Exploring the risks and best practices of TLS certificate pinning in Azure's open-source database offerings, with strategic guidance for enterprise deployments.
TLS Certificate Pinning in Azure Database Services: Strategic Considerations for PostgreSQL and MySQL
Transport Layer Security (TLS) encryption forms the backbone of secure communication between client applications and database servers. In Azure Database for PostgreSQL and MySQL, TLS certificates play a critical role in authenticating service endpoints while encrypting data in transit. However, the implementation of certificate pinning—a technique where applications restrict trust to specific certificates—introduces significant operational challenges in cloud environments.
What Changed: The Evolution of Certificate Management
Historically, certificate pinning emerged as a security measure to prevent man-in-the-middle attacks by binding clients to specific certificates. While this approach offers apparent security benefits, it creates operational fragility in modern cloud infrastructures where certificate rotations are routine. Azure Database services manage certificates centrally, with customers not directly controlling server-side certificates. This model fundamentally differs from traditional on-premises deployments where organizations had complete control over certificate lifecycles.
The architectural shift to cloud-managed certificates has necessitated a reevaluation of certificate trust strategies. Organizations moving to Azure Database for PostgreSQL or MySQL must adapt their security approaches to align with provider-managed certificate rotations while maintaining appropriate security controls.
Provider Comparison: Azure OSS Databases vs. Azure SQL
Understanding the differences in how Azure handles certificates across its database offerings is crucial for strategic decision-making.
Azure Database for PostgreSQL and MySQL
These services expose a traditional database engine-level TLS surface where clients directly validate server certificate chains. The certificates are anchored in public or regional certificate authorities, creating a client-managed trust model. This architecture allows for certificate pinning but places the burden of trust management on the client application.
Key characteristics:
- Direct TLS negotiation between client and database engine
- Certificates issued by well-known trusted public CAs including Microsoft-issued certificates
- Clients validate the entire certificate chain
- Certificate rotations are transparent to the service but may impact clients using pinning
Azure SQL
Azure SQL (including Azure SQL Database and Azure SQL Managed Instance) employs a different architectural approach. Client connections terminate at a service-managed endpoint rather than directly at the database engine. This abstraction layer centralizes certificate management, with certificates issued and rotated by the service itself.
Key characteristics:
- TLS endpoint abstraction through service-managed endpoints
- Certificates represent the Azure SQL service rather than specific machines
- Platform-managed certificate rotation
- Certificate pinning is generally not feasible due to the service-level abstraction
The architectural differences have significant implications for security strategy. Azure SQL clients are guided to use Encrypt=True and TrustServerCertificate=False, relying on platform-managed certificate validation. In contrast, Azure OSS database clients must implement their own trust validation logic, introducing both flexibility and responsibility.
Business Impact: Risks of Certificate Pinning
While certificate pinning may appear to enhance security, it introduces substantial operational risks in cloud environments:
Operational Fragility
Certificate rotations are inevitable for security and compliance purposes. When clients use certificate pinning, any change to the server certificate chain—even valid, security-enhancing updates—can cause connection failures. This creates potential service disruption during scheduled maintenance or security updates.
Increased Management Overhead
Organizations implementing certificate pinning must develop complex processes to:
- Monitor certificate expiration dates
- Coordinate updates across all client applications
- Ensure synchronized certificate rotations
- Maintain fallback mechanisms during pinning conflicts
This overhead contradicts the core cloud computing principle of reduced operational burden.
