Security researchers discover coordinated attack stealing Google tokens, hijacking accounts, and deploying backdoors through malicious browser extensions
Security researchers have uncovered a large-scale campaign involving more than 100 malicious Chrome extensions that are actively stealing user credentials, hijacking accounts, and deploying backdoors through the official Chrome Web Store.
Coordinated Attack Infrastructure The campaign, discovered by application security company Socket, operates through a centralized command-and-control infrastructure hosted on a Contabo VPS server. The threat actors have organized their malicious extensions under five distinct publisher identities, distributing them across multiple categories including Telegram sidebar clients, slot machine and Keno games, YouTube and TikTok enhancers, text translation tools, and various utilities.
The researchers identified evidence pointing to a Russian malware-as-a-service (MaaS) operation, based on code comments related to authentication and session theft mechanisms.
Multiple Attack Vectors The malicious extensions employ several sophisticated techniques to compromise user data:
- 78 extensions inject attacker-controlled HTML into the user interface using the
innerHTMLproperty - 54 extensions leverage
chrome.identity.getAuthTokento collect victim email addresses, names, profile pictures, Google account IDs, and OAuth2 Bearer tokens - 45 extensions contain hidden backdoor functions that execute on browser startup, fetching commands from the C2 server and capable of opening arbitrary URLs without user interaction
Telegram Session Hijacking
One particularly severe extension steals Telegram Web sessions every 15 seconds by extracting session data from localStorage and the Telegram Web session token. The extension can also receive inbound messages that clear the victim's localStorage, overwrite it with threat actor-supplied session data, and force-reload Telegram, effectively swapping the victim into a different Telegram account without their knowledge.
Additional Malicious Activities Beyond credential theft, the campaign includes extensions that:
- Strip security headers and inject ads into YouTube and TikTok
- Proxy translation requests through malicious servers
- Deploy staged infrastructure for non-active Telegram session theft
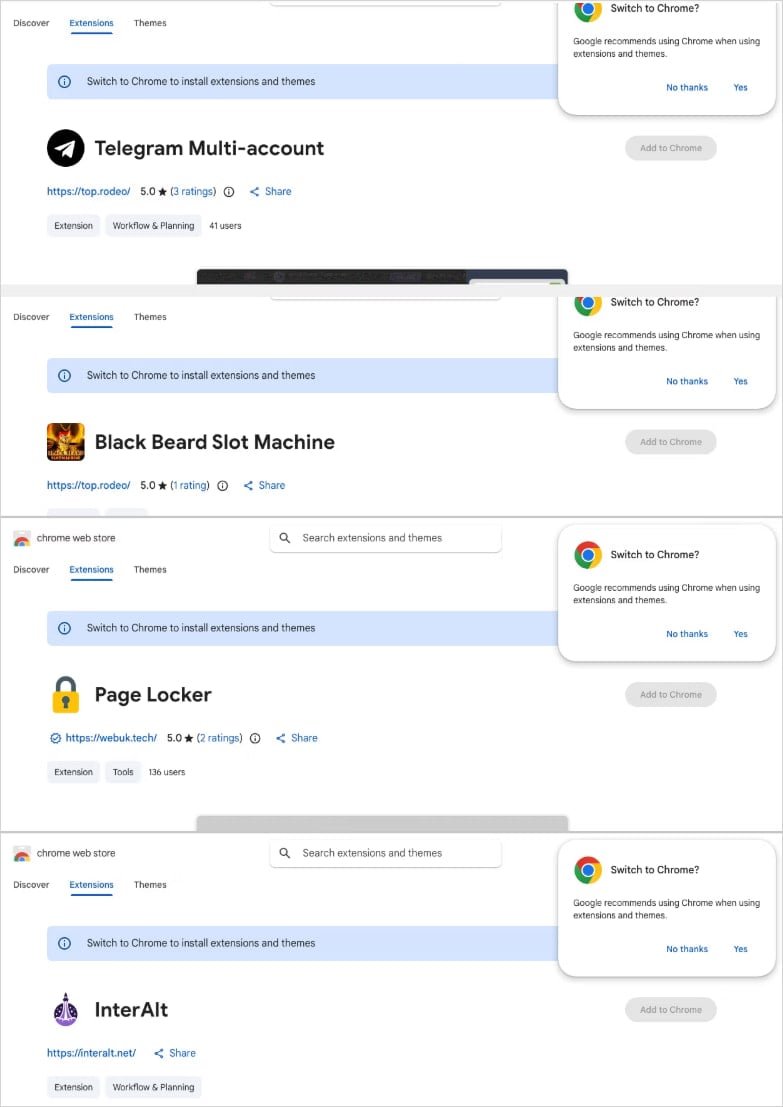
Ongoing Threat Despite Socket notifying Google about the campaign, the malicious extensions remain available on the Chrome Web Store at the time of publication. BleepingComputer confirmed that many of the extensions listed in Socket's report are still accessible.
Protection Measures Users are strongly advised to:
- Review their installed Chrome extensions against the IDs published by Socket
- Immediately uninstall any matching extensions
- Exercise caution when installing new extensions, particularly those offering enhanced functionality for popular platforms
This discovery highlights the ongoing challenges in securing browser extension ecosystems and the sophisticated methods attackers use to distribute malware through official channels.
The incident follows other recent security concerns in the browser extension ecosystem, including the QuickLens Chrome extension that stole cryptocurrency and demonstrated ClickFix attack techniques.

Comments
Please log in or register to join the discussion