Security
AI‑Boosted GREYVIBE Campaigns Target Ukraine, Blurring Lines Between State‑Backed Espionage and Cybercrime
5/29/2026

Security
From $5 Attacks to Botnet-Powered Platforms: Inside the DDoS-as-a-Service Market
5/29/2026

Cybersecurity
Russian‑linked GREYVIBE cyber‑espionage group weaponises ChatGPT across the attack chain
5/29/2026

Security
ThreatsDay Bulletin: Rising Sophistication in Cyber Attacks Demands Enhanced Defenses
5/29/2026

Security
Three SOC Practices That Cut Incident Risk Early
5/27/2026
Security
AI Chatbots Weaponized to Redirect Users to Cryptojacking Malware
5/27/2026
Security
Cloudflare's Security Infrastructure: Protecting the Internet from Evolving Threats
5/26/2026

Cybersecurity
BlackBerry anchors Asian cybersecurity push with new Malaysian hub
5/24/2026

Cybersecurity
ShinyHunters Resurfaces After Brief Silence, Claims New Victims Including Major Telecom and Healthcare Providers
5/24/2026
Security
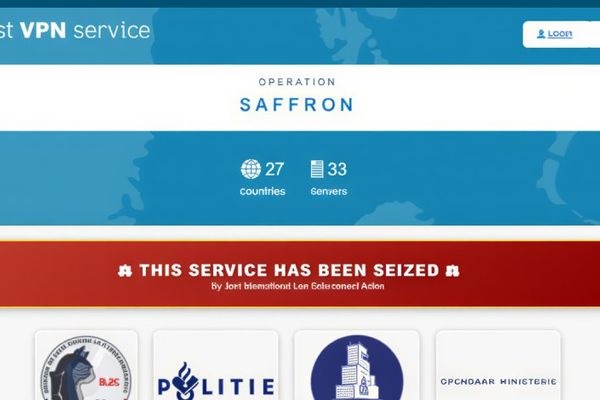
First VPN Dismantled in Global Takedown After Serving 25 Ransomware Gangs
5/22/2026

Security
Showboat Linux Malware Targets Middle East Telecom with SOCKS5 Proxy Backdoor
5/21/2026
Security
Cloudflare Security Block Highlights Routine Web Protection Mechanisms
5/21/2026

Security
Trapdoor Android Ad Fraud Scheme Leveraged 455 Malicious Apps to Flood 659 Million Daily Bid Requests
5/19/2026