This article examines the process of reverse-engineering a USB device protocol using Wireshark, focusing on the Nanoleaf Pegboard Desk Dock. The author demonstrates a systematic approach to capturing and analyzing USB traffic to understand how the device communicates, ultimately uncovering a relatively straightforward protocol that could enable Linux driver development.
In the landscape of hardware compatibility, Linux users often face challenges when manufacturers prioritize proprietary operating systems like Windows and macOS. This reality confronted the author when they purchased the Nanoleaf Pegboard Desk Dock, a USB hub featuring RGB LEDs and gadget hooks, only to discover its lack of Linux support. Rather than accepting this limitation, the author embarked on a reverse-engineering journey using Wireshark, a network protocol analyzer with USB capabilities, to decipher the device's communication protocol.
The core argument presented in this article is that USB protocol reverse-engineering, while potentially daunting, is accessible through systematic packet capture and analysis. The author demonstrates that even without official documentation, developers can understand and potentially replicate device functionality by observing how official software interacts with hardware.
The methodology employed by the author reflects a pragmatic approach to technical problem-solving. Initially, they had set up a Windows virtual machine for reverse-engineering, finding it "more complicated than it needed to be." This experience informed their decision to explore alternative approaches, ultimately settling on Wireshark for packet capture. The author considered two implementation approaches: installing Wireshark on the host machine (Linux/NixOS) versus the guest machine (Windows). Both methods had trade-offs—host setup provided global visibility but might introduce noise, while guest setup focused on specific device traffic but had potential compatibility issues. The author ultimately found the guest approach more useful, highlighting the importance of empirical testing in technical investigations.
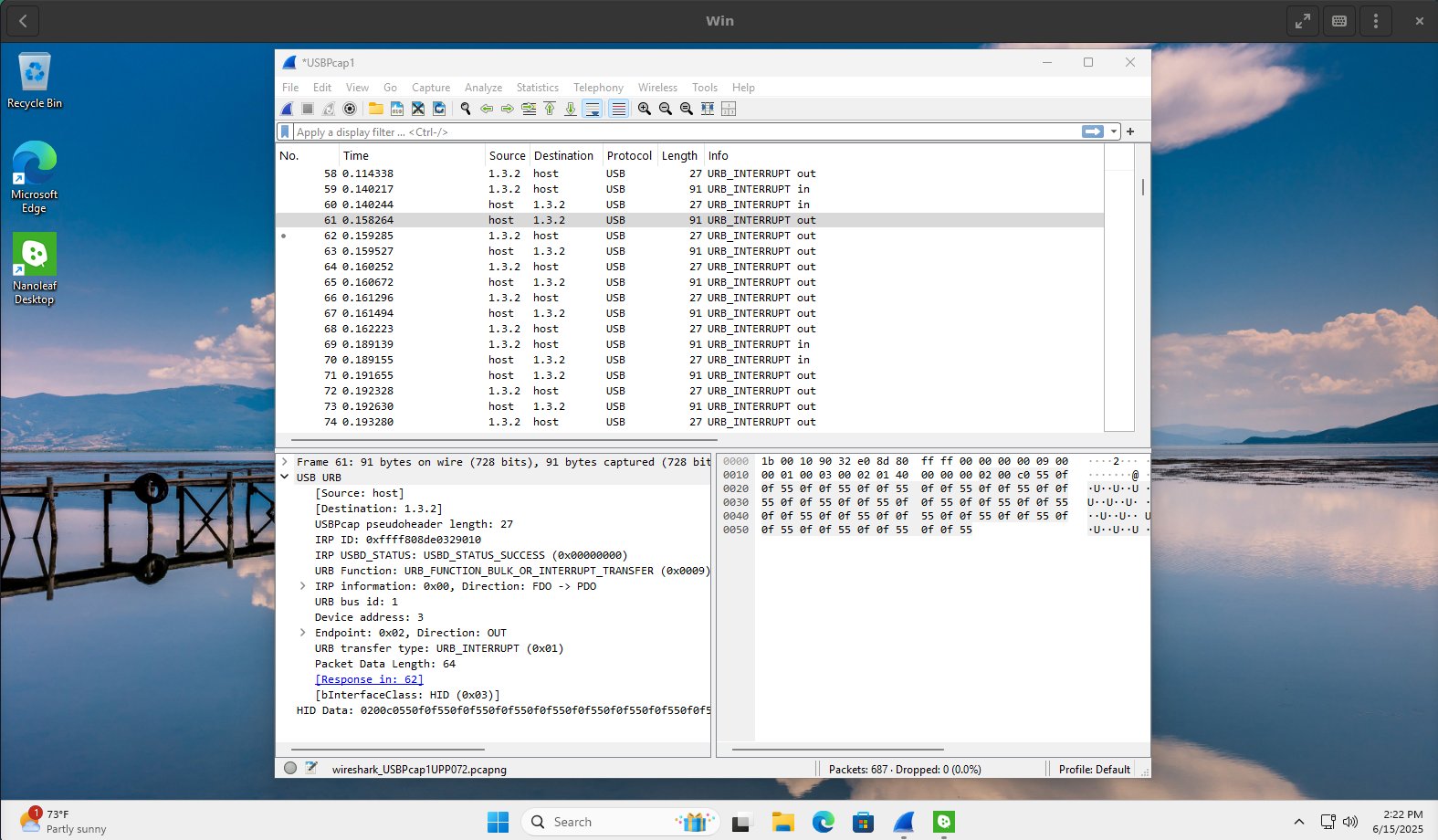
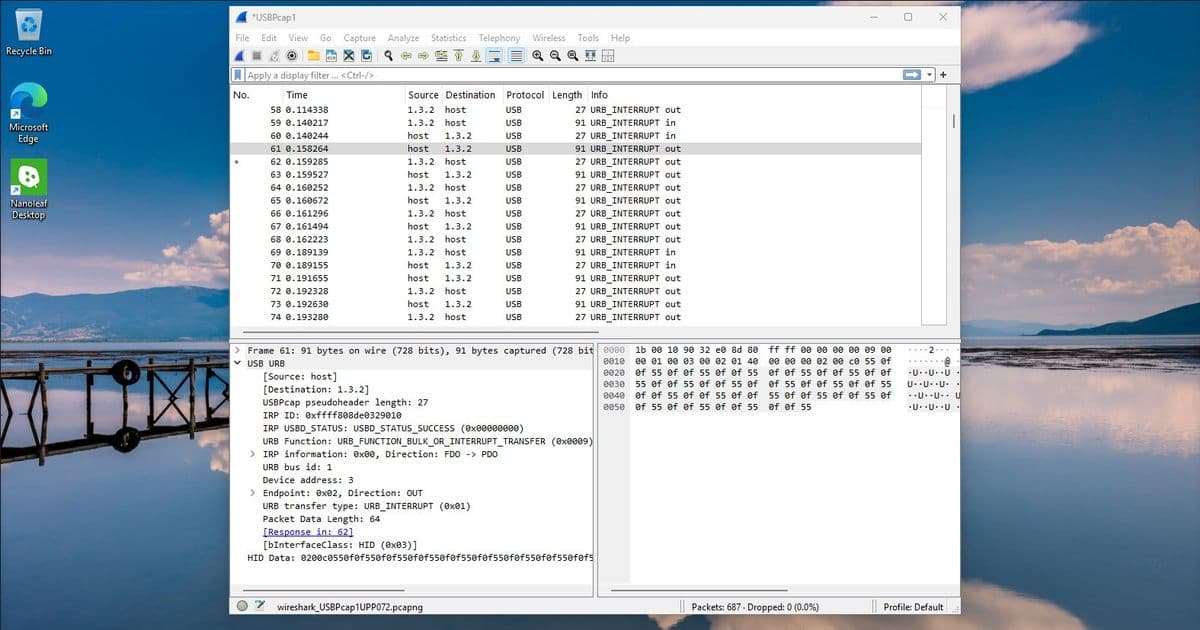
The technical analysis forms the heart of the article, showcasing a methodical approach to packet interpretation. After setting up Wireshark with USB capture capabilities on both systems, the author captured traffic while changing device colors via the official Nanoleaf app. The initial deluge of packets revealed a pattern: URB_INTERRUPT packets appearing every 20 milliseconds, with a consistent sequence of 8 packets out, 2 packets in, and 4 "out" packets containing data from host to device.
Upon examining the packet contents, the author identified a Type-Length-Value (TLV) format. Each packet began with a header (02 00 c0), followed by 192 bytes of color data. The hexadecimal value c0 (192 decimal) corresponded to the expected length for 64 RGB LEDs (64 × 3 bytes = 192 bytes). This structure suggested a relatively straightforward protocol, contrary to the author's initial concerns about "weird proprietary image format or invoke subroutines on the device itself."
