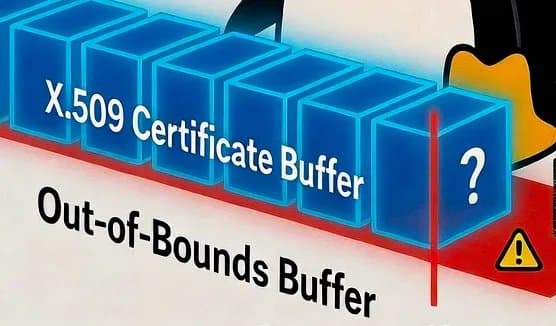
A critical out-of-bounds access vulnerability in Linux's X.509 certificate parsing code, present since kernel 6.4, has been patched just before the Linux 7.0 release. The flaw allowed unprivileged users to trigger kernel crashes or potential information leaks by submitting specially crafted certificates through the keyrings API.
A critical security vulnerability affecting Linux systems has been patched in the upcoming Linux 7.0 kernel release, closing a three-year window during which unprivileged users could potentially crash the kernel or cause information leaks through specially crafted X.509 certificates.
The vulnerability, tracked as an out-of-bounds (OOB) access issue, existed in the Linux kernel's X.509 certificate parsing code since the Linux 6.4 release in 2023. The flaw allowed any unprivileged user to submit a maliciously crafted certificate through the kernel's keyrings API, triggering memory access violations that could lead to denial of service conditions or, in more severe scenarios, information disclosure.
Technical Details of the Vulnerability
The specific issue arose in the certificate parsing logic when handling Basic Constraints or Key Usage extensions. The vulnerable code attempted to read the first byte of these extensions before validating their length, creating a classic buffer over-read scenario. This type of vulnerability is particularly concerning in kernel space because it operates with elevated privileges and can affect system stability.
Lukas Wunner, who authored the fix, explained the technical root cause in the patch submission: "[Leo Lin] reports an out-of-bounds access when parsing a certificate with empty Basic Constraints or Key Usage extension because the first byte of the extension is read before checking its length."
Impact and Severity
While the vulnerability could be triggered by any unprivileged user on a system, the practical impact was somewhat limited compared to more severe kernel flaws. According to the patch analysis, the information leak potential was minimal—primarily exposing memory contents rather than sensitive data. However, the ability to cause kernel panics or denial of service conditions remained a significant concern, especially for multi-user systems or shared hosting environments.
Out-of-bounds access vulnerabilities in kernel code are particularly problematic because they operate at the highest privilege level and can potentially be escalated to more serious exploits. The fact that this could be triggered without any special privileges made it especially noteworthy from a security perspective.
Timeline and Patch Distribution
The vulnerability was responsibly disclosed to the kernel development team, with proof-of-concept code demonstrating the attack vector. The fix was implemented just in time for inclusion in the Linux 7.0 stable kernel release, which was expected to ship on the same day the patch was merged.
Beyond the mainline kernel, the security team has marked this patch for back-porting to all currently supported stable kernel branches dating back to Linux 6.4. This includes:
- Linux 6.6 LTS
- Linux 6.12 LTS
- Linux 6.18 LTS
- Linux 6.19
This comprehensive back-porting strategy ensures that the vast majority of production Linux systems running supported kernel versions will receive the security fix, protecting enterprise deployments and long-term support distributions.
Mitigation and System Administration
For system administrators and DevOps engineers, the immediate priority is ensuring that systems are updated to kernel versions containing this fix once they become available through distribution channels. Most major Linux distributions will back-port the security fix to their stable kernel packages, even for versions that may not receive the full Linux 7.0 feature set.
Organizations running custom kernels or maintaining their own kernel builds should prioritize applying this patch, given the ease with which unprivileged users could trigger the vulnerability. The attack vector through the keyrings API means that any user with local shell access could potentially exploit the flaw, making it relevant for shared hosting providers, educational institutions, and enterprise environments with multiple user accounts.
Broader Context in Kernel Security
This vulnerability highlights the ongoing challenges in maintaining kernel security, particularly in complex subsystems like certificate parsing that must handle a wide variety of input formats and edge cases. The three-year window between the introduction of the bug and its discovery demonstrates how even well-maintained codebases can harbor subtle security issues that only become apparent under specific conditions.
The responsible disclosure process, involving proof-of-concept code and coordinated patch development, represents best practices in security vulnerability management. By providing developers with concrete examples of how the vulnerability could be triggered, the discoverer enabled rapid and accurate patch development.
As Linux continues to evolve with each major release, security vulnerabilities like this serve as important reminders of the need for rigorous code review, comprehensive testing, and prompt patch management, especially for critical infrastructure components that form the foundation of modern computing systems.
Comments
Please log in or register to join the discussion