Security researcher discovers RCE vulnerability in TP-Link TL-MR6400 router through careful firmware analysis, highlighting the persistent security challenges in IoT devices.
In the evolving landscape of cybersecurity research, the discovery of vulnerabilities in Internet of Things (IoT) devices continues to reveal fundamental security challenges that manufacturers and users must confront. A recent analysis of a TP-Link router demonstrates how accessible firmware repositories combined with insufficient input validation can create critical security risks that extend beyond the immediate device to potentially compromise entire networks.
The journey began with a simple observation by security researcher MrBruh, who discovered that TP-Link firmware images were stored in an publicly accessible S3 bucket. This accessibility, while potentially convenient for legitimate purposes, also creates an attack surface for those with malicious intent. The researcher identified 90 different firmware versions for the TL-MR6400 router model, eventually narrowing down to 10 specific to the Asia-Pacific region.
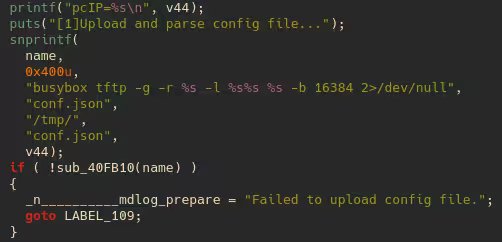
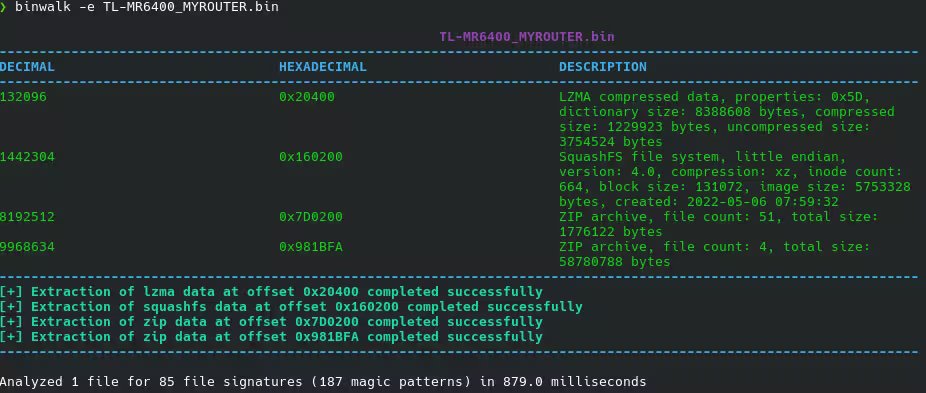 Binwalk analysis of the TP-Link firmware revealed the underlying structure
Binwalk analysis of the TP-Link firmware revealed the underlying structure
After downloading the firmware matching his router's version, the researcher employed binwalk to extract the firmware contents. This process revealed the typical structure of embedded device firmware, with the majority of TP-Link's custom binaries contained within squashfs-root/usr/bin/. The investigation focused on two critical components: httpd, which handles the web-based administration interface, and cli, which provides telnet-based administrative access.
While the httpd binary yielded limited results, the cli binary presented more promising avenues for research. Within this component, an undocumented command called 'mdlog prepare' was discovered, designed to gather diagnostic information and upload it to a user-specified TFTP server. This functionality, while seemingly innocuous, contained a critical vulnerability that could be exploited to achieve Remote Code Execution (RCE).
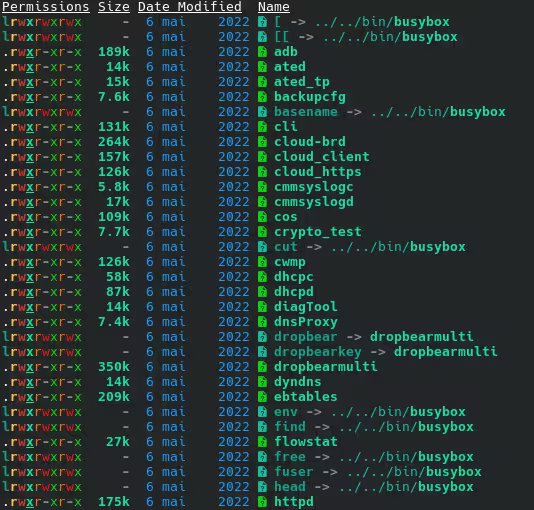 The usr/bin directory contained key TP-Link binaries including the vulnerable cli component
The usr/bin directory contained key TP-Link binaries including the vulnerable cli component
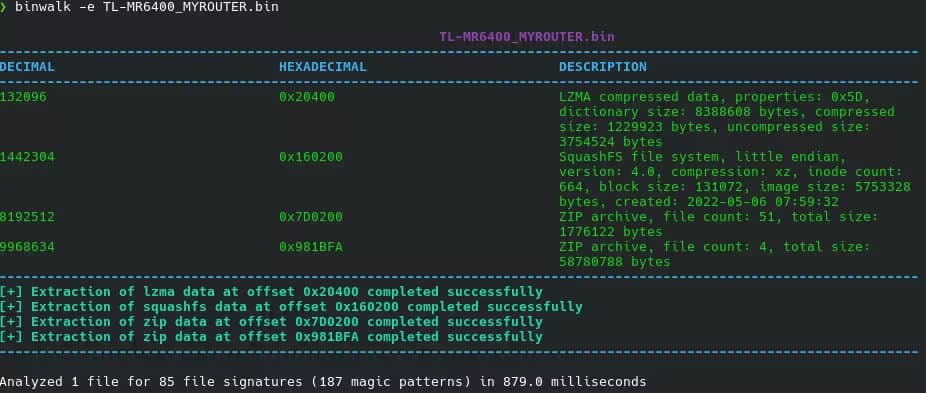
The vulnerability chain begins when the 'mdlog prepare' command retrieves the IP address of the connected telnet session and attempts to connect to a TFTP server on port 69 to download a configuration file named 'conf.json'. This JSON file is parsed using a lightweight library called cJSON, which extracts a 'router.workdir' variable. This variable is then combined with a busybox command to download a diagnostic tool from the TFTP server and execute it.
