Google rolls out a new forensic logging feature in Android 16 to help detect and analyze sophisticated spyware attacks, developed in partnership with human rights organizations.
Google has unveiled a significant security enhancement for Android devices with the introduction of Intrusion Logging, a feature designed to detect and analyze sophisticated spyware attacks. Available as part of Advanced Protection Mode, this opt-in feature provides persistent, privacy-preserving forensics logging that could be invaluable for journalists, activists, and other high-risk individuals who suspect they're being targeted by advanced surveillance tools.
How Intrusion Logging Works
Intrusion Logging captures comprehensive device and network activities on a daily basis, creating a detailed record that security experts can analyze to identify potential compromises. The feature logs several types of activities:
- App activity (including when app processes start)
- App installations, updates, and uninstalls
- Network connections such as Wi-Fi/Bluetooth activity, DNS lookups, and IP addresses
- File transfers to or from the device via USB
- Changes to system certificates
- Device lock and unlock events
What makes this feature particularly noteworthy is its approach to privacy and security. The log data is end-to-end encrypted by the device itself and stored on Google's servers. The encryption keys are secured by the user's Google Account password and screen lock credentials, ensuring that even Google cannot access the logs—only the device owner can.
"By storing the data on a secure server, even malware installed on the smartphone cannot access, delete, or manipulate it," Reporters Without Borders explained. "End-to-end encryption also ensures that neither Google nor state actors can access the data. The Intrusion Logging function in particular enables detection and forensic analysis of even highly sophisticated and previously difficult-to-detect attacks."
Practical Implementation and Limitations
Once enabled, the encrypted logs are stored for 12 months, after which they're automatically wiped. Importantly, users cannot delete the logs before this expiration window, even if they disable the feature or close their Google account. However, users can download the logs offline for longer-term retention.
Google has emphasized that once logs are downloaded and decrypted, users become responsible for their security. "In certain legal or regulatory environments, you may be required by law to provide access to your decrypted data or your security credentials," the company noted.
One limitation to be aware of is that the feature records network events during Chrome Incognito browsing, including DNS lookups and IP connections. Since it operates at the system level without distinguishing between browsing modes, anyone with access to decrypted logs can determine which websites were visited, though not specific pages on those sites.
The Human Rights Context
The development of Intrusion Logging in partnership with Amnesty International and Reporters Without Borders highlights the growing concern about spyware targeting journalists, activists, and human rights defenders. These sophisticated surveillance tools have increasingly been used to compromise devices and monitor communications without users' knowledge.
