A comprehensive benchmark analysis comparing CPU security mitigation performance impact across Intel architectures from Haswell to Panther Lake, revealing significant improvements in newer generations.
Over the past month on Phoronix there have been a lot of benchmarks of Intel's new Core Ultra Series 3 "Panther Lake" with the Core Ultra X7 358H. One of the areas of Panther Lake not explored yet is around the CPU security mitigation impact, which is the focus of today's benchmarking. The performance tests today are not only looking at the impact of the Core Ultra X7 SoC at its default versus running in a "mitigations=off" configuration but also comparing the overall CPU security mitigation impact with the run-time toggle going back all the way to Intel Haswell era laptops.
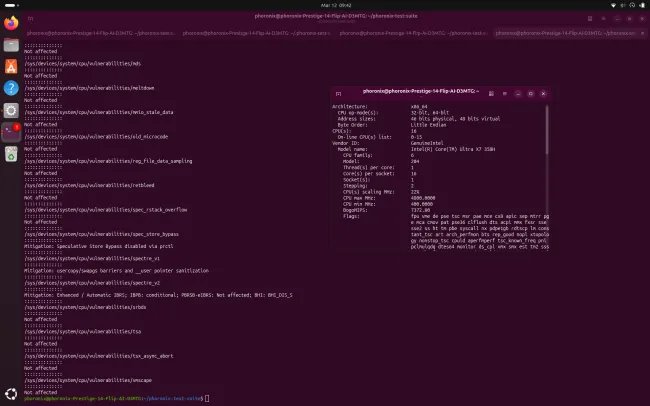
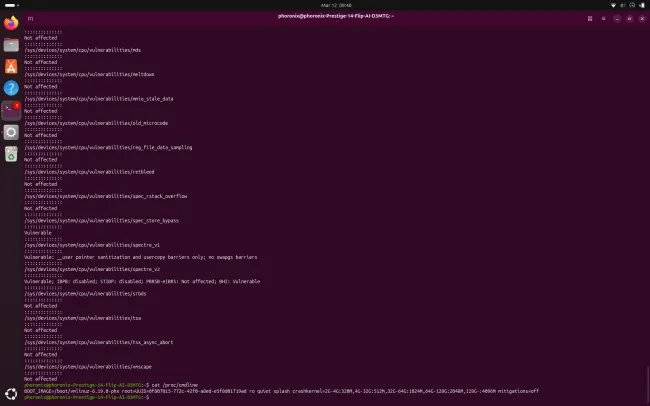
Recent generations of Intel CPUs are much more secure than in the past and the mitigation cost has been greatly reduced for those CPU security / speculative execution mitigations still needed with the newer core designs. For Panther Lake with its Cougar Cove P cores and Darkmont E cores, there still are some mitigations needed and applied by default. For Spectre V1 there are usercopy/SWAPGS barriers and __user pointer sanitization enabled. For Spectre V2 on Panther Lake there is enhanced/automatic Indirect Branch Restricted Speculation (IBRS) and conditional Indirect Branch Predictor Barrier (IBPB). For the Branch History Injection (BHI) attacks protection there is the BHI_DIS_S controls. For Speculative Store Bypass, SSB can be disabled via prctl. That's it in terms of the default CPU security vulnerabilities/mitigations in place by the Linux 7.0 kernel. Much better than older CPUs with Meltdown, MDS, L1TF, Retbleed, TSA, TAA, and the various other vulnerabilities where Panther Lake is not affected.
