
Security
Bridging the Cybersecurity Gap: Aligning SOC Needs with Executive Purchasing Decisions
1/21/2026

Security
Building Custom Playbooks in Microsoft Sentinel: A Step-by-Step Guide to Automation
1/21/2026
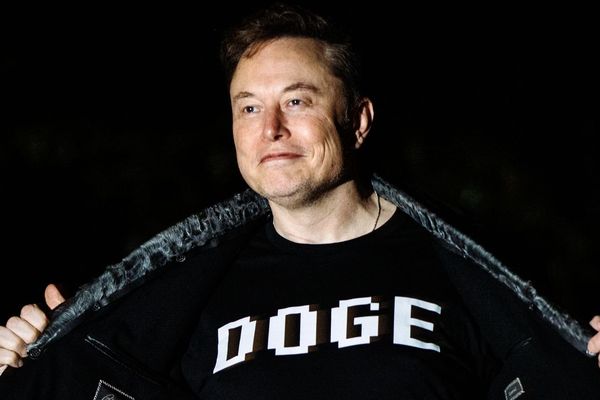
Security
DOGE Data Breach Exposes Systemic Government Privacy Failures
1/21/2026

Security
Microsoft Expands Copilot Data Protection with Sensitive Information Type Integration
1/21/2026

Security
New Verification Protocol Detects Malicious Code Generation in LLMs Without Execution
1/21/2026

Security
Architecting Account Integrity: The Dual Authentication Design of Artemis
1/21/2026

Security
Reddit Network Security Blocks Trigger Developer Concerns Over API Access
1/21/2026

Security
Dutch Society's Critical Dependency on U.S. Cloud Infrastructure Exposed
1/21/2026

Security
ICE protesters are increasingly turning to data leaks, surveillance
1/21/2026
Security
How CyberArk Protects AI Agents with Instruction Detectors and History-Aware Validation
1/20/2026
Security
Reddit's API Changes and the Developer Token Requirement: What It Means for the Community
1/18/2026

Security
HTTP Headers Reference
1/18/2026

Security
The Secret Break: How British Codebreakers Turned the Zimmermann Telegram Against Germany
1/18/2026