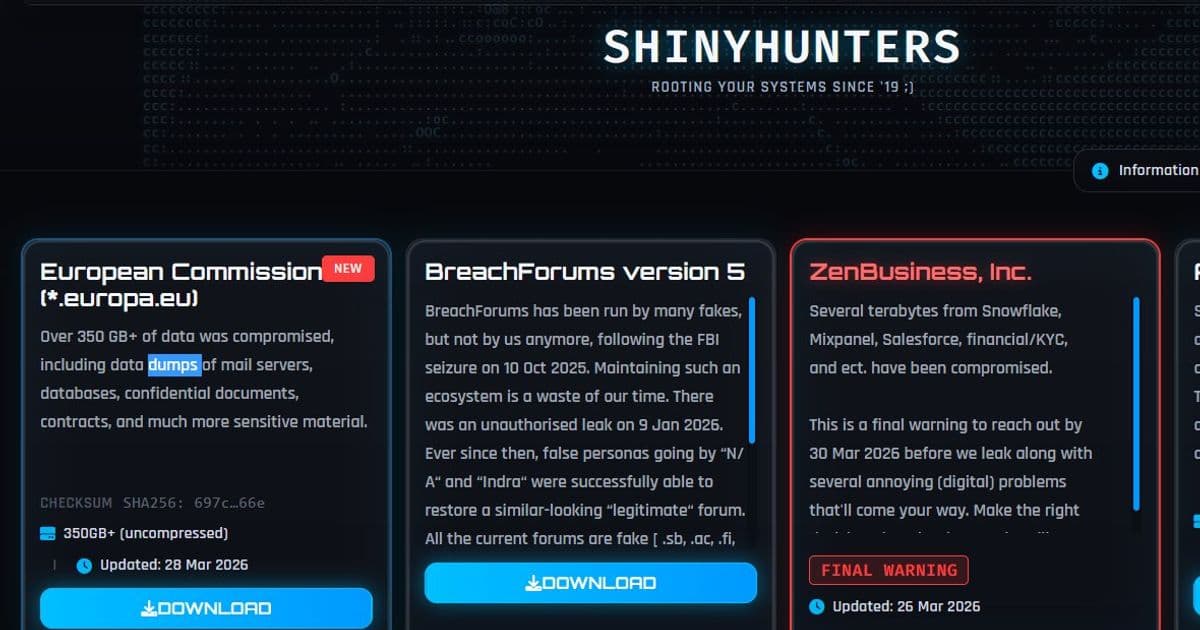
ShinyHunters claims responsibility for stealing over 350GB of data from the European Commission, including mail server content, though the EC states internal systems were unaffected.
The notorious cybercrime group ShinyHunters has claimed responsibility for a major data breach targeting the European Commission, allegedly stealing over 350GB of sensitive information including content from mail servers. The attack, which was detected on March 24, 2026, has raised significant concerns about cybersecurity vulnerabilities within EU institutions.
The European Commission has confirmed the breach but maintains that its internal systems were not affected, creating a discrepancy between the attacker's claims and the official response. This gap in narratives is common in high-profile cyberattacks, where organizations often downplay the severity of incidents while attackers exaggerate their impact.
ShinyHunters has built a reputation as one of the most active and successful cybercrime groups in recent years, specializing in data theft and extortion. The group typically targets large organizations, steals sensitive data, and threatens to publish it unless ransom demands are met. Their modus operandi involves breaching corporate networks, exfiltrating vast amounts of data, and then negotiating with victims through various channels.
This latest attack on the European Commission represents a significant escalation in the group's targeting strategy, moving from private corporations to governmental institutions. The European Commission serves as the executive branch of the European Union, making it a high-value target for cybercriminals seeking to disrupt EU operations or gain access to sensitive diplomatic and policy-related communications.
According to reports from multiple cybersecurity sources, the stolen data reportedly includes a substantial amount of email correspondence and other communications stored on mail servers. The exact nature of the compromised information remains unclear, though the scale of the breach suggests it could contain sensitive discussions about EU policies, international relations, and internal administrative matters.
The timing of this breach is particularly noteworthy given the current geopolitical climate and the European Union's role in various international negotiations and policy decisions. Any compromise of EU communications could potentially impact ongoing diplomatic efforts or provide adversaries with insights into the bloc's strategic thinking.
Cybersecurity experts have noted that governmental institutions often lag behind private sector organizations in implementing robust security measures, making them attractive targets for sophisticated hacking groups. The European Commission, like many large bureaucratic organizations, likely faces challenges in maintaining consistent security protocols across its various departments and international offices.
This incident follows a pattern of increasing cyberattacks against governmental and international organizations worldwide. As digital transformation accelerates and more sensitive operations move online, the attack surface for potential breaches continues to expand, creating new vulnerabilities that sophisticated threat actors can exploit.