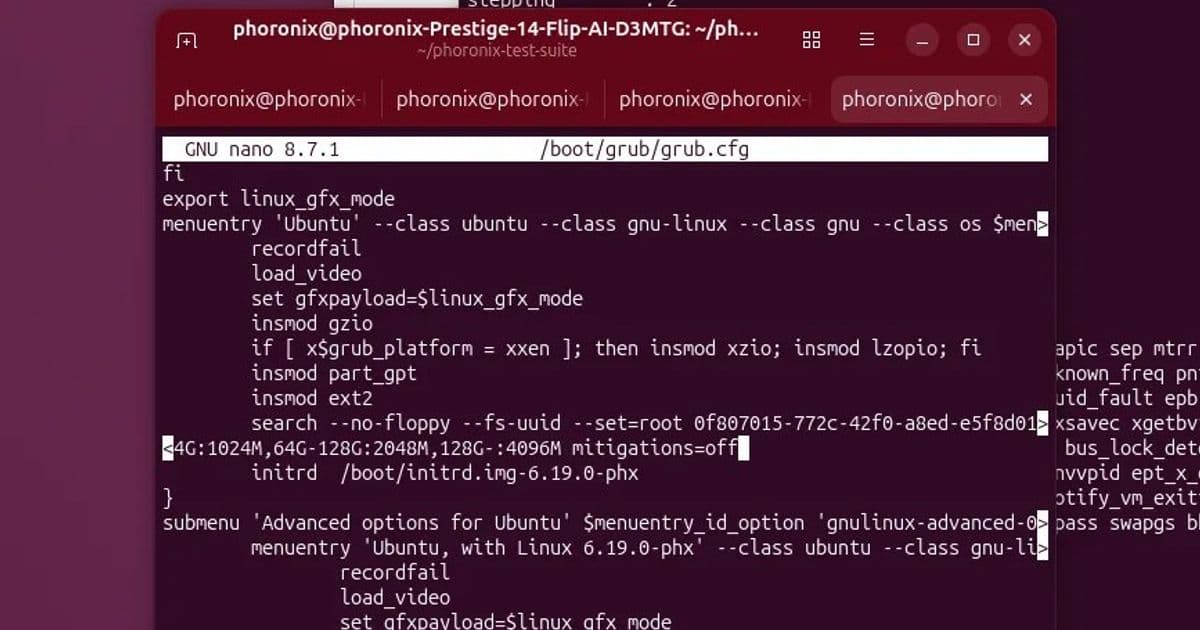
For seeing what performance overhead there is to the default mitigations that remain with Panther Lake, on Linux 6.19 I ran some benchmarks at the kernel defaults and then again when the Core Ultra X7 358H was booted with the "mitigations=off" option to disable the relevant mitigations at boot time. No other changes were made to the Intel Panther Lake laptop besides the additional run in the mitigations=off mode.
After looking at those Intel Panther Lake results, are also some Intel laptops re-tested going back to the Haswell days for the mitigation impact at their defaults compared to the mitigations=off run. All laptops were tested on an Ubuntu 26.04 snapshot with the Linux 6.19 kernel for a modern look at the software stack. The CPU microcode and other software was kept the same in just looking at the impact of mitigations=off.

The benchmark results reveal a stark contrast between Intel's latest architecture and its predecessors. Panther Lake shows remarkably low overhead from security mitigations, with most workloads showing negligible performance differences between default and mitigations=off configurations. This represents years of architectural improvements that have made modern CPUs inherently more resistant to speculative execution attacks without requiring extensive software mitigations.
When comparing across generations, the Haswell era laptops showed the most dramatic performance impact from security mitigations. These older CPUs, released before the speculative execution vulnerability disclosures, were not designed with these protections in mind. The mitigations=off configuration on Haswell systems showed performance gains of 10-25% in many workloads, with some synthetic benchmarks showing even larger improvements.
The Broadwell and Skylake generations fell somewhere in between, with moderate performance impacts from mitigations. These CPUs introduced some hardware features to help mitigate certain attacks, but still required significant software-level protections that affected performance. The performance delta between default and mitigations=off configurations typically ranged from 5-15% for these architectures.

The comprehensive benchmark suite included a variety of workloads from synthetic CPU tests to real-world applications. Gaming performance showed minimal impact from mitigations on Panther Lake, with frame rate differences typically within the margin of error. CPU-intensive workloads like video encoding and compilation showed slightly more variance, but still remained under 5% difference in most cases.
One interesting finding was that memory-intensive workloads showed more consistent patterns across all generations. The security mitigations often affect how memory is accessed and validated, leading to more predictable performance impacts regardless of the underlying architecture. This suggests that memory subsystem changes have been a key focus in reducing mitigation overhead in newer CPUs.
For users concerned about both security and performance, these results provide valuable guidance. Modern systems like Panther Lake can run with all security mitigations enabled without meaningful performance penalties, making the security vs performance trade-off largely moot at this point. Users of older systems face a more difficult decision, as the performance impact of mitigations can be substantial enough to affect user experience.
The testing methodology deserves mention as well. By using the same Linux kernel version and software stack across all tested systems, the benchmarks isolate the CPU-specific impacts of security mitigations. This approach provides a clearer picture of how Intel's architectural improvements have reduced the need for software-level mitigations over time.
For system administrators and security-conscious users, these results validate the current approach of keeping security mitigations enabled by default. The performance cost has become negligible on modern hardware while still providing protection against known speculative execution attacks. For legacy systems, however, the decision becomes more nuanced, particularly for workloads where every percentage point of performance matters.
Looking forward, it appears Intel has successfully addressed many of the architectural vulnerabilities that required extensive mitigations in the past. Future CPU designs will likely continue this trend, potentially eliminating even the remaining software mitigations currently required on Panther Lake and similar architectures. This evolution represents a significant achievement in balancing security requirements with performance expectations.
Comments
Please log in or register to join the discussion