Criminal IP and Securonix ThreatQ have announced a strategic integration that brings exposure-based threat intelligence directly into security operations workflows, enabling faster analysis and more effective response to threats.
In an increasingly complex threat landscape, security teams are constantly seeking ways to enhance their threat intelligence capabilities without disrupting existing workflows. The recent integration between Criminal IP and Securonix ThreatQ addresses this challenge head-on, bringing exposure-based IP intelligence directly into the ThreatQ platform to accelerate analysis and response.
Enhanced Context Through Integration
Unlike traditional threat intelligence feeds that primarily focus on known malicious indicators, Criminal IP provides visibility into how assets and infrastructure are exposed across the internet. By embedding this data into ThreatQ, organizations can incorporate real-world context into investigations without disrupting established processes.
"This integration enables organizations to bring IP reputation and exposure intelligence directly into the ThreatQ platform, supporting faster analysis and more effective response throughout the investigation lifecycle," said Byungtak Kang, CEO of Criminal IP. "By integrating our intelligence into existing workflows, security teams can improve visibility and make more informed decisions without adding operational complexity."
Automated Intelligence Enrichment at Scale
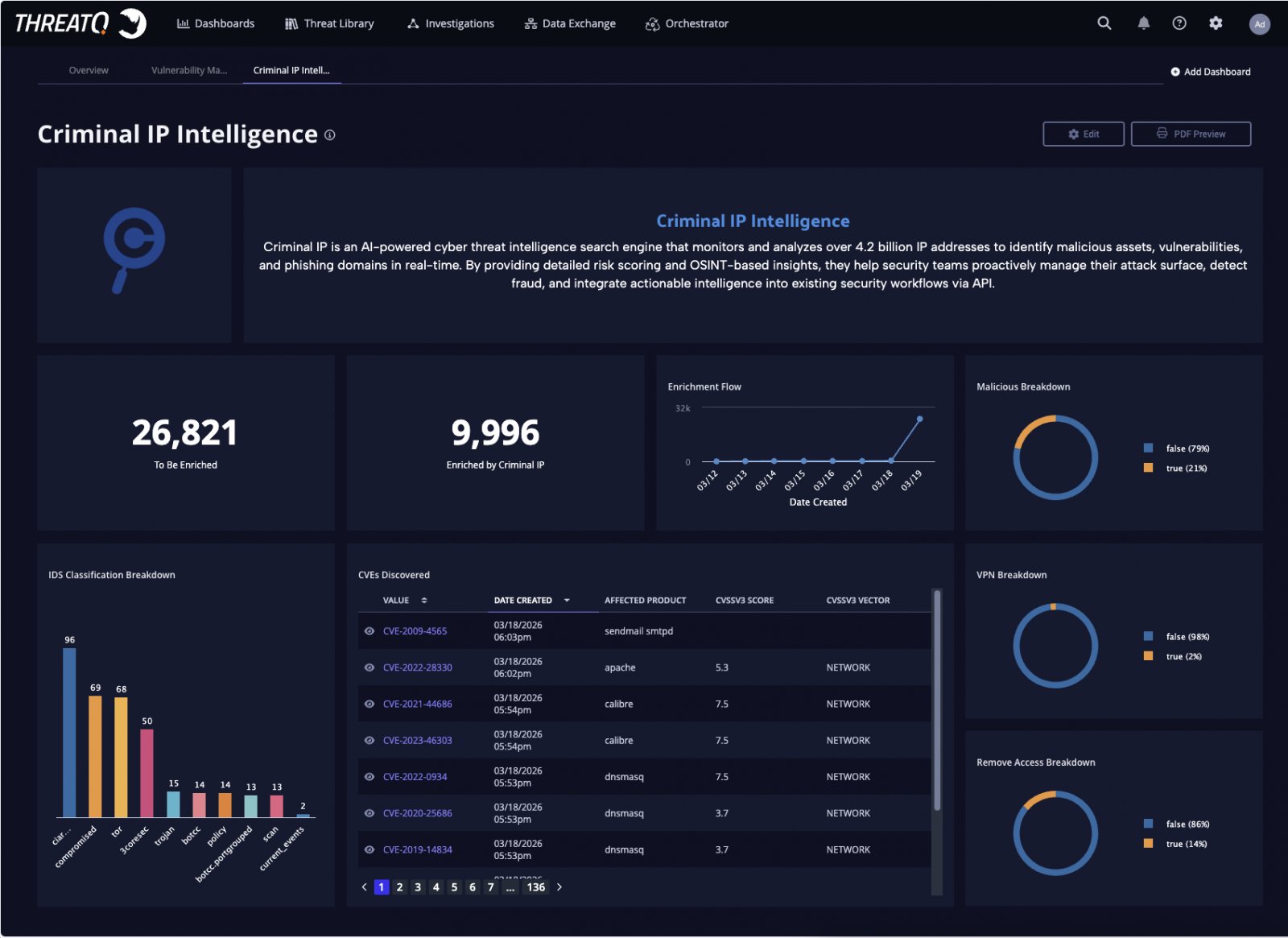
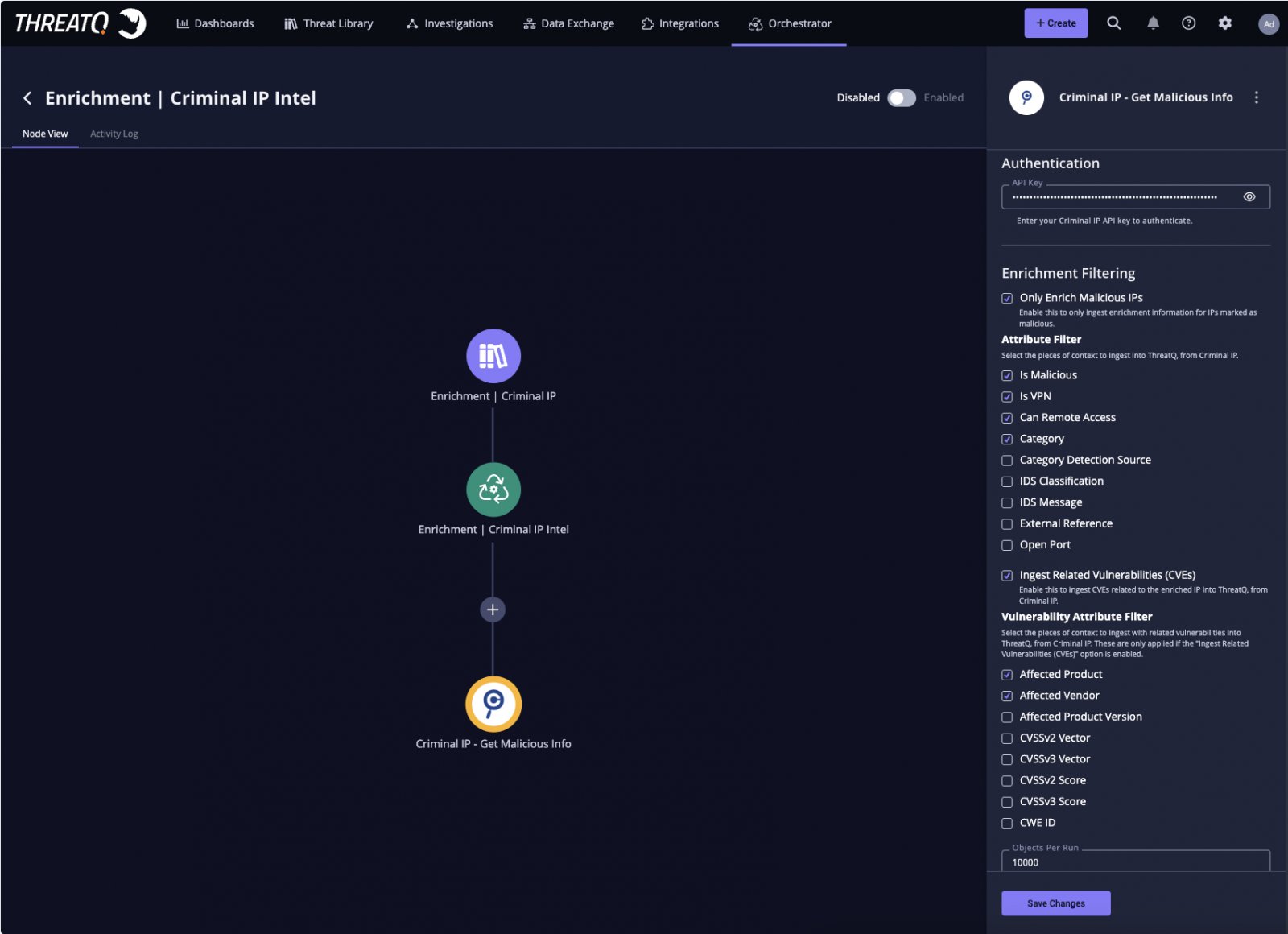
Within the integrated environment, Criminal IP's threat intelligence APIs automatically enrich incoming IP indicators in ThreatQ with contextual data including:
- Maliciousness scoring
- VPN and proxy detection
- Remote access exposure
- Open ports
- Known vulnerabilities
Powered by ThreatQ's data-driven orchestration engine, organizations can configure automated workflows that continuously evaluate incoming indicators against Criminal IP's threat database. This ensures that threat context remains current without requiring manual analyst effort, supporting faster triage and more consistent prioritization.