The critical flaw lies in the complete lack of input sanitization for the 'router.workdir' variable. By inserting a delimiter character such as ';', an attacker can chain additional commands after the intended operation. For instance, using a workdir value of '/tmp/x; sh; #' transforms the command execution into three separate operations:
busybox tftp -g -r mdlog_bridge.bin -l /tmp/xsh#mdlog_bridge.bin <IP> -b 16384 2>/dev/null(commented out)
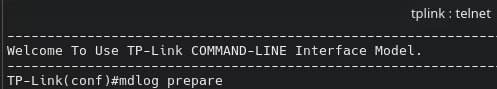 The command-line interface of the TP-Link router showing the vulnerable functionality
The command-line interface of the TP-Link router showing the vulnerable functionality
This exploitation technique effectively bypasses the intended diagnostic functionality and provides the attacker with a fully interactive root shell on the compromised device. The implications of such vulnerability are significant, as routers typically serve as gateways to entire networks, potentially exposing connected devices and sensitive data to unauthorized access.
The researcher followed responsible disclosure practices, reporting the vulnerability to TP-Link on December 24, 2025. The manufacturer acknowledged the issue, implemented a fix, and assigned CVE-2026-3841 to track the vulnerability. The patch was released on March 12, 2026, with an additional 30-day observation period before the details were made public on April 30, 2026.
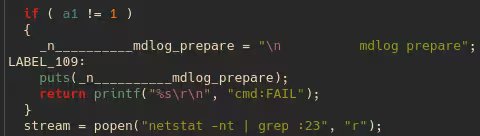 Source code snippet showing the vulnerable implementation in the cli binary
Source code snippet showing the vulnerable implementation in the cli binary
This discovery highlights several concerning patterns in IoT security that extend beyond this specific vulnerability. First, the practice of storing firmware in publicly accessible repositories creates unnecessary exposure that can be exploited by researchers and malicious actors alike. While transparency can be beneficial for security research, it must be balanced with appropriate access controls.
Second, the presence of undocumented administrative commands suggests inadequate security-by-design practices. These hidden features, often included for debugging or support purposes, can become attack vectors if not properly secured or removed from production firmware.
Third, the vulnerability demonstrates a fundamental failure in input validation—a security principle that should be non-negotiable in any software development process, particularly for devices that sit at critical network junctions.
 Further source code revealing the lack of input sanitization in the implementation
Further source code revealing the lack of input sanitization in the implementation
From a broader perspective, this research underscores the persistent challenges in securing IoT devices. Many manufacturers prioritize feature development and time-to-market over comprehensive security testing, resulting in products with vulnerabilities that can remain undiscovered for years. The open nature of firmware repositories, while potentially beneficial for legitimate research, also lowers the barrier for attackers seeking to identify and exploit weaknesses.
Users of TP-Link routers should verify whether their specific firmware version includes the patch for CVE-2026-3841 and update accordingly. For those with devices that no longer receive updates, this vulnerability serves as a reminder of the security risks associated with using outdated network equipment.
The security research community continues to play a vital role in identifying such vulnerabilities before they can be exploited maliciously. However, the ultimate responsibility lies with manufacturers to implement secure coding practices, conduct thorough security testing, and maintain ongoing support for their products throughout their lifecycle.
As our homes and workplaces become increasingly connected through IoT devices, the security of these components becomes paramount. The discovery of vulnerabilities like this one in TP-Link routers highlights the ongoing need for vigilance, both from manufacturers and the security research community, to ensure that the convenience of connected devices does not come at the cost of security.
Comments
Please log in or register to join the discussion