Passwords remain fundamentally insecure at age 65, with new vulnerabilities in password managers, AI-generated credentials, and flawed implementations of alternatives like passkeys creating urgent digital rights concerns.
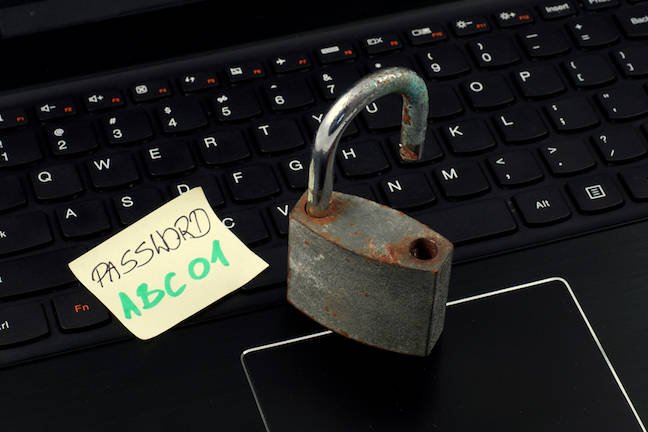
Sixty-five years after passwords debuted with MIT's Compatible Time-Sharing System, these authentication relics continue to dominate digital security despite mounting evidence of their inadequacy. Recent developments reveal alarming vulnerabilities across the authentication landscape, undermining user privacy and digital sovereignty.
The Password Manager Paradox Cloud-based password managers from Apple and Google – used by most consumers – introduce critical sovereignty risks. As US companies, they must comply with government demands to revoke access, potentially leaving users permanently locked out of their digital lives. Research also reveals architectural weaknesses in password managers previously thought invulnerable, enabling credential theft through sophisticated attacks.
AI's Dangerous Illusions When users request "strong passwords" from AI tools, large language models often generate credentials that appear secure but contain predictable patterns vulnerable to brute-force attacks. Even when password managers generate credentials internally, opaque algorithms make verification impossible. This creates false confidence in fundamentally weak authentication methods.
Agentic AI: The New Frontier of Risk Emerging agentic AI systems compound these problems by requiring broad access to user accounts. Without industry standards for privilege isolation, users must surrender credentials to AI agents – effectively creating master keys for malicious actors. The chaotic emergence of frameworks like OpenClaw demonstrates how rapidly these risks scale across interconnected systems.
Broken Promises of Alternatives While biometrics and hardware-bound PINs work reasonably well on individual devices, their extension to online services remains problematic:
- Two-Factor Authentication (2FA): SMS-based 2FA remains vulnerable to SIM-swapping, while authenticator apps fail when devices are lost. Physical security keys suffer from inconsistent platform support.
- Passkeys: Though cryptographically sound in theory, real-world implementations confuse users. Services inconsistently support them, while cloud-syncing options contradict the technology's device-bound purpose. When platforms like Apple omit fingerprint sensors from desktop devices, biometric fallbacks disappear.
The Standardization Imperative These failures stem from industry fragmentation. Major platforms refuse to adopt common authentication standards, prioritizing proprietary ecosystems over user security. Without unified terminology, consistent user interfaces, and mandatory security education, alternatives like passkeys remain inaccessible to non-technical users.
Digital sovereignty requires authentication systems users can truly control. Until manufacturers commit to cross-platform standards and transparent credential management – rather than chasing AI trends with inherent security risks – the password crisis will only deepen.
Further Reading

Comments
Please log in or register to join the discussion