
Security
GlassWorm Malware Takedown Disrupts Developer Supply Chain Attack Infrastructure
5/27/2026

Security
Iranian Hackers Deploy MiniFast and MiniJunk V2 via Phishing and SEO Poisoning
5/26/2026
Vulnerabilities
DAEMON Tools Supply Chain Attack Compromises Official Installers with Malware
5/6/2026

Security
Sophisticated EtherRAT Campaign Impersonates Admin Tools via GitHub Facades
5/1/2026

Vulnerabilities
WordPress Plugin Suite Hacked to Push Malware to Thousands of Sites
4/16/2026

Security
New AgingFly Malware Targets Ukrainian Government and Healthcare in Sophisticated Cyber Campaign
4/16/2026

Security
Over 100 Chrome Web Store Extensions Exposed in Large-Scale Data Theft Campaign
4/15/2026

Vulnerabilities
JanelaRAT Malware Targets Latin American Banks with 14,739 Attacks in Brazil in 2025
4/13/2026
Security
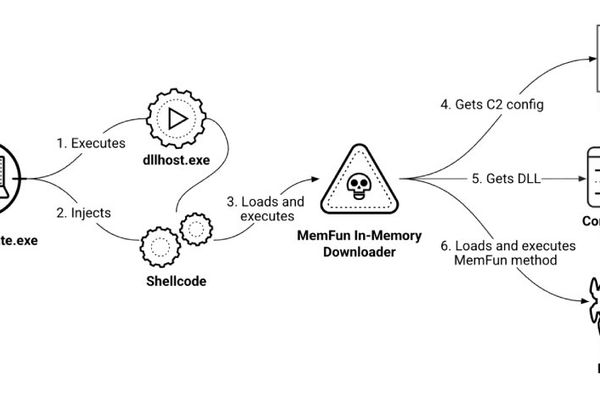
Chinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
3/13/2026

Vulnerabilities
North Korean Hackers Publish 26 npm Packages Hiding Pastebin C2 for Cross-Platform RAT
3/2/2026

Security
Fake Next.js Job Interviews Target Developers with Backdoor Malware
2/26/2026

Security
Fake 7-Zip Site Turns PCs Into Residential Proxy Nodes
2/14/2026

Security
Claude LLM artifacts abused to push Mac infostealers in ClickFix attack
2/13/2026