, while maintaining backward compatibility, has earned it the trust of some of the largest deployments in the world.
For operators running large clusters or those in regulated industries, Cilium 1.19 offers concrete improvements in security posture and operational visibility. For the broader Kubernetes ecosystem, it represents another step toward making zero-trust networking the default rather than the exception.

Comments
Please log in or register to join the discussion