
Chips
Inside the Spacelab Mitra 125 MS: Reverse‑Engineering a 1980‑Era ALU Board
5/23/2026
Hardware
Inside the 80386: How a community reverse‑engineered a 95 KB microcode ROM
5/23/2026

Regulation
Software Freedom vs. Corporate Control: SFC's Stand Against Bambu Lab's AGPLv3 Violations
5/19/2026
Hardware
Reverse-Engineered PS2 Silicon Powers Custom Handheld Modder's Bespoke Portable Console
5/18/2026
Security
The Art of Software Reversal: Deconstructing Grateful Dead D2S2's Serial Validation
5/18/2026
Hardware
Running Windows CE 2.11 on a Nintendo 64: A Hobbyist’s Reverse‑Engineering Journey
5/15/2026
Security
Reverse Engineering macOS QuickLook: When System Changes Require Technical Intervention
5/10/2026
Security
Why Complex Windows Malware Analyses Have Become Rarest
5/9/2026
Chips
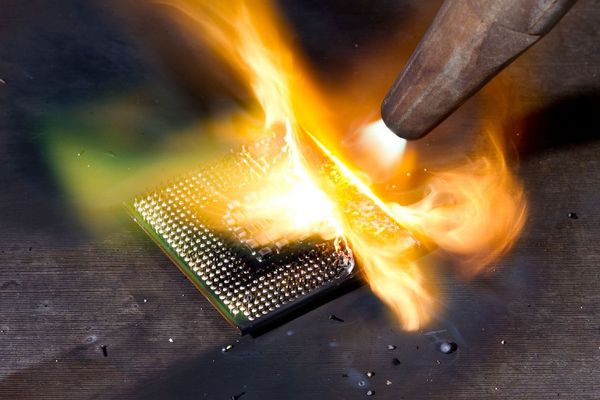
Extreme CPU Delidding: When Unconventional Tools Meet Silicon Analysis
5/3/2026
Hardware
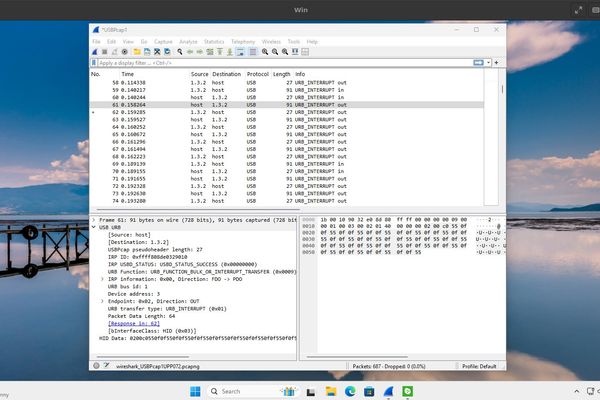
Reverse-Engineering USB Protocols: A Case Study with Wireshark and the Nanoleaf Desk Dock
4/11/2026
Security
The Mysterious UVWATAUAVAWH: A Deep Dive into Windows Binary Strings
3/30/2026

Hardware
Enthusiast reverse engineers world’s smallest HDD to access data with help from an old Nokia N91 and OpenClaw — open source USB bridge unlocks 0.85-inch mechanical Toshiba drive from 2004
3/17/2026
Hardware
Rich Whitehouse: The Art of Reverse Engineering and Open-Source Innovation
3/9/2026