A security researcher has published exploit code for an unpatched Windows privilege escalation flaw after becoming frustrated with Microsoft's handling of the disclosure process.
A security researcher has published exploit code for an unpatched Windows privilege escalation flaw after becoming frustrated with Microsoft's handling of the disclosure process. The vulnerability, dubbed BlueHammer, allows attackers to gain SYSTEM or elevated administrator permissions on affected Windows systems.
The disclosure that wasn't
The researcher, operating under the alias Chaotic Eclipse, published the exploit code on GitHub on April 3rd, expressing frustration with Microsoft's Security Response Center (MSRC). In a brief post, the researcher stated, "I was not bluffing Microsoft, and I'm doing it again." The comment suggests this isn't the first time the researcher has taken such action due to dissatisfaction with Microsoft's vulnerability handling.
"Unlike previous times, I'm not explaining how this works; y'all geniuses can figure it out," the researcher added. "Also, huge thanks to MSRC leadership for making this possible."
The researcher also questioned Microsoft's decision-making process, writing, "I'm just really wondering what was the math behind their decision, like you knew this was going to happen and you still did whatever you did? Are they serious?"
Technical details of BlueHammer
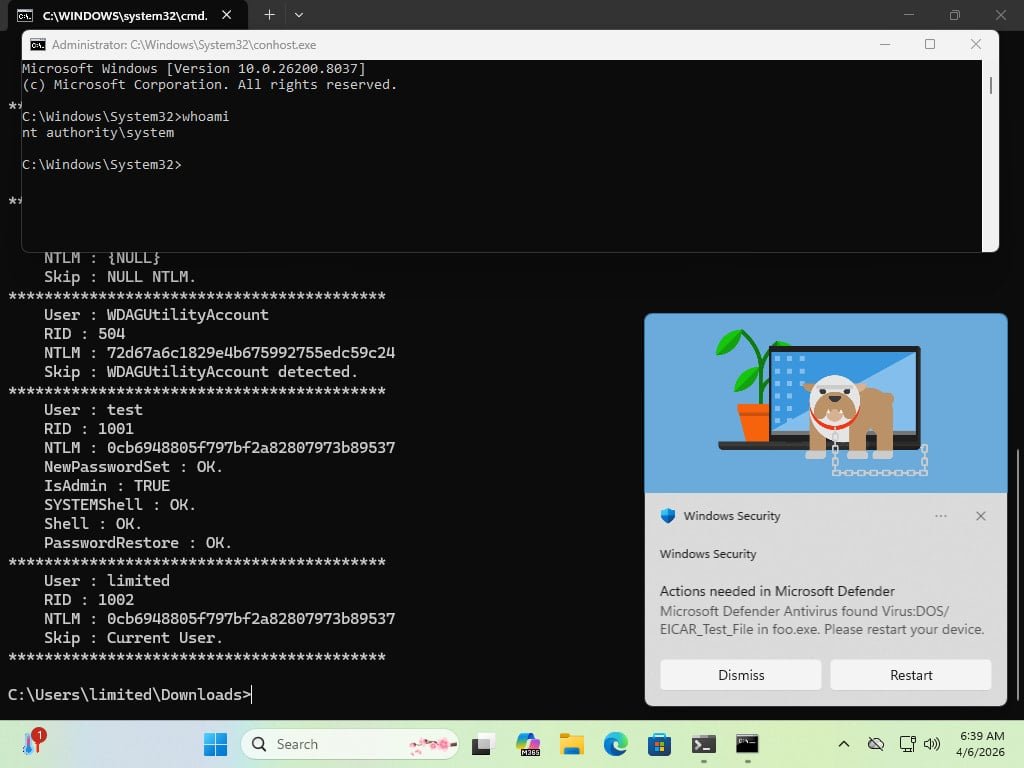
Will Dormann, principal vulnerability analyst at Tharros (formerly Analygence), confirmed to BleepingComputer that the BlueHammer exploit works. According to Dormann, the flaw is a local privilege escalation (LPE) that combines two attack techniques:
- TOCTOU (time-of-check to time-of-use) vulnerability
- Path confusion exploit
Dormann explained that while the issue isn't easy to exploit, it gives a local attacker access to the Security Account Manager (SAM) database, which contains password hashes for local accounts. With this access, attackers can escalate to SYSTEM privileges and potentially achieve complete machine compromise.
"At that point, [the attackers] basically own the system, and can do things like spawn a SYSTEM-privileged shell," Dormann told BleepingComputer.
Limitations and platform differences
Some researchers testing the exploit confirmed that the code was not successful on Windows Server platforms. This confirms the researcher's statement that there are bugs that may prevent it from working properly. On Server platforms, the BlueHammer exploit increases permissions from non-admin to elevated administrator, a protection that requires the user to temporarily authorize an operation that needs full access to the system.
Dormann noted that one requirement from MSRC when submitting a vulnerability is to provide a video of the exploit. While this may help Microsoft sift through reported vulnerabilities more easily, it adds to the effort of submitting a valid report.
Microsoft's response
BleepingComputer has contacted Microsoft for a comment on the BlueHammer flaw. A Microsoft spokesperson provided the following statement:
"Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible. We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community."
Risk assessment
While BlueHammer requires a local attacker to exploit it, the risk it poses is still significant. Hackers can gain local access through various vectors, including:
- Social engineering attacks
- Leveraging other software vulnerabilities
- Credential-based attacks
- Physical access to systems
Related security updates
This incident comes amid ongoing concerns about Windows security. Recent Patch Tuesday updates have addressed multiple zero-day vulnerabilities:
- Microsoft March 2026 Patch Tuesday fixed 2 zero-days and 79 flaws
- Microsoft February 2026 Patch Tuesday fixed 6 zero-days and 58 flaws
- Google reported that 90 zero-days were exploited in attacks last year
The BlueHammer disclosure highlights the ongoing tension between security researchers and software vendors, particularly around disclosure timelines and the handling of critical vulnerabilities. With no official patch available, organizations running affected Windows systems should monitor for updates and implement additional security controls to limit local attack vectors.
Comments
Please log in or register to join the discussion