Real-Time Investigation Capabilities
The integration allows analysts to access Criminal IP intelligence directly within the ThreatQ interface, enabling real-time validation of suspicious IP activity without switching tools. By combining exposure data with infrastructure-level insights, teams can assess risk more effectively within their existing workflows.
Analysts can perform on-demand Criminal IP lookups directly from indicator detail views or investigation boards, providing immediate access to additional context during active investigations. Criminal IP further enhances ThreatQ's investigation graph by revealing relationships between IP addresses, associated infrastructure, and attack activity, helping analysts better understand connections and patterns across threats.
Intelligence-Driven Prioritization and Response
By integrating Criminal IP's intelligence into ThreatQ's scoring framework, organizations can align risk evaluation with their specific operational environment. This enables more precise prioritization and supports more effective decision-making during investigations.
Enriched data can be visualized through dashboards, providing clearer visibility into maliciousness trends, VPN usage, and risk distribution across indicators. This visual representation helps security teams quickly identify patterns and focus their efforts where they're needed most.
Expanding Visibility with Exposure Intelligence
The integration highlights the growing importance of exposure-based intelligence in modern threat analysis. By continuously monitoring and analyzing internet-facing assets and IP infrastructure, Criminal IP provides differentiated visibility that extends beyond traditional indicator-based approaches.
"This collaboration strengthens the role of IP intelligence at critical points of investigation and decision-making," said Scott Sampson, Chief Revenue Officer, Securonix. "By combining ThreatQ's orchestration and prioritization capabilities with Criminal IP's real-time threat data, organizations can accelerate enrichment processes, reduce manual workloads, and focus on the most relevant threats within their environment."
Implementation Considerations
For organizations looking to implement this integration, several practical considerations should be kept in mind:
Assess Current Workflows: Evaluate how IP indicators are currently processed within ThreatQ to identify the best points for integration.
Configure Automated Enrichment: Set up automated enrichment rules based on organizational priorities and risk tolerance.
Customize Scoring Models: Adjust ThreatQ's scoring framework to incorporate Criminal IP's metrics in alignment with specific business needs.
Train Security Teams: Ensure analysts understand how to leverage the integrated intelligence effectively within their existing workflows.
Monitor Performance: Continuously evaluate the impact of the integration on investigation efficiency and response times.
Broader Implications
This partnership represents a significant step toward more operationalized threat intelligence. By integrating exposure-based intelligence directly into security workflows, organizations can reduce the time spent on manual enrichment and focus on high-priority threats.
The integration also demonstrates a broader industry trend toward more contextual and actionable threat intelligence. Rather than simply providing lists of known malicious IPs, solutions like Criminal IP offer deeper insights into how infrastructure is exposed and potentially vulnerable, enabling more proactive security measures.
For organizations interested in implementing this integration, additional information is available through the Criminal IP integration page and the Securonix ThreatQ documentation.
As the threat landscape continues to evolve, partnerships like this between specialized intelligence providers and broader security platforms will become increasingly important. By embedding intelligence directly into operational workflows, security teams can maintain effectiveness without adding complexity to their already demanding workloads.

Comments
Please log in or register to join the discussion