The European Commission's response to the breach will be closely watched by other governmental institutions and cybersecurity professionals. The effectiveness of their incident response, transparency in communication, and measures taken to prevent future attacks will likely influence cybersecurity practices across the public sector.
For ShinyHunters, this high-profile attack could represent a significant milestone in their criminal operations, potentially increasing their leverage in future extortion attempts and attracting attention from law enforcement agencies worldwide. The group's ability to successfully breach such a prominent target may encourage other cybercriminals to target similar high-value governmental institutions.
As investigations continue, cybersecurity professionals will be analyzing the attack vectors used, the vulnerabilities exploited, and the overall impact on EU operations. This analysis will be crucial for developing improved security measures and preventing similar breaches in the future.
The broader implications of this breach extend beyond the immediate data compromise. It highlights the ongoing challenges faced by governmental institutions in protecting sensitive information in an increasingly hostile digital environment. The incident serves as a reminder that no organization, regardless of its importance or resources, is immune to sophisticated cyber threats.
Moving forward, the European Commission and other governmental bodies will likely need to reassess their cybersecurity strategies, potentially investing in more advanced threat detection systems, implementing stricter access controls, and conducting more frequent security audits. The cost of these improvements, while substantial, pales in comparison to the potential damage from future breaches.
This attack also underscores the importance of international cooperation in combating cybercrime. As threat actors operate across borders, effective responses require coordination between law enforcement agencies, cybersecurity firms, and governmental institutions across multiple jurisdictions.
The coming weeks will likely reveal more details about the extent of the breach and the specific information compromised. Until then, the cybersecurity community will be watching closely to see how this incident unfolds and what lessons can be learned to strengthen defenses against similar attacks in the future.
For now, the European Commission faces the dual challenge of managing the immediate fallout from the breach while also addressing the longer-term implications for its cybersecurity posture. The outcome of this situation could have lasting effects on how governmental institutions approach digital security in an era of increasingly sophisticated cyber threats.
[Featured image: 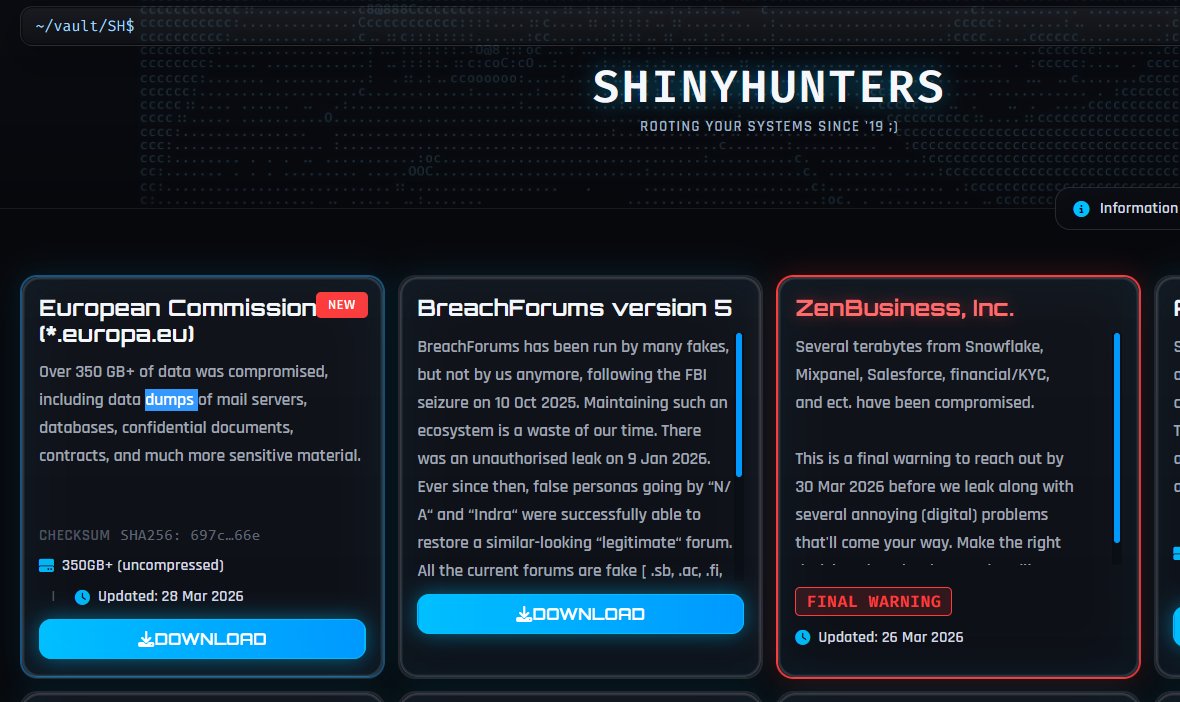 ]
]
Comments
Please log in or register to join the discussion