Security Posture Dilution
Ironically, the rigidity introduced by certificate pinning can weaken overall security by:
- Delaying necessary certificate updates due to fear of breaking applications
- Encouraging workarounds that bypass security controls
- Creating blind spots during certificate transitions
Strategic Recommendations: Best Practices for Enterprise Deployments
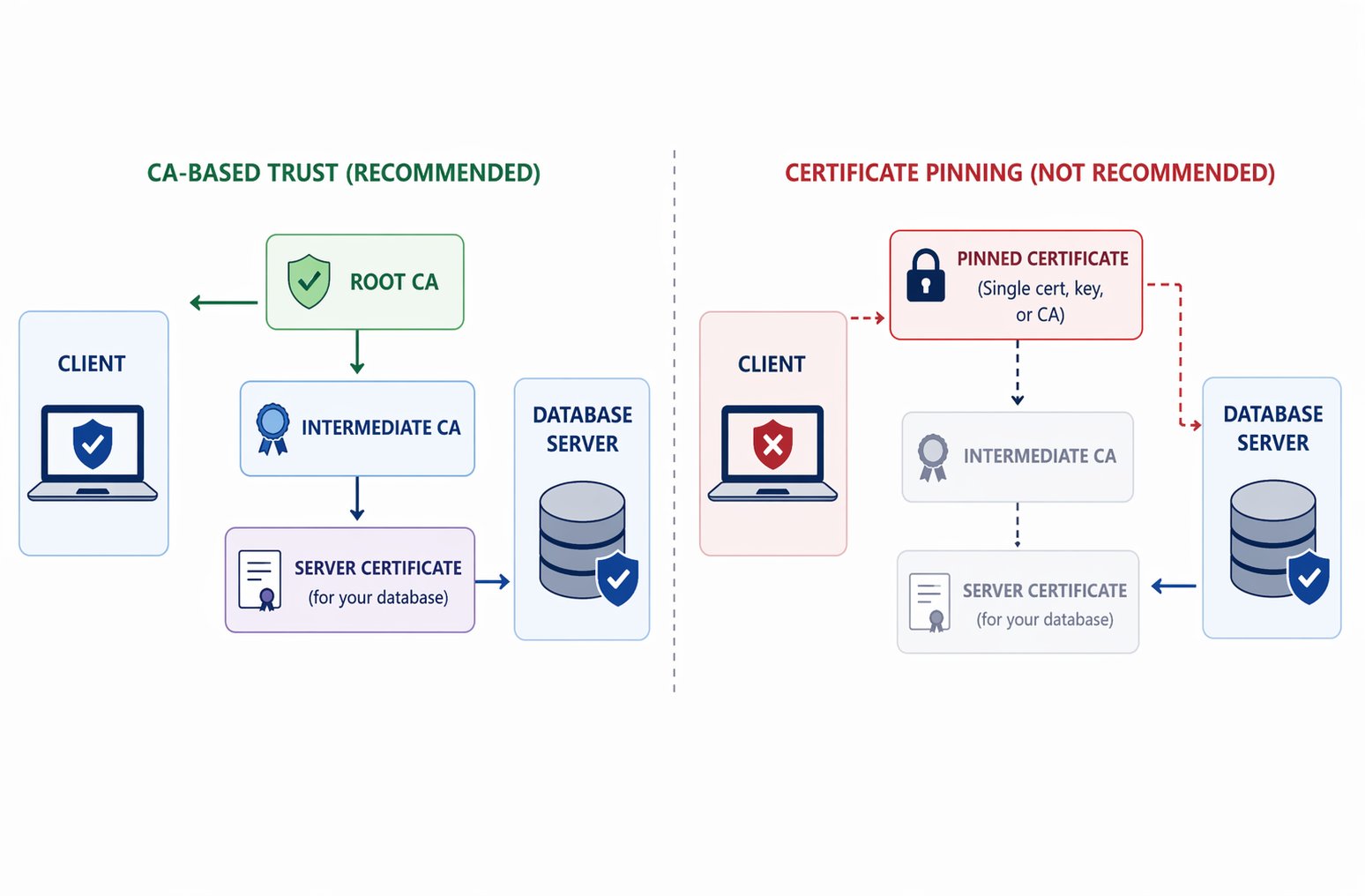
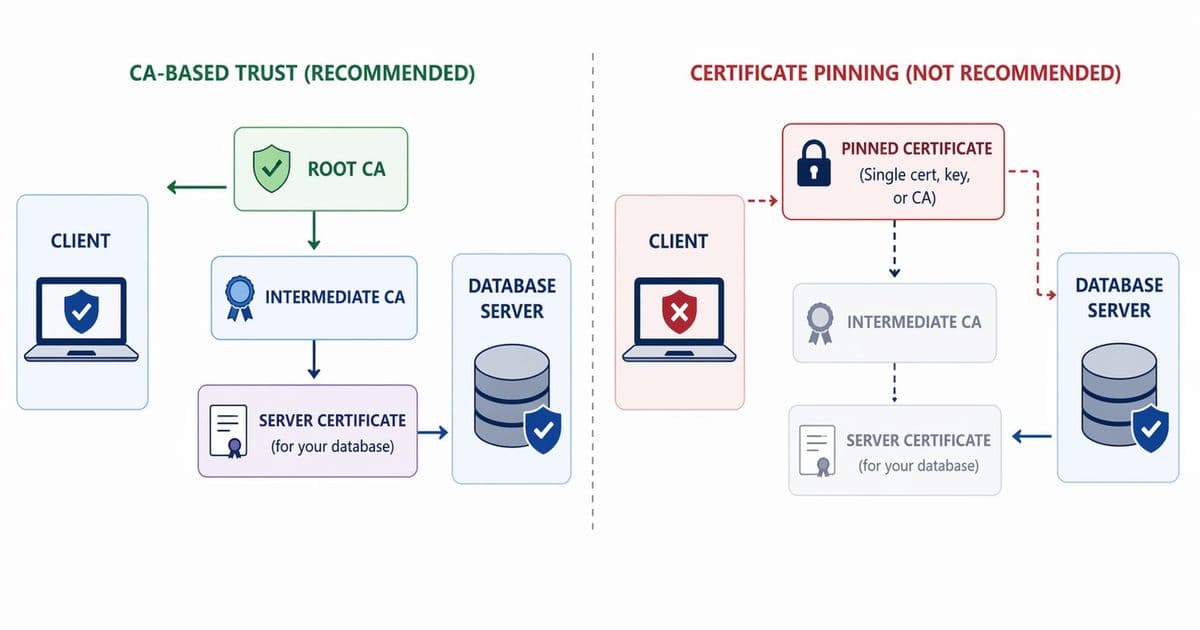
Adopt a CA-Based Trust Model
Instead of pinning specific certificates, organizations should implement a Certificate Authority (CA)-based trust model that allows certificates to change safely. This approach:
- Trust root CAs rather than individual certificates
- Configure clients to use standard TLS validation against Azure-documented root CAs
- Avoid configurations that restrict trust to specific certificates or narrowly scoped CA sets
For PostgreSQL client configurations, prefer:
sslmode=verify-ca: Validates the server certificate chain against trusted CAssslmode=verify-full: Verifies CA and hostname match
For MySQL client configurations, prefer:
ssl-mode=VERIFY_CA: Validates the server certificate chain against trusted CAsssl-mode=VERIFY_IDENTITY: Validates CA and hostname (similar to PostgreSQL verify-full)
These modes ensure proper authentication of service endpoints while maintaining resilience against certificate rotations.
Maintain a Combined CA During Certificate Rotations
Azure rotates root or intermediate CAs periodically. Organizations should:
- Add new root and intermediate CAs to client trust stores before rotations begin
- Retain existing certificates until transitions are complete
- Avoid removing older certificates prematurely
This combined CA approach ensures continuous validation during transitions without operational disruption.