The analysis uncovered several protocol peculiarities that deviated from standard RGB representation. When setting a static red color, the observed pattern was 0f ff 0f rather than the expected ff 00 00. Similarly, dark green appeared as 55 0f 0f instead of 00 55 00. This suggested a GRB color format rather than RGB. Further anomalies emerged when turning the device completely off (0f 0f 0f) or setting it to pure white (d7 ff a1), with the latter causing device resets even through official drivers. The author hypothesized that these inconsistencies stemmed from device limitations that the official driver attempted to mitigate without full success.
For Windows users looking to replicate this approach, the author notes that USBPcap is required to enable USB packet capture on Windows, with specific setup instructions including copying the USBPcapCMD.exe executable to the Wireshark plugins directory.
The implications of this reverse-engineering work extend beyond the specific Nanoleaf device. The author's methodology demonstrates a generalizable approach for hardware compatibility issues on Linux systems. By systematically capturing and analyzing USB traffic, developers can create open-source drivers for unsupported hardware, potentially bridging the gap between proprietary devices and open-source operating systems.
The article also highlights the importance of understanding that not all protocols are equally complex. While the Nanoleaf protocol proved relatively straightforward, the author acknowledges that more sophisticated devices—such as input devices with multiple axes and buttons—would present greater challenges. Nevertheless, the fundamental approach remains applicable: isolate variables, observe changes, and build understanding incrementally.
Counter-perspectives to this approach might include the argument that reverse-engineering is unnecessary when manufacturers could provide better Linux support. Additionally, some might question the legality of reverse-engineering proprietary protocols, though in many jurisdictions, such activities for interoperability purposes are protected. The author doesn't address these concerns directly, focusing instead on the technical aspects of the process.
The article concludes with a forward-looking statement about implementing a Linux driver based on the discovered protocol. The author plans to cycle through each green-red-blue set to map the LED layout and develop more complex patterns, acknowledging that the actual implementation details remain to be determined. This ending serves as both a completion of the current investigation and an invitation for further exploration.
This case study exemplifies how technical curiosity and systematic analysis can overcome hardware limitations in open-source environments. The Wireshark-based methodology demonstrated here provides a blueprint for developers facing similar challenges, potentially expanding the compatibility of Linux with a wider range of hardware devices. As the author suggests, while the specific protocol might be simple, the approach remains valuable for more complex devices, making this article both a practical guide and an inspiration for technical problem-solving.
Comments
Please log in or register to join the discussion