German police have identified two Russian nationals as the leaders of the notorious GandCrab and REvil ransomware operations, responsible for over $40 million in damages and 130 extortion cases targeting German companies.
German authorities have identified two Russian nationals as the masterminds behind two of the most notorious ransomware operations in recent years, GandCrab and REvil, responsible for hundreds of attacks and tens of millions in damages.
The Identification
The Federal Police in Germany (BKA) has identified 31-year-old Daniil Maksimovich Shchukin and 43-year-old Anatoly Sergeevitsch Kravchuk as the leaders of these ransomware operations between 2019 and 2021. According to BKA's disclosure, the two acted as the heads of both ransomware groups "from at least the beginning of 2019 until at least July 2021."
Shchukin operated under the monikers UNKN/UNKNOWN for years, posting on cybercrime forums and speaking as a representative of the ransomware operation. The German authorities say that Shchukin and Kravchuk participated in at least 130 extortion cases targeting companies specifically in Germany.
Following these attacks, at least 25 victims paid Shchukin and his co-conspirators $2.2 million in ransom, while the total financial damage caused by them is estimated in excess of $40 million.

The GandCrab Connection
GandCrab started in early 2018 and quickly became one of the most successful ransomware operations of its time. Its original leader decided to retire in June 2019, after claiming to have earned $2 billion from ransom payments. However, the leader cashed out with $150 million, which they claimed to have invested in legal businesses.
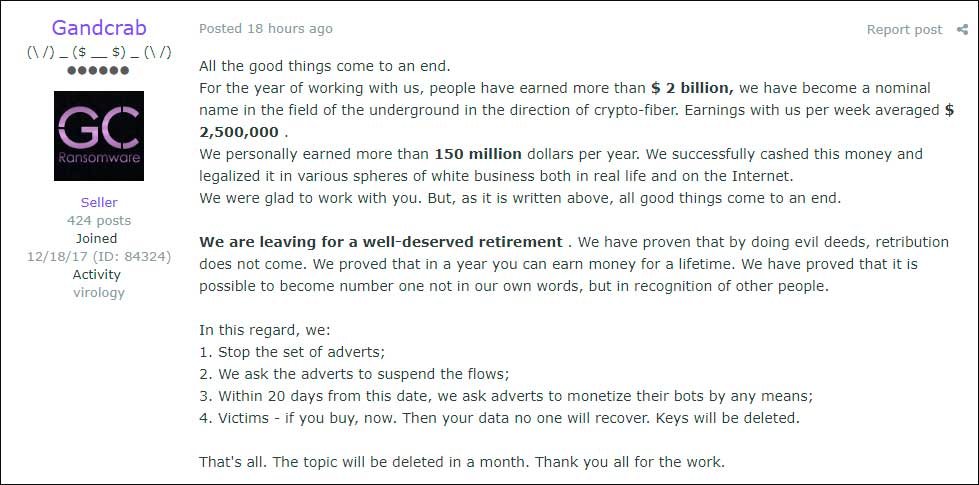
This retirement announcement marked a pivotal moment in ransomware history. The GandCrab leader's decision to exit the criminal world was unusual for ransomware operators, who typically continue their operations until law enforcement intervention.
The Birth of REvil
Soon after GandCrab's retirement, a new operation called REvil emerged, following the affiliate model established by GandCrab through advertising and building partnerships with cybercriminals. REvil, also known as Sodinokibi, was formed from previous GandCrab affiliates and operators who had already learned the successful tactics and started to apply them to their operations.
REvil later added public leak sites and ran data auctions to pressure victims, representing an evolution in ransomware tactics. Notable victims include multiple Texas local governments, computer giant Acer, and the Kaseya supply-chain attack that impacted around 1,500 downstream victims.
The Kaseya Attack and Aftermath
Following the massive Kaseya hack in July 2021, REvil took a two-month break during which law enforcement breached their servers and started to monitor operations. Multiple infrastructure disruptions were recorded at the time, and in mid-January 2022, Russia arrested more than a dozen REvil gang members, who were released in 2025 after time served on carding charges.
The Kaseya attack represented one of the most significant supply chain compromises in ransomware history, affecting potentially thousands of businesses through a single managed service provider vulnerability.
Current Status and International Cooperation
It is unclear if either Shchukin or Kravchuk joined other ransomware operations following REvil's demise in 2021. BKA believes that Shchukin and Kravchuk are now in Russia and asks the public to share any information that could lead to their whereabouts.
Relevant entries were also created on the EU's Most Wanted portal. The police shared several images, including tattoo photos, to help track down the two threat actors and bring them to justice.
This case highlights the increasing international cooperation in combating cybercrime, with German authorities taking the lead in identifying these high-profile ransomware operators. The publication of identifying information and images represents a significant escalation in the public pressure campaign against ransomware operators.
The Broader Context
The identification of these individuals comes amid a broader crackdown on ransomware operations globally. Recent operations like Interpol's Synergia have taken down 1,300 servers used for cybercrime, while police arrests of Phobos ransomware suspects and the seizure of 8Base sites demonstrate the ongoing efforts to dismantle these criminal networks.
For businesses and organizations, this development serves as a reminder of the persistent threat posed by ransomware groups and the importance of maintaining robust cybersecurity defenses, including regular backups, employee training, and incident response planning.
The case also underscores the challenges of international law enforcement cooperation, particularly when suspects are believed to be operating from countries that may not extradite to Western nations. Despite these challenges, the identification of these individuals represents a significant victory in the ongoing battle against cybercrime.

Comments
Please log in or register to join the discussion