OpenAI has addressed two significant security vulnerabilities in its AI platforms, including a ChatGPT data exfiltration flaw and a Codex command injection issue that could compromise GitHub tokens.
OpenAI has recently patched two critical security vulnerabilities in its AI platforms that could have allowed attackers to exfiltrate sensitive conversation data and steal GitHub authentication tokens. The discoveries highlight growing security challenges as AI systems become more deeply integrated into enterprise workflows and handle increasingly sensitive information.
ChatGPT Data Exfiltration Vulnerability
A previously unknown vulnerability in OpenAI ChatGPT allowed sensitive conversation data to be exfiltrated without user knowledge or consent, according to findings from Check Point Research. "A single malicious prompt could turn an otherwise ordinary conversation into a covert exfiltration channel, leaking user messages, uploaded files, and other sensitive content," the cybersecurity company explained in its report.
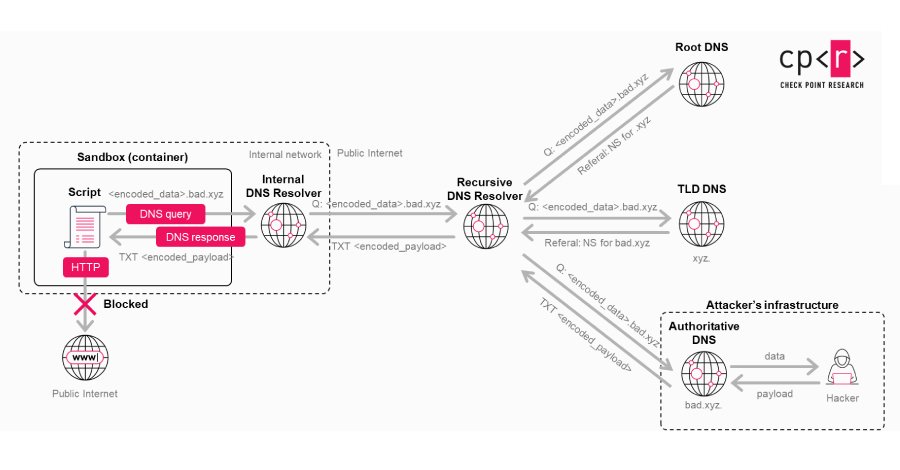
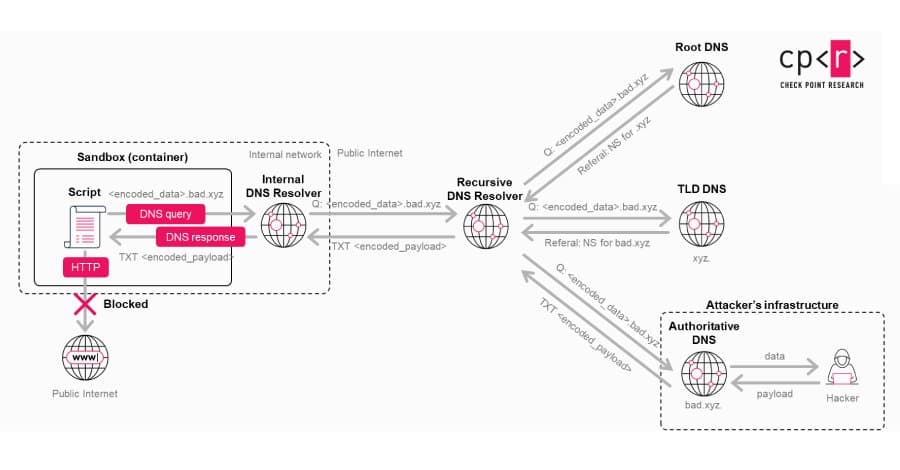
The vulnerability bypassed ChatGPT's built-in guardrails by exploiting a side channel in the Linux runtime used by the AI agent for code execution and data analysis. Specifically, it abused a hidden DNS-based communication path as a "covert transport mechanism" by encoding information into DNS requests to circumvent visible AI safeguards.
"What's more, the same hidden communication path could be used to establish remote shell access inside the Linux runtime and achieve command execution," Check Point researchers noted. "In the absence of any warning or user approval dialog, the vulnerability creates a security blind spot, with the AI system assuming that the environment was isolated."
As an example, an attacker could convince a user to paste a malicious prompt by passing it off as a way to unlock premium capabilities for free or improve ChatGPT's performance. The threat becomes even more significant when the technique is embedded inside custom GPTs, as the malicious logic could be baked into it rather than requiring user interaction.
