Microsoft has eliminated unauthenticated domain enumeration via the Azure Access Control Service metadata endpoint, following similar changes to Exchange Online Autodiscover.
Microsoft has quietly eliminated another method for unauthenticated tenant domain enumeration in Microsoft 365, closing a loophole that security researchers and attackers alike had been using to map organizational domains.
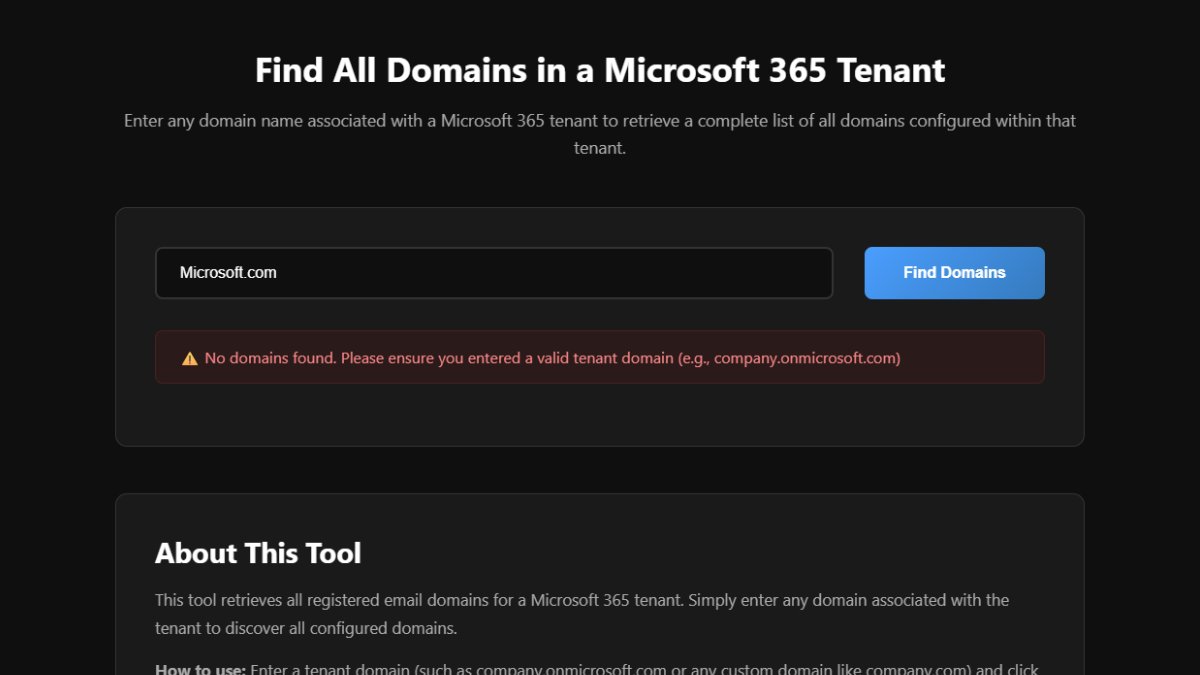
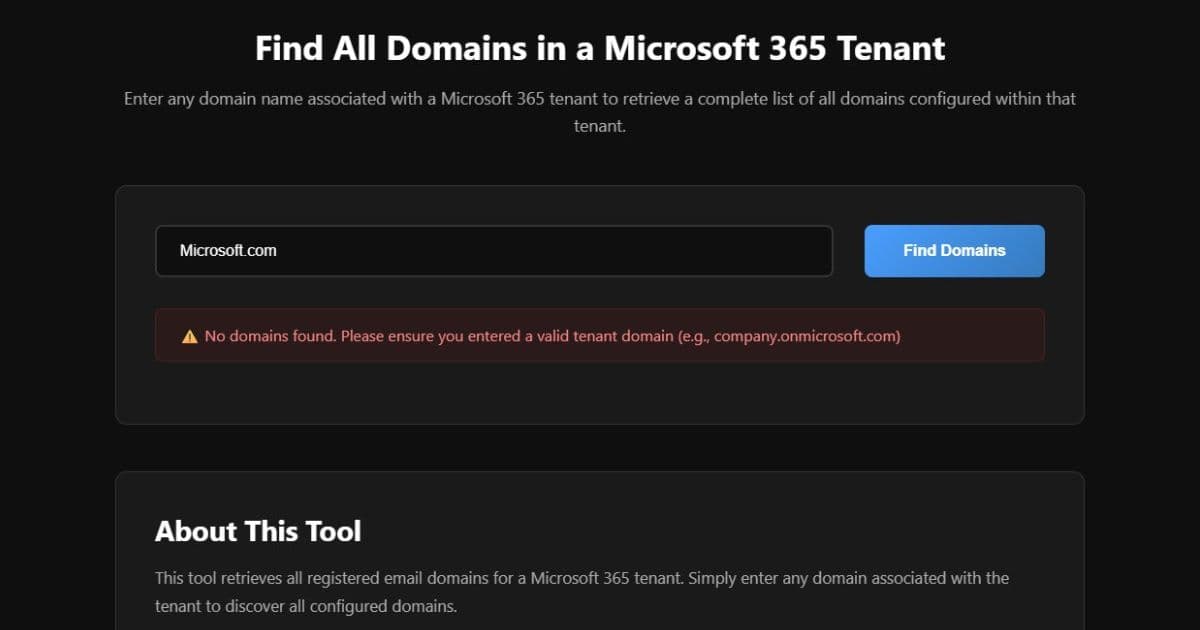
Previously, services could query the https://accounts.accesscontrol.windows.net/${tenantName}/metadata/json/1 endpoint without authentication. This would return a JSON response containing an allowed_audiences array that listed all verified domains tied to a specific organization's Microsoft 365 tenant. Tools like TenantDomainFinder leveraged this endpoint to perform reconnaissance on target organizations.
The change is significant because unauthenticated domain enumeration provides attackers with valuable intelligence for targeting organizations. By identifying all verified domains associated with a tenant, attackers could:
- Map an organization's complete domain footprint
- Identify lesser-known or secondary domains that might have weaker security controls
- Evade security measures by targeting specific domains
- Build more comprehensive phishing campaigns
Microsoft has now scrubbed this data from the unauthenticated response entirely. The allowed_audiences array returns empty when queried without authentication, effectively killing the utility of this endpoint for intelligence gathering. No amount of header manipulation or client spoofing will force the backend to reveal this data.
This update follows a similar recent change to the Exchange Online Autodiscover service, which historically powered the Get-FederationInformation cmdlet. Together, these changes signal a clear defensive strategy by Microsoft to shut down domain mapping across all legacy endpoints.
For legitimate administrators who need to query domains, Microsoft recommends using Microsoft Graph instead, which requires authentication with the "Domain.Read.All" permission. This approach ensures that only authorized users can access domain information.
From a security standpoint, this is a positive change. While it may frustrate some security researchers and penetration testers who relied on these endpoints for legitimate testing, the reduction in attack surface is worthwhile. The security community will likely continue searching for alternative methods to enumerate domains while authenticated, though Microsoft's ongoing efforts suggest they're committed to closing these gaps systematically.
The change demonstrates Microsoft's evolving approach to security hardening in Microsoft 365, moving away from legacy endpoints that expose sensitive information and toward authenticated, permission-based access controls.
Comments
Please log in or register to join the discussion