Insyde's SecureBoot bypass fix for Hydroph0bia addresses the immediate vulnerability but relies on NVRAM variables that remain vulnerable to physical attacks and potential bypasses.
This is the final installment of my Hydroph0bia series, examining how Insyde addressed the massive SecureBoot bypass vulnerability (CVE-2025-4275) that affected countless UEFI systems. After 10 days since embargo lift, only Dell has delivered working BIOS updates, while Lenovo promises fixes by July 30th and Framework remains silent.
The Fix Analysis
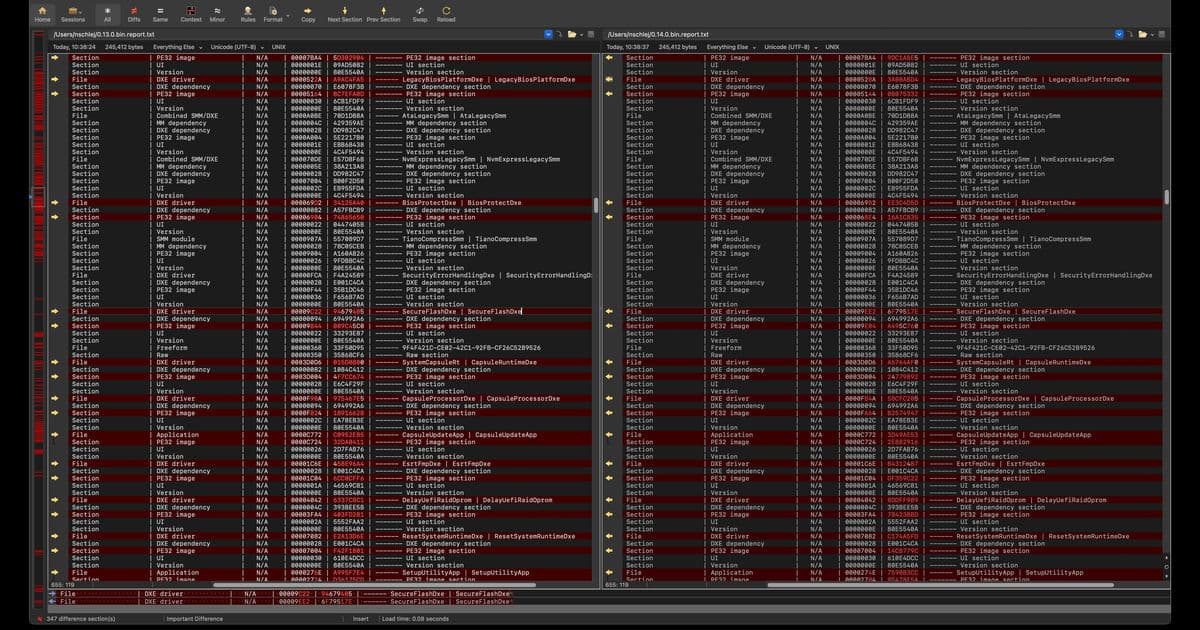
To understand Insyde's approach, I compared Dell's pre-fix (0.13.0) and post-fix (0.14.0) BIOS updates using InsydeImageExtractor and UEFITool reports. The most significant changes appeared in SecureFlashDxe, which gained 704 bytes of new code.
What Changed
BdsDxe: Replaced direct gRT->SetVariable calls with LibSetSecureVariable, preventing special Insyde variables with AW attribute from being set.
SecurityStubDxe: Fixed an ExitBootServices handler that previously called gBS->CloseEvent on itself - a change unrelated to Hydroph0bia but potentially breaking if attackers could somehow set SecureFlashCertData.
SecureFlashDxe: The main fix includes:
- Same
LibSetSecureVariablereplacement as BdsDxe - Same ExitBootServices handler fix
- New variable removal at entry point to prevent SecureFlashSetupMode and SecureFlashCertData from persisting
- Added VariablePolicy protection for both variables
The Problem with the Fix
The VariablePolicy implementation, while newer than InsydeVariableLock, appears vulnerable to the same "flip a global variable to disable the whole thing" attack we used in Part 2. Without hardware to test, I can't confirm this, but the architecture remains fundamentally flawed.
Physical Attack Vectors Still Work
Manual NVRAM editing via SPI programming hardware or flash write protection bypasses can still set SecureFlashCertData in ways that bypass both VariablePolicy and LibSetSecureVariable. Physical attacks are technically out of scope for SecureBoot bypass discussions since all trusted variables reside in the same physical storage, but this leaves firmware updaters vulnerable to certificate hijacking.
The Better Solution
There's a cleaner approach that Insyde apparently attempted but abandoned due to regressions: stop using NVRAM for security-sensitive applications. SecureFlashCertData doesn't need to live in BdsDxe, CapsuleRuntimeDxe, or other drivers. SecurityStubDxe could simply:
- React to SecureFlashSetupMode trigger
- Load certificates into memory once using LoadCertificateToVariable
- Use them directly from memory for Authenticode verification
The only potential regression would affect OEMs who blindly copied this mechanism into custom drivers, but security updates shouldn't be held back by backward compatibility concerns.
Insyde's Response
I contacted Tim Lewis (Insyde CTO) about the fix's limitations and received this reply from Kevin Devis (Insyde Security Strategist):
"We started on a fix based on your feedback. Unfortunately we ran into some regression issues and decided to fix 'the easy way' for now. In addition, we are creating an ECR for an engineer to investigate a solution that will not use variables. This way we mitigate the issue for now and improve the codebase even more later. It might take 6 months or so."
It's refreshing to see an IBV actively engaging in responsible disclosure, coordinating fixes, and communicating transparently about limitations and future plans.
What's Next
I've acquired an Acer Swift Go 16 as my test platform for further Insyde H2O investigations. While it lacks the Hydroph0bia fix, it properly protects the DXE volume using FlashDeviceMap, which Intel BootGuard secures. I'm curious whether Acer introduced additional vulnerabilities beyond Insyde's baseline.
Acknowledgments
Thanks to Dell's security team for being first to deliver fixes, and to Tim Lewis, Kevin Devis, and the entire Insyde security team for their collaboration and transparency throughout this process.
Resources: Unwrapped Dell G15 5535 firmware images (0.13.0 and 0.14.0), UEFITool reports, and extracted driver binaries are available on GitHub for independent analysis.
Comments
Please log in or register to join the discussion