Recent security breaches in npm highlight critical vulnerabilities in JavaScript package management, raising questions about supply chain security across all package ecosystems.
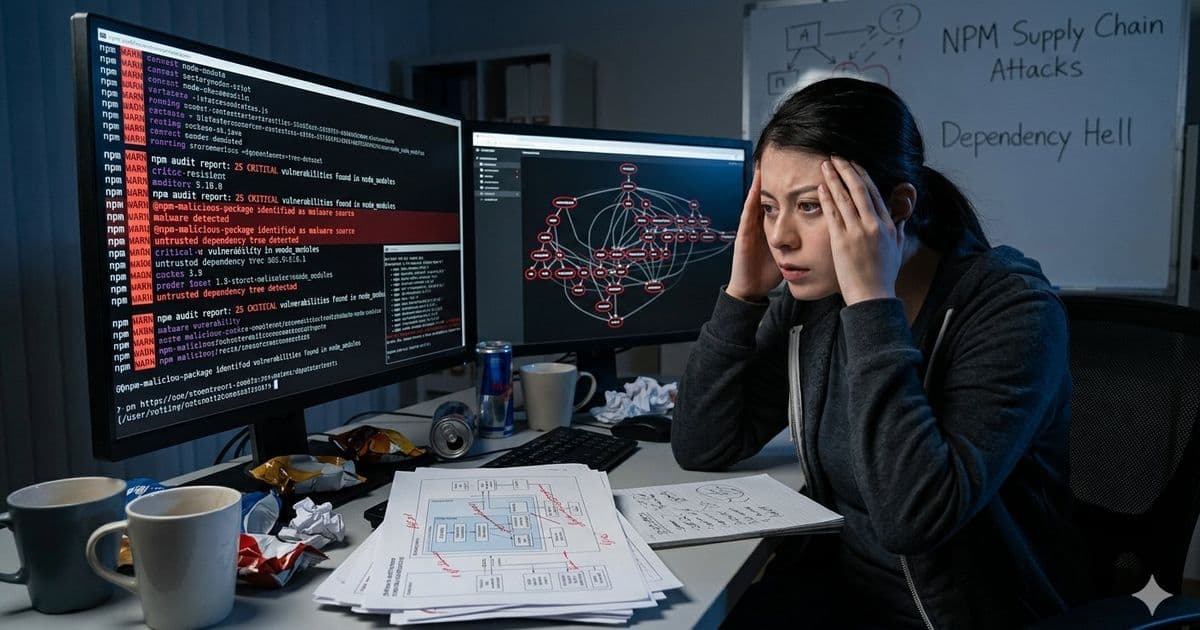
The JavaScript ecosystem faced another significant security breach recently when attackers compromised a long-abandoned utility package in the npm registry, resulting in millions of enterprise applications being compromised and billions of user records exposed. This incident, while not unprecedented in the npm ecosystem, has reignited conversations about package manager security and the risks of dependency management in modern software development.
The compromised package, which had been maintained by a pseudonymous maintainer who had become inactive, was taken over by malicious actors who injected crypto-mining code and remote execution capabilities into the package. When developers worldwide executed npm install, they unknowingly installed this malicious code into their production builds, creating a widespread supply chain attack that affected everything from small startups to large enterprises.
"This is becoming an increasingly common problem in the JavaScript ecosystem," said security researcher Dr. Elena Rodriguez. "The combination of a massive number of packages, many with minimal maintenance, and the default behavior of executing scripts during installation creates a perfect environment for supply chain attacks."
Unlike ecosystems such as Go and Rust, which have built-in package verification and more robust standard libraries, the JavaScript ecosystem has historically relied on a vast network of third-party packages. While this has accelerated development velocity, it has also introduced significant security risks.
"Go's module system uses cryptographic checksums to verify package integrity, and the standard library is comprehensive enough that many third-party packages aren't necessary," explained Go maintainer James Wilson. "We're not immune to supply chain attacks, but the barriers to entry for malicious actors are much higher."
The npm registry has implemented some security measures over the years, including two-factor authentication for package maintainers and the ability to audit dependencies. However, critics argue these measures are insufficient given the scale of the ecosystem.
"npm has made some progress, but the fundamental problem remains: anyone can publish a package with arbitrary installation scripts that execute with the same permissions as the developer," said security consultant Sarah Chen. "Until npm changes this default behavior, these attacks will continue to happen."
Alternative package managers like Yarn and pnpm have introduced some improvements, such as more granular control over script execution and better caching mechanisms. However, they still rely on the same underlying package distribution model.
"Package maintainers need better tools to detect when packages are being transferred or abandoned," suggested npm security lead Marcus Johnson. "We're working on improved verification processes and better communication channels when packages change hands, but this is a complex problem that requires industry-wide collaboration."
For developers, the incident highlights the importance of dependency hygiene. Tools like npm audit, Snyk, and Dependabot can help identify known vulnerabilities, but they can't catch novel attacks like the one described.
"Developers need to be more selective about their dependencies and consider whether packages are truly necessary," advised security expert Dr. Rodriguez. "Sometimes using a smaller, well-maintained library is better than a popular one that hasn't been updated in years."
The broader software industry is beginning to recognize package security as a critical issue. Initiatives like the OpenSSF (Open Source Security Foundation) are working to improve security across open source ecosystems, including package registries.
"Supply chain security is everyone's responsibility," said OpenSSF director Alex Kim. "We need collaboration between package maintainers, registry operators, developers, and security researchers to create a more secure ecosystem."
As the JavaScript ecosystem continues to grow, the challenge of maintaining security while preserving the openness and accessibility that has made it so popular will become increasingly important. The recent npm breach serves as a stark reminder that without significant improvements in package management security, developers and users will continue to bear the brunt of these attacks.
For more information on npm security best practices, developers can refer to the official npm security documentation. For information on dependency auditing tools, the OWASP Dependency-Check provides comprehensive scanning capabilities.
Comments
Please log in or register to join the discussion