"With Intrusion Logging, Google is the first major vendor to proactively address the challenge of detecting advanced attacks on devices," said Donncha Ó Cearbhaill, head of Security Lab at Amnesty International. "By making more consensual forensic data available for researchers, we can make life more difficult for attackers and help civil society seek accountability when their devices are unlawfully targeted by spyware and mobile data extraction tools."
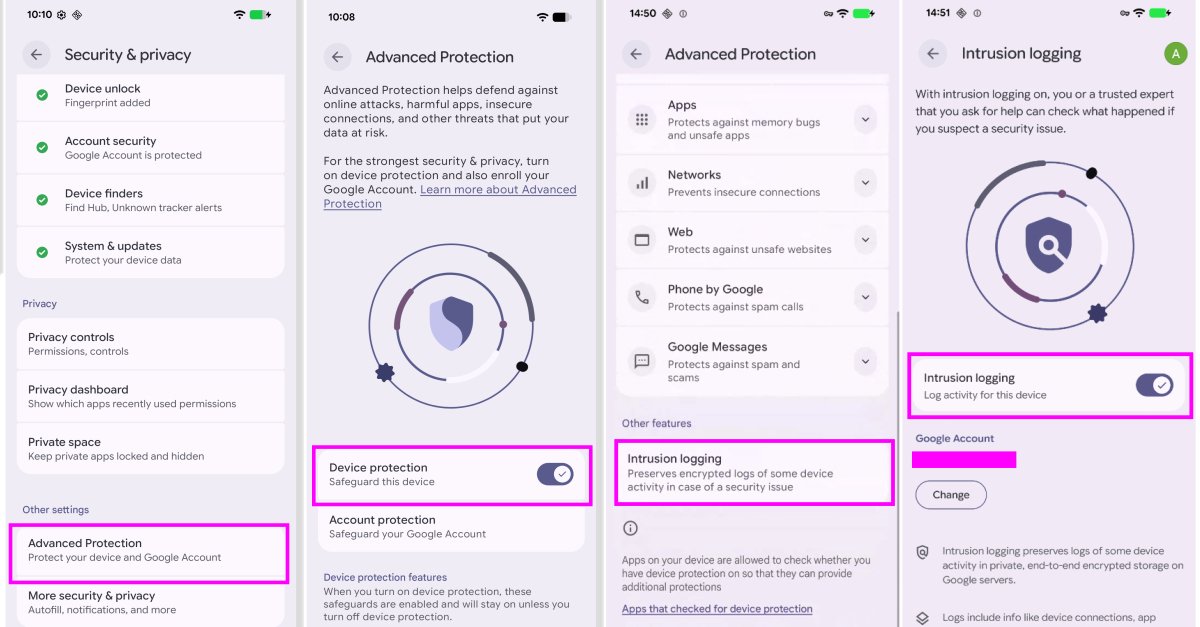
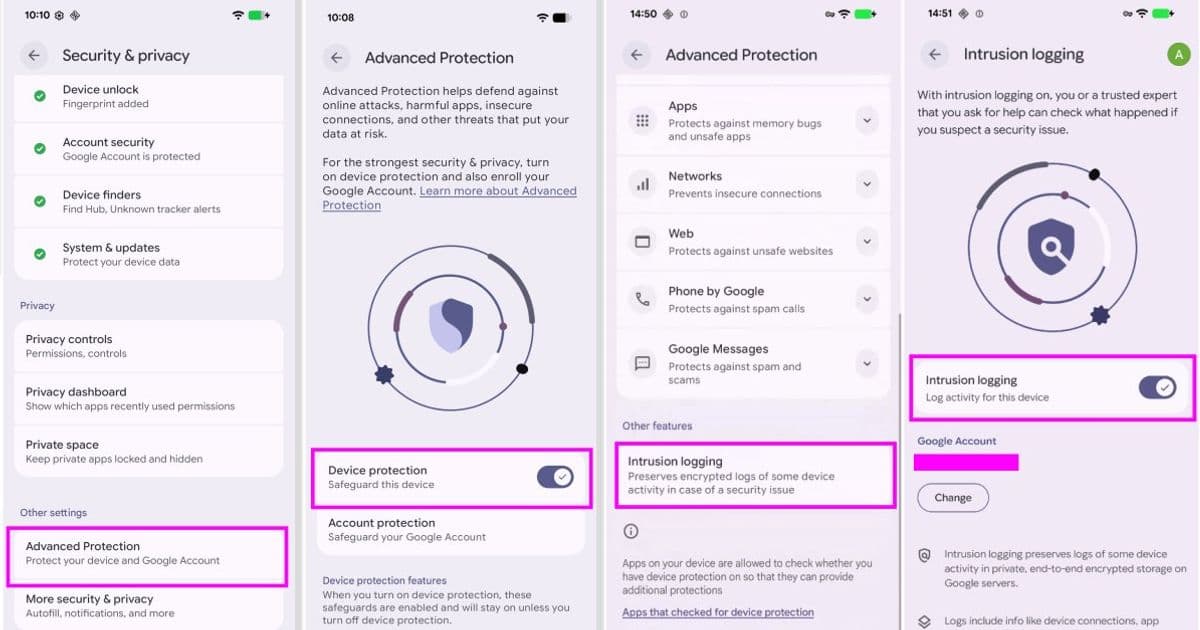
Enabling and Using the Feature
For users who want to enable Intrusion Logging:
- Navigate to the Settings app
- Tap Security & privacy
- Select Advanced Protection
- Choose Intrusion Logging
- Access logs to view or download them
The feature is currently rolling out to all devices running Android 16 and newer.
Broader Security Enhancements
Alongside Intrusion Logging, Google has announced several other security improvements coming to Android:
- Verified Financial Calls: A new feature to combat bank impersonation scams by having the system confirm with installed banking apps whether a call is legitimate
- Expanded Live Threat Detection: Warnings about suspicious app behavior, including SMS forwarding and accessibility overlays used by banking trojans
- Enhanced APK Verification: Chrome on Android now evaluates downloaded APK files for known malware before installation
- Accessibility API Restrictions: Removing access to accessibility services from apps not labeled as accessibility tools
- Improved Find Hub: Enhanced "Mark as lost" feature with biometric authentication to prevent thieves from disabling tracking
- Better Authentication Controls: Reducing the number of PIN/password attempts allowed and implementing longer wait times between failed attempts
- Precise Location Controls: Allowing users to share location temporarily only when specific apps are open
- AISeal with pKVM: Hardware-backed isolation for AI-related data processing
- Binary Transparency: Verification of official builds through a public ledger
- SMS OTP Protection: Hiding one-time passwords from most apps for three hours
- Post-Quantum Cryptography: Implementation to safeguard against future quantum computing threats
"By improving protections against banking scams, and extending powerful protections like Live Threat Detection and Android Advanced Protection, we are ensuring that Android remains the most secure platform," said Eugene Liderman, director of Android security and privacy.
Who Should Use This Feature
While Intrusion Logging could benefit any security-conscious user, it's particularly valuable for:
- Journalists and investigative reporters
- Human rights activists and defenders
- Lawyers handling sensitive client information
- Political figures and their staff
- Corporate executives in competitive industries
- Anyone who suspects they may be targeted by advanced surveillance
The feature represents a significant step forward in mobile security, giving users a way to detect sophisticated spyware that might otherwise remain hidden. By providing detailed forensic data while maintaining strong privacy protections, Google has created a valuable tool for both individuals and security researchers working to identify and combat advanced threats.
Comments
Please log in or register to join the discussion