Hackers are actively exploiting a critical remote code execution vulnerability in Marimo, an open-source Python notebook platform, just hours after its public disclosure. The flaw allows unauthenticated attackers to gain full shell access and steal credentials.
A critical remote code execution vulnerability in Marimo, a popular open-source Python notebook platform, is now under active exploitation by threat actors who are targeting exposed instances to steal credentials and sensitive data.

Vulnerability Details
The flaw, tracked as CVE-2026-39987, affects Marimo versions 0.20.4 and earlier, allowing remote code execution without authentication. GitHub assigned it a critical severity score of 9.3 out of 10.
The vulnerability stems from the WebSocket endpoint /terminal/ws exposing an interactive terminal without proper authentication checks. This design flaw enables connections from any unauthenticated client, providing direct access to a full interactive shell running with the same privileges as the Marimo process.
Marimo is widely used by data scientists, ML/AI practitioners, researchers, and developers building data applications or dashboards. The project has garnered significant adoption with 20,000 GitHub stars and 1,000 forks.
Timeline of Exploitation
According to researchers at cloud-security company Sysdig, the exploitation timeline unfolded rapidly:
- Within 12 hours: 125 IP addresses began reconnaissance activity
- Less than 10 hours: First exploitation attempt observed
- April 8: Marimo publicly disclosed the flaw
- April 12: Version 0.23.0 released to address the vulnerability
Attack Methodology
Sysdig's analysis reveals a methodical attacker employing a hands-on approach rather than automated scripts. The attack sequence demonstrates sophistication and focus on high-value objectives:
- Initial validation: Attacker connected to
/terminal/wsendpoint, executed a scripted sequence to confirm remote command execution, then disconnected - Manual reconnaissance: Reconnected and issued basic commands (
pwd,whoami,ls) to understand the environment - Directory navigation: Attempted to explore the filesystem structure
- Credential harvesting: Immediately targeted
.envfiles, extracting environment variables including cloud credentials and application secrets - SSH key probing: Continued searching for SSH keys and other authentication materials
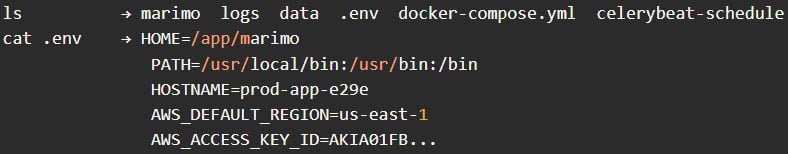
The entire credential access phase was completed in less than three minutes, according to Sysdig's report. Notably, the attacker returned approximately one hour later for a second exploitation session using the same exploit sequence.
Attack Characteristics
Several aspects of the attack pattern suggest a sophisticated threat actor:
- Focused objectives: The attacker concentrated on stealing
.envcredentials and SSH keys rather than deploying persistence mechanisms - No cryptomining: Unlike many opportunistic attacks, no cryptominers or backdoors were installed
- Stealth approach: The quick, targeted nature of the attacks suggests an attempt to avoid detection
- Manual operation: The methodical, hands-on approach indicates human operators rather than fully automated scripts
Mitigation and Protection
Marimo users should take immediate action to protect their instances:
Immediate Actions
- Upgrade immediately: Install Marimo version 0.23.0, which addresses the vulnerability
- Block WebSocket endpoint: If upgrading isn't immediately possible, block or disable access to the
/terminal/wsendpoint entirely - Restrict network access: Use firewall rules to limit external access to Marimo instances
Security Monitoring
- Monitor WebSocket connections: Watch for unusual activity to
/terminal/ws - Review logs: Check for unauthorized access attempts and successful connections
- Network segmentation: Ensure Marimo instances aren't exposed to untrusted networks unnecessarily
Post-Exploitation Response
- Rotate credentials: Immediately rotate all exposed secrets, API keys, and authentication materials
- Audit access: Review logs for signs of unauthorized access
- Incident response: If compromise is suspected, follow established incident response procedures
Context and Impact
The rapid exploitation timeline—just 10 hours from public disclosure to active attacks—highlights the critical nature of this vulnerability and the speed at which threat actors operate. This pattern mirrors other recent high-profile vulnerabilities where public disclosure has led to immediate exploitation attempts.
Marimo's popularity in data science and AI communities makes this particularly concerning, as many organizations rely on the platform for sensitive data processing and model development. The ability to execute arbitrary code without authentication could lead to data exfiltration, model theft, or lateral movement within networks.
Related Security Trends
This incident is part of a broader pattern of critical vulnerabilities being exploited shortly after disclosure. Recent examples include:
- Flowise RCE vulnerability: Also seeing active exploitation in AI workflow platforms
- Fortinet FortiClient EMS flaw: Critical enterprise security software vulnerability under attack
- Langflow flaw: AI workflow hijacking attempts
- BeyondTrust RCE flaw: Ransomware groups exploiting remote code execution
These incidents underscore the importance of rapid patch management and network segmentation for exposed services, particularly in the AI/ML and data science ecosystem where platforms like Marimo play a crucial role.
Expert Recommendations
Security experts emphasize several key principles for organizations using Marimo or similar platforms:
- Defense in depth: Never rely on a single security control
- Network isolation: Keep development and data science platforms isolated from production networks
- Principle of least privilege: Limit permissions and network access to only what's necessary
- Regular auditing: Continuously monitor for unusual access patterns and potential compromises
- Incident preparedness: Have response plans ready for when—not if—critical vulnerabilities are discovered
The Marimo vulnerability serves as a stark reminder that even popular, well-maintained open-source projects can contain critical flaws, and the window between public disclosure and exploitation is shrinking rapidly. Organizations must maintain vigilant security practices and rapid response capabilities to protect their data science and AI infrastructure.

Comments
Please log in or register to join the discussion