A deep examination of subscription bombing—its mechanics, real‑world case studies, underground services, and the layered defenses needed to protect inboxes from this growing form of digital disruption.
Introduction
Subscription bombing, sometimes called subscription flooding, exploits the trust that email providers place in legitimate third‑party senders. By silently registering a victim’s address with thousands of newsletters, password‑reset services, and other notification systems, an attacker can flood an inbox with messages that pass SPF, DMARC, and DKIM checks, evade traditional spam filters, and hide any subsequent malicious activity. The technique has resurfaced with alarming frequency, moving from isolated incidents in the 1990s to coordinated campaigns that deliver thousands of emails per hour.
How the Attack Works
- Victim Identification – The attacker harvests email addresses from public sources (company web pages, LinkedIn, data‑leak dumps) or from prior phishing compromises.
- Service Database Construction – Using crawlers or manual research, the attacker builds a list of services that send confirmation or notification emails. The CACM study discovered that roughly 70 % of these services require a CSRF token or nonce, meaning the attacker must first fetch a page to obtain the token before posting the subscription request.
- Automation – A script (often a series of
curlcommands or a headless‑browser bot) iterates over the service list, submitting the victim’s address. Some actors employ AI‑driven browser agents (e.g., airtop.ai or axiom.ai) to solve CAPTCHAs and handle dynamic forms. - Delivery – Each service sends a confirmation or welcome email. Because the sending domain has a good reputation, the messages land in the inbox rather than the junk folder.
- Optional Follow‑up – In many campaigns the flood serves as a smokescreen for a credential‑theft attempt, ransomware deployment, or a social‑engineering call that pretends to help the victim clean up the spam.
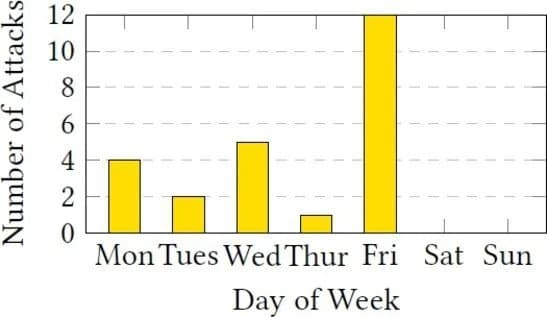
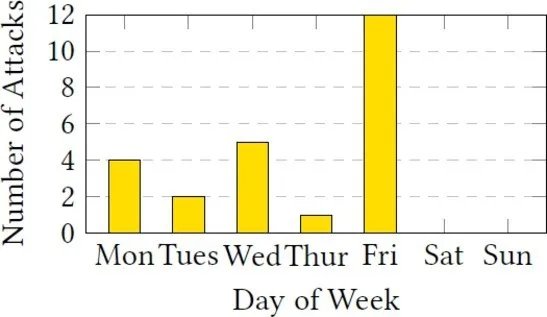 Figure 1 – Distribution of attacks across weekdays; half occur on Friday.
Figure 1 – Distribution of attacks across weekdays; half occur on Friday.
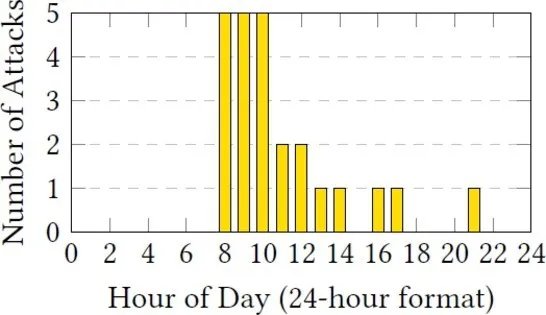 Figure 2 – Hour‑of‑day pattern; attacks concentrate between 08:00 and 10:00.
Figure 2 – Hour‑of‑day pattern; attacks concentrate between 08:00 and 10:00.
Empirical Findings from the Large‑Scale Dataset
The CACM case study examined 24 campaigns encompassing 46,970 unwanted emails collected from European enterprises between October and December 2024. Key observations include:
| Metric | Value |
|---|---|
| Average emails per wave | 1,957 (≈ 1,516 per hour) |
| Peak wave | 4,847 emails in 2 hours |
| Typical victim profile | Senior managers whose addresses are publicly listed |
| Top sender TLD | .com (52.8 %) |
| Most common sender prefix | info@ (26.5 %) |
| SPF/DKIM/DMARC pass rates | 91.7 % / 74.3 % / 45.2 % |
| Emails classified as spam (SCL ≥ 5) | 28 % |
| Unsubscribe link present | 34.4 % (one‑click in 16.2 %) |
The data reveal a striking temporal bias: 71 % of attacks began on Friday mornings, a window when many security teams are understaffed and users are less likely to notice a sudden surge. No attacks were observed between 22:00 and 07:00, indicating that attackers deliberately align the flood with the victim’s working hours.