Implement Proactive Monitoring
Establish monitoring systems to:
- Detect TLS handshake failures
- Identify certificate expiration dates
- Monitor Azure service health for certificate rotation announcements
- Implement alerts for potential pinning-related issues
Develop Rotation Playbooks
Create documented procedures for:
- Coordinating certificate updates across distributed applications
- Testing new certificates in staging environments
- Implementing rollback mechanisms if issues arise
- Communicating changes to development teams
Regular Security Assessments
Conduct periodic reviews of:
- Client certificate configurations
- Trust store contents
- Alignment with current Azure security recommendations
- Emerging threats to certificate-based authentication
Conclusion: Balancing Security and Operational Resilience
The shift to cloud-managed database services requires rethinking traditional certificate management strategies. While certificate pinning may offer apparent security benefits, its operational costs in cloud environments often outweigh the advantages.
Organizations should prioritize CA-based trust models that maintain security while accommodating routine certificate rotations. This approach aligns with cloud-native principles, reduces operational overhead, and enhances overall system resilience.
For the most current TLS certificate information, refer to the Azure Database for PostgreSQL documentation and Azure Database for MySQL documentation.
As cloud database services continue to evolve, organizations must develop flexible security strategies that balance protection with operational efficiency. The future of database security lies in adaptive trust models rather than static configurations, enabling both security and agility in cloud-native environments.
Comments
Please log in or register to join the discussion