A sophisticated Vietnamese-linked operation has been using Google's AppSheet platform as a phishing relay to compromise over 30,000 Facebook accounts, which are then sold through an illicit storefront.
A newly discovered Vietnamese-linked cyber operation has been leveraging Google's AppSheet platform as a sophisticated phishing relay to compromise approximately 30,000 Facebook accounts in what researchers have codenamed 'AccountDumpling.' The campaign represents a concerning evolution in social engineering tactics, abusing legitimate platforms to bypass security measures while harvesting valuable credentials and personal information.
The Campaign Mechanics
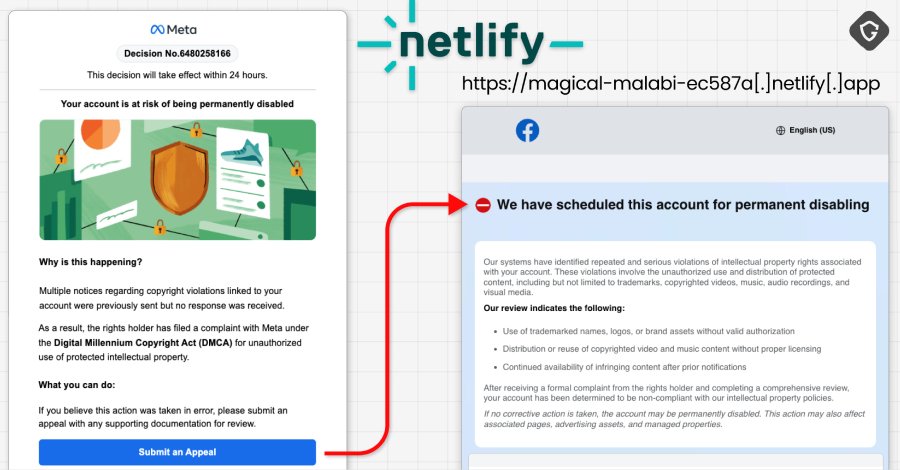
The attacks begin with phishing emails specifically targeting Facebook Business account owners, with messages impersonating Meta Support. These emails create a false sense of urgency, claiming recipients must submit an appeal or risk permanent account deletion. The emails originate from Google AppSheet addresses ("[email protected]"), which allows them to bypass many spam filters and appear more legitimate to unsuspecting victims.
"What we found wasn't a single phishing kit," explained Shaked Chen, security researcher at Guardio. "It was a living operation with real-time operator panels, advanced evasion, continuous evolution and a criminal-commercial loop that quietly feeds on the same accounts it helps steal back."
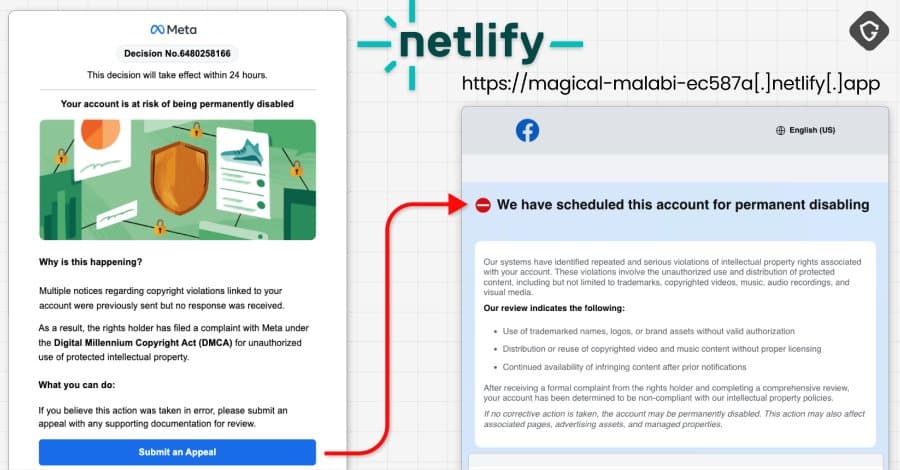
Once victims click on the links, they're directed to sophisticated fake web pages designed to harvest credentials. The campaign has evolved significantly since similar operations were first reported by KnowBe4 in May 2025, with attackers now employing multiple sophisticated lures designed to induce "Meta-related panic." These include:
- Account disablement notifications
- Copyright complaints
- Verification review requests
- Executive recruitment offers
- Facebook login alerts
Multi-Platform Attack Infrastructure
The phishing operation spans multiple platforms, demonstrating a level of technical sophistication that goes beyond typical phishing campaigns:
Netlify-hosted Facebook help center pages that enable account takeover attacks while collecting dates of birth, phone numbers, and government-issued ID photos. This data is forwarded to attacker-controlled Telegram channels.
Blue badge evaluation lures that guide victims to Vercel-hosted "Security Check" or "Meta | Privacy Center" pages. These are gated by bogus CAPTCHA checks before directing users to phishing landing pages that collect contact details, business information, credentials (after forced retry), and two-factor authentication codes.
Google Drive-hosted PDFs masquerading as account verification instructions. These PDFs, created using free Canva accounts, direct users to submit passwords, 2FA codes, government ID photos, and browser screenshots through html2canvas.
Fake job offers impersonating major companies like WhatsApp, Meta, Adobe, Pinterest, Apple, and Coca-Cola to build rapport with recipients and lure them to attacker-controlled sites.
The Scale and Impact
The Telegram channels associated with the first three clusters have been found to contain approximately 30,000 victim records. Most affected users are located in the U.S., Italy, Canada, the Philippines, India, Spain, Australia, the U.K., Brazil, and Mexico. Many victims have been completely locked out of their own accounts, with attackers potentially changing passwords and security settings.
The compromised accounts represent valuable commodities in underground markets, with access to business identities, advertising reputation, and even account recovery services all becoming tradable assets. The operation demonstrates how social media accounts have evolved from simple personal assets to complex business tools with significant monetary value.
Attribution and Motivation
Researchers traced the operation back to Vietnamese threat actors through metadata in PDF documents created using Canva, which listed a Vietnamese name "PHẠM TÀI TÂN" as the files' author. Further open-source intelligence revealed a website ("phamtaitan[.]vn") offering digital marketing services.
"Taken together, they form a consistent picture of a large, Vietnamese-based, mega operation," Chen noted. "This campaign is bigger than a single AppSheet abuse. It's a window into the dark market around stolen Facebook assets, where access, business identity, ad reputation, and even account recovery have all become tradable commodities."

Defensive Recommendations
For organizations and individuals using Facebook Business accounts, security experts recommend several defensive measures:
Implement multi-factor authentication on all Facebook accounts, especially business accounts with administrative privileges.
Train employees to recognize sophisticated phishing attempts, particularly those creating urgency or claiming to be from official support channels.
Verify communications directly through official channels rather than clicking links in suspicious emails.
Monitor account activity for unauthorized changes or login attempts from unfamiliar locations.
Regularly audit third-party applications connected to Facebook accounts and remove unnecessary ones.
Use email filtering solutions that can detect and block emails originating from abused legitimate platforms like AppSheet.
Establish an incident response plan for account compromise scenarios, including procedures for regaining access and notifying affected parties.
The AccountDumpling campaign serves as a stark reminder of how threat actors continue to innovate their techniques, abusing legitimate platforms to carry out malicious activities. As social media platforms become increasingly integrated with business operations, the potential impact of such compromises grows significantly, making robust security practices more critical than ever.
Comments
Please log in or register to join the discussion