OpenClaw, an AI-powered automation framework, has sparked intense security discussions after researchers discovered critical vulnerabilities enabling remote code execution and credential theft through its plugin marketplace. While underground forums show limited active exploitation, the framework's supply chain risks and rapid adoption make it a significant emerging threat requiring immediate attention.
The OpenClaw Hype: Analysis of Chatter from Open-Source Deep and Dark Web
Sponsored by Flare | February 25, 2026
What began as a developer's side project to streamline daily tasks has evolved into a security concern that's capturing attention across both legitimate security research communities and underground forums. OpenClaw, an AI-powered automation framework, has rapidly transitioned from niche developer tool to a topic of intense discussion regarding its potential for supply chain attacks and credential theft.
From Productivity Tool to Security Risk
OpenClaw was created by developer Peter Steinberger as an AI assistance platform designed to handle mundane tasks like email management, scheduling, and thought organization. The framework operates through modular "skills"—user-installable plugins that execute commands on behalf of users. This architecture, while powerful, creates a significant attack surface that security researchers have been quick to identify.
The platform's rapid rise in visibility is evident in threat monitoring data. According to Flare's analysis, OpenClaw-related event volumes showed a dramatic spike in late January 2026, coinciding with increased discussion across security research feeds, Telegram channels, and underground-adjacent forums.
Critical Vulnerabilities Discovered
Security researchers have identified multiple critical vulnerabilities that make OpenClaw an attractive target for supply chain attacks:
CVE-2026-25253 (One-click RCE): Perhaps the most concerning vulnerability allows malicious links to steal authentication tokens and trigger remote code execution without requiring skill installation. Attackers can compromise systems through a single click, bypassing traditional security measures.
Malicious Skill Supply Chain: Hundreds of poisoned skills have been uploaded to ClawHub, OpenClaw's official plugin marketplace. These disguised plugins deliver infostealers, remote access trojans (RATs), and backdoors that appear as legitimate automation tools.
No Skill Sandboxing: Skills execute with full agent and system permissions, allowing malware to access credentials, files, and network resources without restriction. This lack of isolation means that once a malicious skill is installed, it has the same privileges as the automation environment itself.
Prompt Injection Attacks: Attackers can manipulate AI agents through natural language commands, bypassing traditional software vulnerabilities. This represents a new attack vector specific to AI-powered systems.
Token and OAuth Abuse: Stolen or inherited authentication tokens can be leveraged to trigger legitimate API actions, making malicious activity appear authorized and harder to detect.
The Supply Chain Attack Vector
The most significant risk with OpenClaw lies in its plugin ecosystem. The framework's architecture mirrors other plugin-based systems that have historically been targets for supply chain attacks, including browser extensions, package managers like npm and PyPI, and IDE plugin stores.
Once executed, malicious skills harvest credentials, session cookies, and sensitive data from compromised systems. This information is then packaged into stealer logs distributed through underground markets, creating a lucrative ecosystem for attackers.
Underground Discussion vs. Active Exploitation
Analysis of 2,764 collected records from underground forums and Telegram channels reveals an interesting pattern. While OpenClaw mentions total 3,072, ClawDBot (the original name) appears 1,365 times, and MoltBot appears 864 times, the nature of these discussions is telling.
Breaking down the discussion types shows:
- Skills security discussions: 193 mentions
- ClawHub ecosystem references: 110 mentions
- Infostealer references: 53 mentions
- Botnet orchestration: 8 mentions
- DDoS infrastructure: 7 mentions
If OpenClaw were already weaponized at scale for mass exploitation, underground forums would typically show active tool sales, botnet panel discussions, leaked administration interfaces, and established monetization threads. Instead, the conversation consists primarily of security research reports, technical analysis, platform risk speculation, and early-stage experimentation without commercial operations.
Why This Matters Now
OpenClaw sits at the intersection of three major trends: agentic automation platforms, plugin marketplace trust models, and AI-assisted workflow execution. Security researchers tend to detect these risks early, before criminal ecosystems fully monetize them.
The framework's architecture creates a dangerous scenario where automation platforms collapse the distance between initial access and privileged execution. If a malicious skill lands inside a trusted agent, the attacker effectively inherits the permissions of the automation environment.
