Cloudflare has implemented support for ASPA (Autonomous System Provider Authorization), a new cryptographic standard that enhances Internet routing security by validating the path data takes across networks.
Cloudflare has announced support for ASPA (Autonomous System Provider Authorization), a new cryptographic standard designed to make Internet routing safer by verifying the path data takes across networks to reach its destination and preventing traffic from traversing unreliable or untrusted networks.

ASPA is an RPKI-based security mechanism that validates the AS_PATH (the chain of networks a route announcement traverses), thereby reducing route leaks and some classes of hijacks. The goal is to improve Internet reliability and reduce accidental or malicious traffic detours.
How ASPA Works
When data travels across the Internet, it keeps a running log of every network it passes through. ASPA provides networks with a way to officially publish a list of their authorized upstream providers within the RPKI system. This allows any receiving network to look at the AS_PATH, check the associated ASPA records, and verify that the traffic only traveled through an approved chain of networks.
Mingwei Zhang, principal systems engineer at Cloudflare, and Bryton Herdes, principal network engineer at Cloudflare, explain that ASPA detects route detours by validating the expected hierarchical structure of Internet routing. In a normal, "valley-free" topology, traffic moves up from a customer to one or more upstream providers, may traverse a single peer link at the top tier, and then moves down through providers to the destination customer.
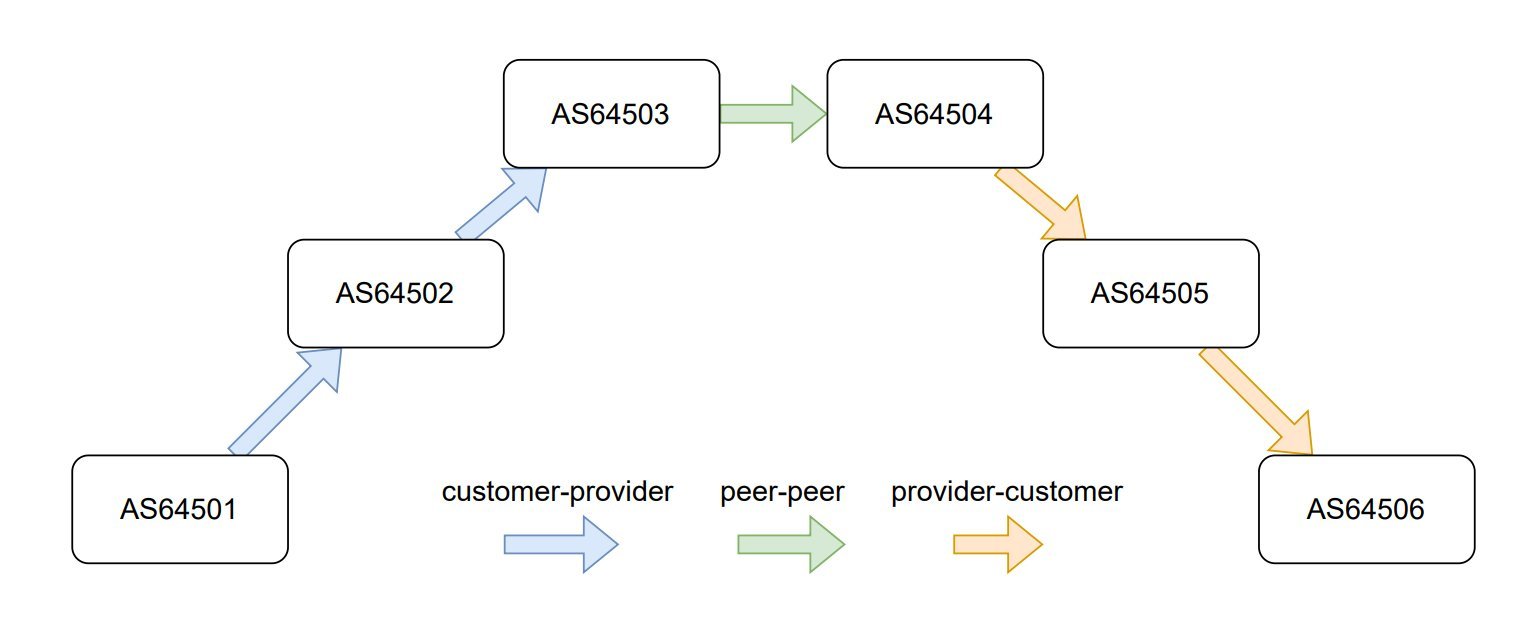
This customer-to-provider ascent, optional peer crossing, and provider-to-customer descent form the standard policy-compliant path. By verifying this structure, ASPA can detect when traffic has taken an abnormal route.
The Need for Enhanced BGP Security
The Border Gateway Protocol (BGP) is essential for routing traffic across the Internet but lacks native path validation, leaving it susceptible to route leaks and hijacks. Although RPKI and Route Origin Authorizations (ROAs) strengthen route origin validation, they do not verify the end-to-end path.
ASPA provides network operators with a cryptographic method to declare their authorized providers, allowing receiving networks to verify that an AS path conforms to this expected structure. This is particularly important because while RPKI validates that a network is allowed to announce a specific IP prefix, it doesn't validate whether the path taken to reach that prefix is legitimate.