Case Study: Company Omega
Two senior executives, Alpha and Beta, were hit on consecutive days. Alpha received 999 emails in just over an hour; Beta saw 719 emails in a similar window. The emails originated from 126 distinct services, none of which were high‑value platforms (e.g., banking or social media). Most messages were newsletters or account‑reset confirmations, and the majority of sender addresses were generic (info@, noreply@).
A notable pattern was the creation of throwaway accounts on the abused services, followed by immediate password‑reset requests. This tactic inflates the volume of emails without granting the attacker any lasting foothold in the victim’s accounts.
Motivations Behind Subscription Bombing
| Goal | Description |
|---|---|
| Harassment / Revenge | Victims are overwhelmed as a form of digital retaliation. Public figures and disgruntled employees are frequent targets. |
| Distraction | The flood masks concurrent activities such as credential stuffing, data exfiltration, or fraudulent purchases. |
| Follow‑up Social Engineering | Attackers later pose as IT support, offering to “clean up” the inbox, thereby gaining remote access via tools like AnyDesk. |
| Overload / DDoS‑like effect | By exceeding mailbox quotas, legitimate alerts are delayed or dropped, potentially crippling incident response. |
Even when the immediate financial gain is modest, the low cost to the attacker (often less than a dollar per thousand emails) makes the technique attractive.
Subscription Bombing as a Service (SBaaS)
Underground marketplaces list SBaaS under names such as emailbomb.cc, subscribethemall.com, and mailbait.info. A typical offering includes:
- Drip‑feed scheduling – 75 to 3,000 emails per hour, configurable for up to 31 days.
- Pricing – $1 per 1,000 emails on a standard list; premium lists (claimed to bypass filters) cost $10 per 1,000.
- Delivery guarantees – Reported inbox success rates of 20‑25 % for free trials.
- Payment – Cryptocurrency only (BTC, LTC, XMR).
The study’s own interaction with a public SBaaS instance confirmed the advertised capabilities: a 24‑hour trial delivered 3,930 emails, of which 24 % landed in the inbox.
Defensive Strategies
1. Rate‑Limiting and Anomaly Detection
Email gateways can flag accounts that receive an unusually high number of messages from previously unseen domains. A threshold (e.g., > 500 new senders within 30 minutes) can trigger a quarantine and an alert to the security team.
2. Automated Unsubscription
Because manual unsubscription is impractical, organizations should explore AI‑assisted agents that navigate unsubscribe pages, solve CAPTCHAs, and submit opt‑out requests. Early prototypes achieve ~ 45 % success; continued research is needed to improve reliability across languages and custom UI flows.
3. Sender Reputation Enrichment
Maintaining a trusted‑sender list based on historical interaction helps the mail server prioritize known contacts. Conversely, a negative‑sender list can be built from domains observed in a confirmed attack wave, automatically bouncing future messages from those sources.
4. Encouraging Provider Hardening
Newsletter services can mitigate abuse by:
- Requiring double‑opt‑in confirmation links.
- Implementing CAPTCHA or email‑rate throttling on sign‑up endpoints.
- Providing a single‑click unsubscribe that works without additional authentication.
While these measures add friction, they reduce the pool of exploitable services and protect providers from being black‑listed.
Open Questions and Future Directions
- Can machine‑learning classifiers be trained on the subtle header patterns of subscription‑bomb emails without generating excessive false positives?
- Will generative AI agents lower the barrier to building and maintaining high‑quality service lists, thereby increasing attack volume?
- Should legislation mandate a standard
List-Unsubscribeheader for all bulk‑mail senders, and would such a rule meaningfully curb the impact?
Addressing these questions will require collaboration between academia, industry, and policy makers.
Conclusion
Subscription bombing demonstrates how a seemingly benign feature—mass email notifications from reputable services—can be weaponized with minimal effort. The CACM dataset shows that attacks are highly targeted, temporally precise, and capable of overwhelming even well‑configured inboxes. Mitigation must therefore be multi‑layered: rate‑limiting, AI‑driven unsubscription, enriched sender reputation, and hardening of the services that act as amplifiers. As automation tools become more sophisticated, the threat surface is likely to expand, making proactive research and cross‑sector cooperation essential.
References
- The original study is available via DOI 10.1145/3797487.
- For further reading on AI‑assisted browser automation, see the documentation of airtop.ai and axiom.ai.
- Historical context on early email bombing can be found in the 1996 stock‑broker incident (see ACM SIGCOMM archives).
Comments
Please log in or register to join the discussion