Canonical commissioned a security audit of Rust Coreutils that revealed 113 issues, including 44 CVEs. While most have been fixed for Ubuntu 26.04, the distribution will still rely on GNU Coreutils for critical commands due to remaining TOCT vulnerabilities. Ubuntu 26.10 aims to complete the transition to '100% Rust Coreutils'.
Ahead of tomorrow's Ubuntu 26.04 LTS release, Canonical published a blog post outlining the current state of Rust Coreutils and the results of a recent security audit. The findings reveal both progress and challenges in Ubuntu's ambitious plan to replace traditional GNU Coreutils with Rust implementations.
Security Audit Results
Canonical recently commissioned an independent external security audit of Rust Coreutils conducted by Zellic. The comprehensive audit uncovered 113 issues in total, including 44 Common Vulnerabilities and Exposures (CVEs). This represents a significant vetting of the Rust implementations that Canonical hopes will eventually replace decades-old GNU utilities.
The audit identified various categories of issues:
- Memory safety vulnerabilities
- Logic errors in command implementations
- Potential race conditions
- Input validation weaknesses
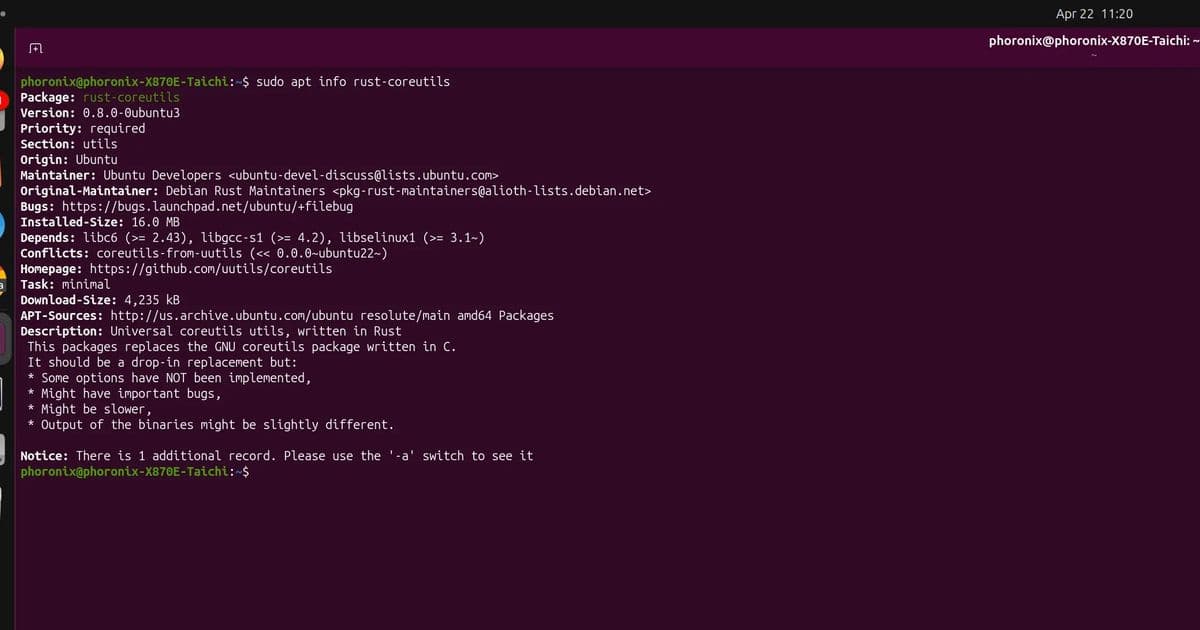
"The vast majority of those issues have since been addressed," according to Canonical's Ravi Kant Sharma, who authored the post detailing the audit. Ubuntu 26.04 LTS will ship with Rust Coreutils 0.8, which incorporates most of these security fixes.
Current Implementation in Ubuntu 26.04
Despite the progress, Ubuntu 26.04 LTS will not fully transition to Rust Coreutils. Specifically, the cp, mv, and rm commands will continue to be provided by GNU Coreutils due to persistent time-of-check to time-of-use (TOCTOU) issues in the Rust implementations.
TOCTOU vulnerabilities occur when there's a time gap between checking a condition and acting on it, allowing an attacker to modify the state between these operations. These race conditions are particularly problematic for file manipulation utilities that modify filesystem state.
Transition Strategy
Canonical has outlined a clear path forward:
| Ubuntu Version | Rust Coreutils Status | GNU Coreutils Status |
|---|---|---|
| 26.04 LTS | Partial implementation | cp, mv, rm remain |
| 26.10 | Planned "100% Rust" | Full transition |
The hope by Canonical is to achieve "100% rust-coreutils" with Ubuntu 26.10. By that release, the remaining TOCTOU and other issues are expected to be resolved, allowing for a complete transition away from GNU implementations.
Why Rust Coreutils?
The move to Rust Coreutils represents several strategic advantages:
- Memory Safety: Rust's ownership model prevents entire classes of memory vulnerabilities common in C-based GNU utilities.
- Performance: Rust implementations often match or exceed GNU Coreutils in benchmarks, especially with modern hardware.
- Modern Tooling: Rust provides better tooling for development, testing, and maintenance.
- Security: The explicit nature of Rust's error handling forces developers to consider edge cases.
Technical Challenges
The transition isn't merely about rewriting utilities in Rust. Several technical challenges must be addressed:
- Behavioral Compatibility: Rust implementations must match GNU utilities' behavior exactly to avoid breaking scripts and workflows.
- Performance Parity: While Rust often performs well, some GNU utilities have decades of optimization.
- Edge Cases: Filesystem interactions involve countless edge cases that must be properly handled.
- POSIX Compliance: Maintaining compliance with POSIX standards is crucial for enterprise environments.
Community Response
The Ubuntu community has reacted with cautious optimism to the audit results. While the number of issues identified may seem high, the proactive security audit demonstrates Canonical's commitment to robustness.
"It's better to find these issues now during development rather than after deployment," noted one Ubuntu developer in the comments section. "The fact that most have already been fixed shows the maturity of the Rust Coreutils project."
Looking Ahead
Ubuntu's Rust Coreutils initiative represents one of the most significant transitions in the distribution's history. The security audit, while revealing challenges, ultimately strengthens the project's foundation.
For system administrators and power users, the transition will likely be transparent. The focus remains on maintaining the familiar command-line experience while gaining the benefits of modern, memory-safe implementations.
More details on the security audit, newly disclosed CVEs, and the transition timeline can be found on Ubuntu Discourse.
The Rust Coreutils project itself continues to evolve, with ongoing development addressing the remaining issues identified in the audit. As Ubuntu moves toward its 26.10 release, we'll see whether Canonical can achieve its ambitious goal of "100% Rust Coreutils" while maintaining the reliability and compatibility that users expect.
Comments
Please log in or register to join the discussion