Current Adoption and Tools
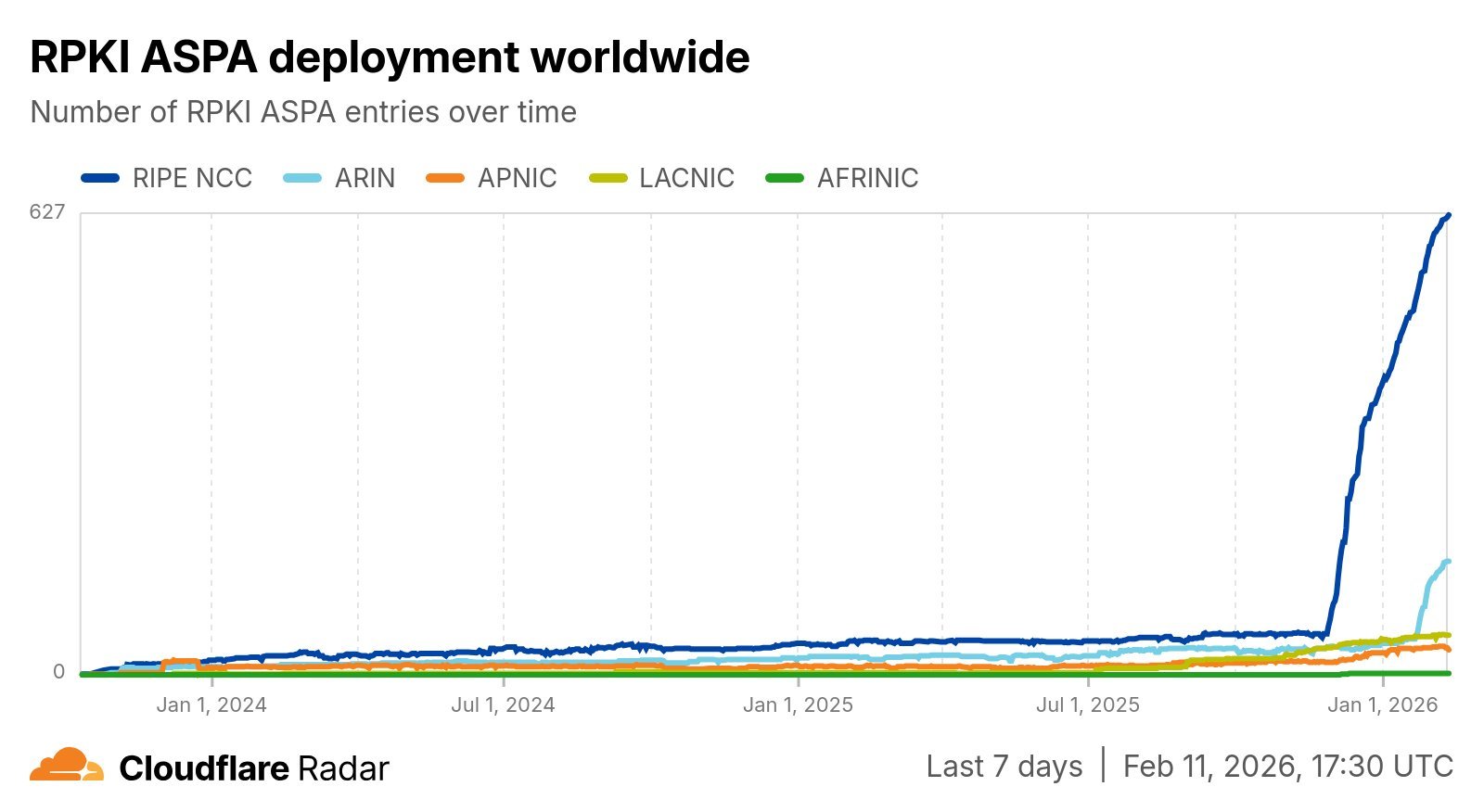
While the specific IETF standard remains in draft, Cloudflare notes that ARIN and RIPE NCC already support ASPA object creation, and routing software such as OpenBGPD and BIRD includes ASPA validation. Cloudflare has also added tools to Cloudflare Radar to track how widely ASPA is being adopted, so network operators can see who's using it and how paths are validated.
Last year, NIST released open-source test tools and datasets to facilitate testing and experimentation with emerging BGP security and resilience mechanisms, including the ability to evaluate router implementations of ASPA specifications.
Real-World Impact
In the recent Venezuela BGP route leak incident, Cloudflare notes that ASPA would have helped networks detect and reject the abnormal path announcements by verifying whether the observed AS path matched the expected provider-authorization relationships, something that origin validation alone could not do.
Implementation Challenges
Zhang and Herdes warn that while ASPA is becoming a reality, it will be a long road to actually providing significant value on the Internet. Changes are needed to RPKI Relaying Party (RP) packages, signer implementations, RTR (RPKI-to-Router protocol) software, and BGP implementations to actually use ASPA objects and validate paths with them.
Cloudflare is not alone in this effort. In the "AWS secures internet routing with RPKI plus security checks" article published last year, the team at AWS writes: "Although ASPA is still being standardized, we are committed to using it and all tools at our disposal to continue to make the internet a safe and reliable place for everyone."
Looking Forward
With ASPA finally becoming a reality, the Internet community has its cryptographic upgrade for Internet path validation. However, widespread adoption will require coordination across the entire networking ecosystem, from RPKI infrastructure providers to router vendors to network operators.
The implementation of ASPA represents a significant step forward in Internet security, addressing a fundamental weakness in BGP that has been exploited in numerous high-profile incidents over the years. As more networks adopt this standard and the supporting infrastructure matures, the Internet should become more resilient against both accidental route leaks and deliberate hijacking attempts.

Comments
Please log in or register to join the discussion