A 23-year-old Tennessee man was sentenced to 30 months in prison for selling access to tens of thousands of compromised DraftKings accounts, part of a larger credential-stuffing scheme that netted over $2 million in profits.
A 23-year-old Tennessee man has been sentenced to 30 months in federal prison for his role in a massive credential-stuffing operation that compromised nearly 68,000 DraftKings accounts in November 2022.
Kamerin Stokes of Memphis was convicted for selling access to tens of thousands of hacked DraftKings accounts, according to court documents. The accounts were initially hijacked by Nathan Austad (online alias "Snoopy") and Joseph Garrison, who used credentials stolen from multiple data breaches to launch a coordinated attack on the sports betting platform.
The scale of the attack
The credential-stuffing campaign was remarkably successful, compromising approximately 68,000 DraftKings accounts. Prosecutors revealed that Austad and Garrison used automated tools to test stolen username and password combinations across the platform, exploiting the common practice of password reuse across multiple services.
Once inside these accounts, the attackers added new payment methods and made small deposits to verify their validity. They then withdrew all available funds, resulting in approximately $635,000 stolen from roughly 1,600 compromised accounts.
The criminal enterprise
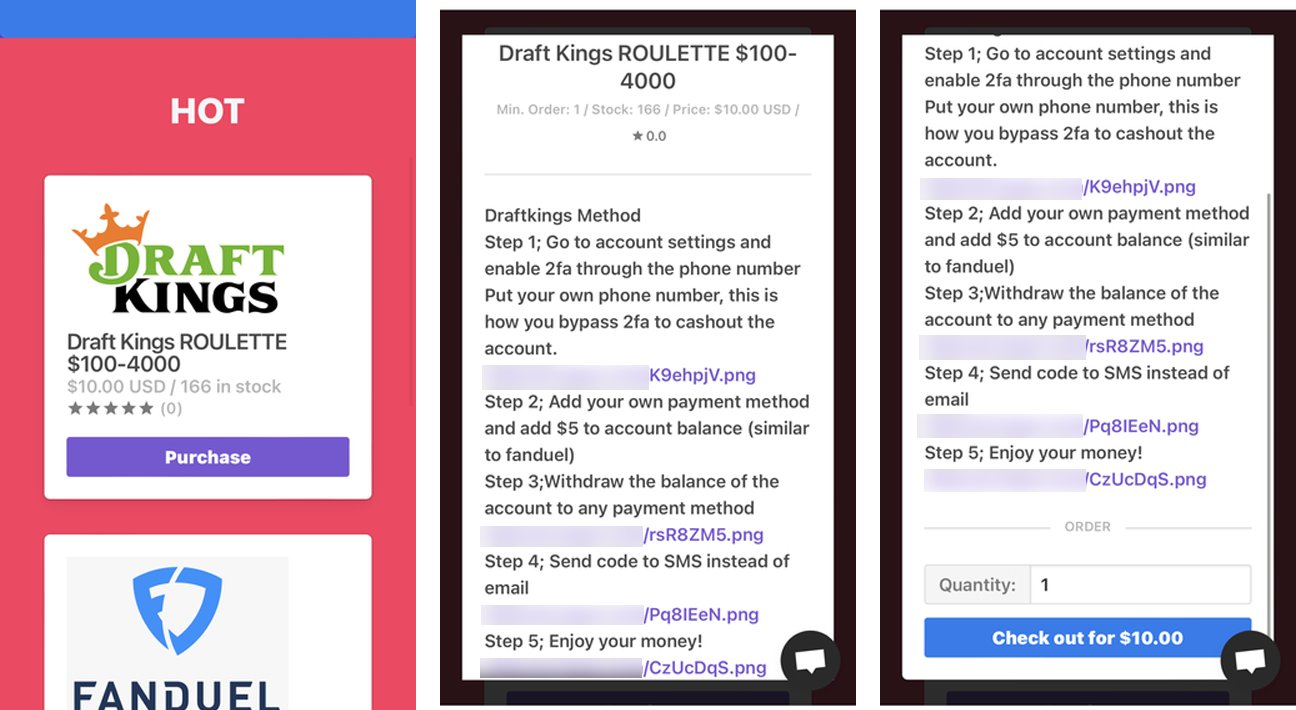
Austad and Garrison didn't just steal funds directly—they built a lucrative business model around selling access to these compromised accounts. Court records show they generated over $2.1 million by operating their own "shops" that sold hijacked accounts not only for DraftKings but also for other platforms including FanDuel and Chick-fil-A.
Stokes entered the picture as a bulk buyer, purchasing large quantities of compromised accounts from Austad and Garrison's operations. He then resold these accounts through his own shop, expanding the criminal network's reach and profits.
Audacious continuation despite prosecution
What makes this case particularly notable is Stokes' brazen behavior following his arrest and guilty plea. While awaiting trial, he reopened his criminal enterprise with a new tagline: "fraud is fun."
Prosecutors noted that Stokes admitted to running similar shops for three years and specifically stated he relaunched the operation because he "gotta pay my attorneys"—referring to his legal representation in this very case.
This flagrant violation of his pretrial release conditions led to his rearrest and remand into federal custody.
The broader impact
DraftKings was forced to refund hundreds of thousands of dollars to affected customers after the attack. The company's response highlighted the challenges platforms face when dealing with credential-stuffing attacks, particularly when attackers can add new payment methods and verify them with minimal deposits.
Sentencing and restitution
In addition to his 30-month prison sentence, Stokes received three years of supervised release. He was also ordered to pay substantial financial penalties:
- $1,327,061 in restitution to victims
- $125,965.53 in forfeiture
The case serves as a stark reminder of the ongoing threat posed by credential-stuffing attacks and the sophisticated criminal ecosystems that have developed around selling access to compromised accounts. Security experts continue to emphasize the importance of unique passwords for each service and enabling multi-factor authentication wherever possible.
The prosecution of Stokes and his associates demonstrates federal authorities' commitment to pursuing not just the initial hackers but also the secondary markets that facilitate the monetization of stolen account access.

Comments
Please log in or register to join the discussion