Current Risk Assessment
The combined dataset suggests that OpenClaw is not currently showing signs of mass criminal operationalization at scale. However, this doesn't mean organizations should ignore the threat. The security community is talking about OpenClaw more than threat actors are currently exploiting it, but historically, this phase often precedes real weaponization by weeks or months.
The lesson from OpenClaw is less about one framework and more about a broader shift. Automation platforms with plugin ecosystems are becoming high-value targets long before organizations realize they have deployed them at scale.
Protection Recommendations
Organizations should take immediate steps to protect against OpenClaw-related threats:
Monitor for OpenClaw deployments: Many organizations may have deployed OpenClaw agents without security team awareness, particularly in shadow IT scenarios.
Implement skill verification: Establish processes to verify the authenticity and safety of skills before installation, similar to app store security practices.
Restrict agent permissions: Run OpenClaw agents with the minimum necessary privileges rather than root or system-level access.
Monitor network traffic: Look for unusual outbound connections that might indicate credential exfiltration from compromised skills.
Educate users: Train employees about the risks of installing automation plugins and the importance of using only verified skills from trusted sources.
Use threat intelligence: Leverage platforms like Flare that monitor underground forums and Telegram channels for emerging threats related to automation frameworks.
The OpenClaw case demonstrates how quickly AI-powered automation tools can evolve from productivity enhancers to security concerns. As organizations increasingly adopt these technologies, the attack surface expands, and the window between discovery and exploitation narrows. The current hype cycle around OpenClaw may be research-driven, but it serves as a critical warning about the future of supply chain attacks in an AI-automated world.
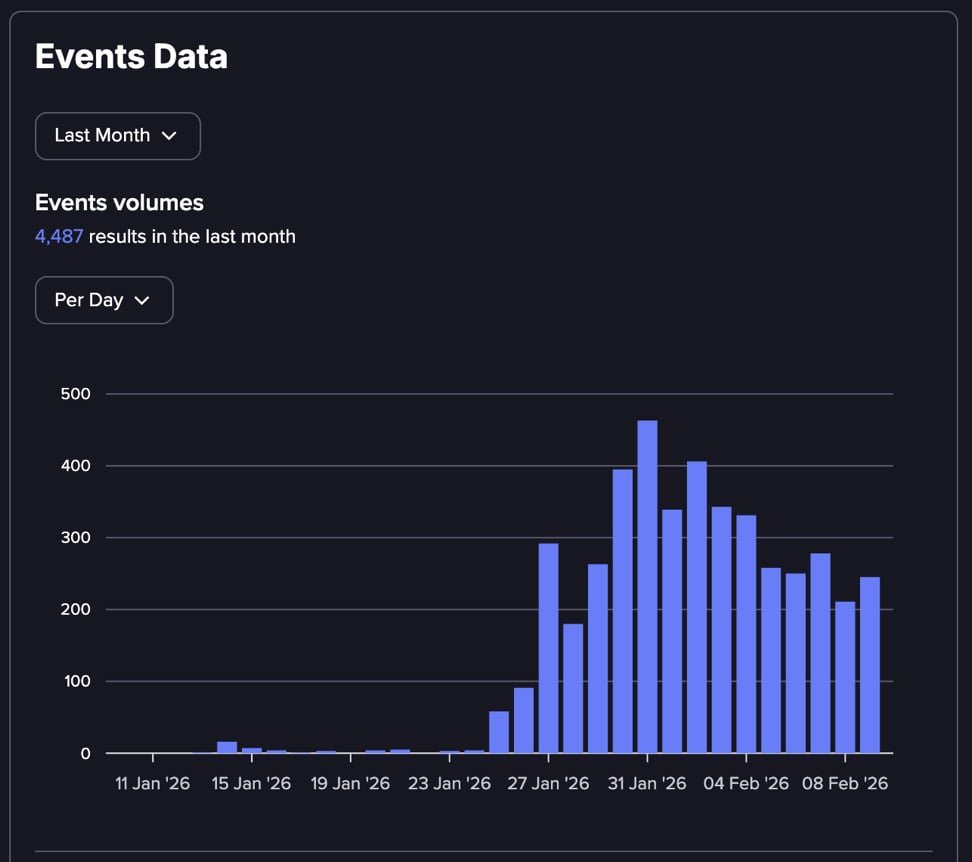
Figure: OpenClaw-related event volumes tracked by Flare showing dramatic spike in late January 2026
Comments
Please log in or register to join the discussion