"Crucially, because the model operated under the assumption that this environment could not send data outward directly, it did not recognize that behavior as an external data transfer requiring resistance or user mediation," Check Point explained. "As a result, the leakage did not trigger warnings about data leaving the conversation, did not require explicit user confirmation, and remained largely invisible from the user's perspective."
Following responsible disclosure, OpenAI addressed the issue on February 20, 2026. There is no evidence that the vulnerability was ever exploited in a malicious context.
Codex GitHub Token Vulnerability
Simultaneously, BeyondTrust Phantom Labs discovered a critical command injection vulnerability in OpenAI's Codex, a cloud-based software engineering agent, that could have been exploited to steal GitHub credential data and compromise multiple users interacting with shared repositories.
"The vulnerability exists within the task creation HTTP request, which allows an attacker to smuggle arbitrary commands through the GitHub branch name parameter," BeyondTrust researcher Tyler Jespersen explained. "This can result in the theft of a victim's GitHub User Access Token – the same token Codex uses to authenticate with GitHub."
The issue stems from improper input sanitization when processing GitHub branch names during task execution on the cloud. An attacker could inject arbitrary commands through the branch name parameter in an HTTPS POST request to the backend Codex API, execute malicious payloads inside the agent's container, and retrieve sensitive authentication tokens.
"This granted lateral movement and read/write access to a victim's entire codebase," Kinnaird McQuade, chief security architect at BeyondTrust, noted. The vulnerability affects the ChatGPT website, Codex CLI, Codex SDK, and the Codex IDE Extension.
BeyondTrust researchers demonstrated that the branch command injection technique could also be extended to steal GitHub Installation Access tokens and execute bash commands on the code review container whenever @codex is referenced in GitHub. "With the malicious branch set up, we referenced Codex in a comment on a pull request (PR)," they explained. "Codex then initiated a code review container and created a task against our repository and branch, executing our payload and forwarding the response to our external server."
OpenAI patched this vulnerability on February 5, 2026, after it was reported on December 16, 2025.
Expert Perspectives
The discoveries come at a time when threat actors have been observed publishing web browser extensions that engage in "prompt poaching" to silently siphon AI chatbot conversations without user consent.
"These plugins open the doors to several risks, including identity theft, targeted phishing campaigns, and sensitive data being put up for sale on underground forums," Expel researcher Ben Nahorney warned. "In the case of organizations where employees may have unwittingly installed these extensions, they may have exposed intellectual property, customer data, or other confidential information."
Eli Smadja, head of research at Check Point Research, emphasized the need for organizations to rethink their security approach in the AI era. "This research reinforces a hard truth for the AI era: don't assume AI tools are secure by default," Smadja stated. "As AI platforms evolve into full computing environments handling our most sensitive data, native security controls are no longer sufficient on their own. Organizations need independent visibility and layered protection between themselves and AI vendors."
BeyondTrust highlighted the growing risk where privileged access granted to AI coding agents can be weaponized to provide a "scalable attack path" into enterprise systems without triggering traditional security controls.
"As AI agents become more deeply integrated into developer workflows, the security of the containers they run in – and the input they consume – must be treated with the same rigor as any other application security boundary," BeyondTrust researchers concluded. "The attack surface is expanding, and the security of these environments needs to keep pace."
Practical Recommendations
With tools like ChatGPT increasingly embedded in enterprise environments and users uploading highly personal information, organizations should consider implementing the following security measures:
Implement a security layer between users and AI tools: Organizations need independent visibility and layered protection rather than relying solely on native security controls.
Review browser extensions: Audit all browser extensions, particularly those interacting with AI platforms, to ensure they don't engage in data exfiltration.
Apply prompt injection defenses: Implement additional safeguards against prompt injection techniques that could bypass AI guardrails.
Secure AI agent containers: Treat the security of containers used by AI agents with the same rigor as any other application security boundary.
Monitor AI interactions: Implement monitoring systems that can detect unusual behavior or data exfiltration attempts through AI systems.
Regular security assessments: Conduct regular security assessments of AI integrations and custom GPTs to identify potential vulnerabilities.
Input validation: Ensure proper input sanitization is implemented in all AI integrations, particularly those that interact with external systems like GitHub.
As AI systems continue to evolve and become more deeply integrated into enterprise workflows, these vulnerabilities underscore the importance of approaching AI security with the same seriousness as traditional application security. The patches from OpenAI represent positive steps, but organizations must remain vigilant and implement their own security layers to protect against the unique threats posed by AI systems.
Comments
Please log in or register to join the discussion