North Korean hacking group APT37 has been using Facebook to build trust with targets before delivering RokRAT malware through trojanized software and image files.
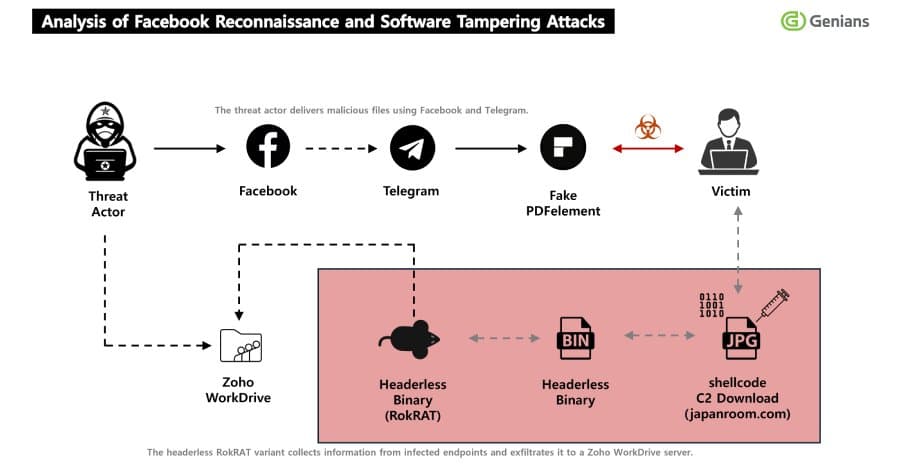
North Korea's APT37 hacking group has launched a sophisticated social engineering campaign using Facebook to deliver RokRAT malware to unsuspecting targets. The campaign, detailed by Genians Security Center (GSC), demonstrates how threat actors are increasingly leveraging social media platforms for initial access before deploying advanced persistent threats.
The Facebook-Based Social Engineering Approach
The attackers created two Facebook accounts with locations set to Pyongyang and Pyongsong, North Korea. These accounts were used to identify and screen potential targets before sending friend requests. Once trust was established through the social media connection, conversations were moved to Facebook Messenger where specific topics were used to lure victims.
"The threat actor used two Facebook accounts with their location set to Pyongyang and Pyongsong, North Korea, to identify and screen targets," the GSC explained. "After building trust through friend requests, the actor moved the conversation to Messenger and used specific topics to lure targets as part of the initial social engineering stage of the attack."
The Pretexting Tactic
Central to this campaign is a technique called pretexting, where attackers create a fabricated scenario to trick users. In this case, targets were convinced they needed to install a dedicated PDF viewer to access encrypted military documents. This psychological manipulation is particularly effective because it plays on the victim's curiosity and perceived need for sensitive information.
The PDF viewer used was actually a tampered version of Wondershare PDFelement. When launched, this trojanized software triggered the execution of embedded shellcode, providing the attackers with an initial foothold in the victim's system.
Multi-Stage Attack Chain
The infection process follows a carefully orchestrated multi-stage approach:
- Initial Contact: Facebook friend requests from seemingly legitimate accounts
- Trust Building: Conversations moved to Messenger with topic-specific lures
- Delivery: ZIP file containing trojanized software sent via Telegram
- Execution: Tampered PDF viewer installs and runs embedded shellcode
- C2 Communication: Connection established with compromised legitimate infrastructure
- Final Payload: JPG image delivers the RokRAT malware
Compromised Infrastructure for Command and Control
One of the most concerning aspects of this campaign is the use of legitimate but compromised infrastructure for command and control operations. The attackers weaponized the website associated with the Seoul arm of a Japanese real estate information service to issue malicious commands and payloads.
This approach makes detection significantly more difficult, as traffic appears to be legitimate web requests rather than suspicious command and control communications. The payload itself is disguised as a JPG image file named "1288247428101.jpg" to further evade detection.
RokRAT Malware Capabilities
Once deployed, RokRAT provides attackers with extensive capabilities:
- Capturing screenshots of infected systems
- Enabling remote command execution via cmd.exe
- Collecting detailed host information
- Performing comprehensive system reconnaissance
- Evading detection by security programs like Qihoo's 360 Total Security
- Disguising malicious traffic to blend with normal network activity
The malware abuses Zoho WorkDrive as its command and control infrastructure, a tactic also observed by Zscaler ThreatLabz in their Ruby Jumper campaign analysis from February 2026.
Campaign Infrastructure Details
The attackers established two specific Facebook accounts for this operation:
- "richardmichael0828"
- "johnsonsophia0414"
Both accounts were created on November 10, 2025, suggesting careful planning and preparation before the campaign began. After moving conversations to Telegram, the attackers delivered ZIP archives containing:
- The trojanized version of Wondershare PDFelement
- Four PDF documents
- A text file with installation instructions
Evolution of APT37's Tactics
According to the GSC analysis, "Its core functionality has remained relatively stable and has been reused repeatedly across multiple operations over time. This shows that RokRAT has focused less on changing its core functionality and more on evolving its delivery, execution, and evasion chain."
This observation highlights an important trend in advanced persistent threat operations: rather than constantly developing new malware capabilities, threat actors are increasingly focusing on improving their delivery mechanisms and evasion techniques to bypass modern security controls.
Protection and Detection Strategies
Organizations can protect against similar campaigns by implementing several key measures:
Social Engineering Defense: Train employees to recognize social engineering attempts, particularly those originating from social media platforms. Verify the identity of contacts before engaging in sensitive conversations or downloading files.
Software Integrity: Implement application whitelisting and verify the integrity of software before installation. Be particularly cautious of software required to view supposedly sensitive documents.
Network Monitoring: Monitor for unusual network traffic patterns, especially communications with unexpected geographic locations or suspicious domains.
Multi-Factor Authentication: Use MFA for all critical accounts to prevent lateral movement even if initial access is achieved.
Security Awareness: Regular training on the latest social engineering tactics and how to identify suspicious requests or files.
The Broader Threat Landscape
This campaign exemplifies how nation-state actors are combining traditional espionage techniques with modern digital platforms. The use of social media for initial access represents a significant evolution in attack methodology, as it allows threat actors to establish trust and gather intelligence before any malicious activity occurs.
The targeting of military-related documents suggests espionage objectives, consistent with APT37's known focus on gathering intelligence from government, military, and defense industry targets. The sophisticated nature of the attack chain, including the use of legitimate infrastructure and file type masquerading, indicates significant resources and technical expertise behind the operation.
As social media continues to be integrated into professional and personal communication, organizations must adapt their security strategies to address these evolving threats. The combination of psychological manipulation through pretexting and technical sophistication through multi-stage malware delivery creates a formidable challenge for defenders.
The APT37 campaign serves as a reminder that even sophisticated targets can be compromised through well-executed social engineering, emphasizing the need for comprehensive security awareness training and robust technical controls to protect against these increasingly complex threats.
Comments
Please log in or register to join the discussion