A wiper attack on Stryker medical equipment manufacturer exploited Microsoft Intune's remote wipe capabilities, raising questions about enterprise security tools being weaponized by attackers.
A sophisticated cyberattack on Stryker, a major medical technology company, has exposed a concerning vulnerability in enterprise device management systems. According to sources cited by Brian Krebs, the perpetrators of a wiper attack on Stryker appear to have used Microsoft Intune to issue a "remote wipe" command against all connected devices, effectively leveraging the company's own security infrastructure against it.
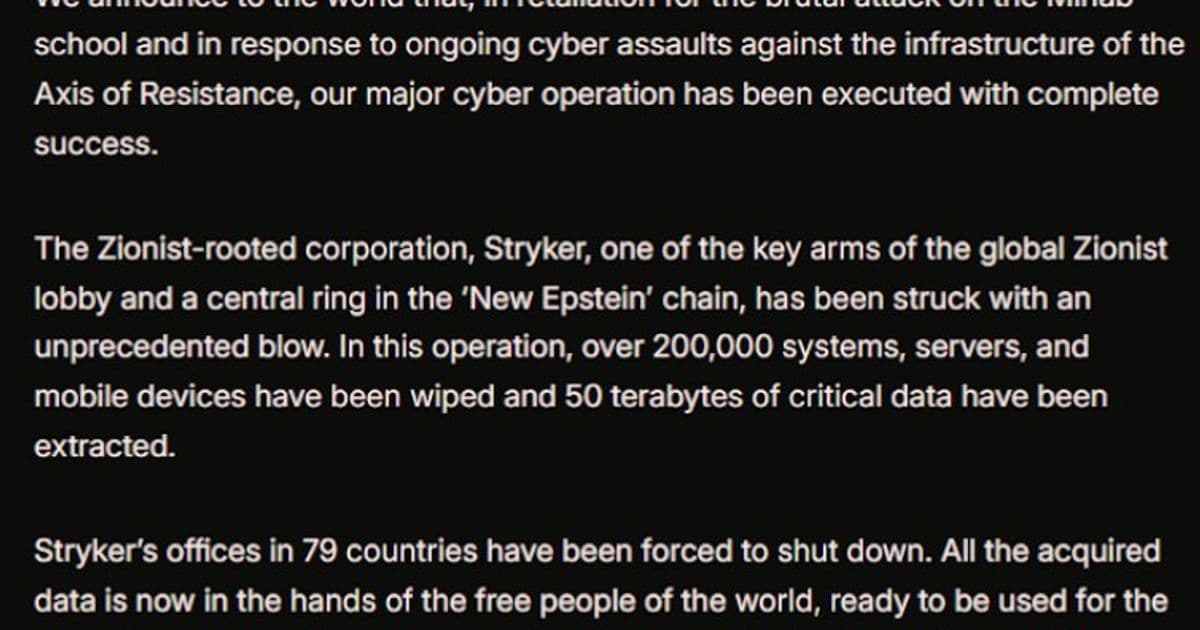
The attack, claimed by a hacktivist group with links to Iran's intelligence agencies, demonstrates how enterprise security tools designed to protect organizations can be weaponized when attackers gain administrative access. Microsoft Intune is a cloud-based service for mobile device management that allows IT administrators to remotely wipe devices, enforce security policies, and manage software deployments across an organization's fleet of devices.
This incident highlights a fundamental tension in cybersecurity: the same tools that enable organizations to respond to device loss or employee termination can be exploited by attackers who compromise those administrative privileges. When attackers gained sufficient access to Stryker's systems, they were able to trigger a company-wide wipe that likely disrupted operations and potentially destroyed critical data.
The use of Microsoft Intune in this attack raises several important questions about enterprise security architecture. Organizations must balance the convenience and control that centralized device management provides against the risk of those controls being turned against them. The attack suggests that Stryker's attackers achieved a level of access that allowed them to impersonate legitimate administrators or compromise the Intune service itself.
This is not an isolated incident. Similar attacks have been documented where ransomware groups and nation-state actors have exploited enterprise management tools. The trend reflects a broader shift in cyberattack methodology, where adversaries are increasingly targeting the administrative controls and management infrastructure that organizations rely on for security.
For Microsoft, this incident presents a reputational challenge. While Intune is designed with security in mind, including authentication requirements and audit logging, the attack demonstrates that even sophisticated enterprise tools can be misused when attackers achieve sufficient compromise. The company may need to consider additional safeguards or anomaly detection capabilities to prevent unauthorized use of remote wipe functions.
From a defensive perspective, organizations using Microsoft Intune and similar tools should review their access controls, implement multi-factor authentication for administrative functions, and consider additional monitoring for unusual device management activity. The incident also underscores the importance of network segmentation and the principle of least privilege in enterprise environments.
The Stryker attack serves as a cautionary tale about the double-edged nature of enterprise security tools. While these platforms provide essential capabilities for managing modern device fleets, they also create potential attack vectors that sophisticated adversaries can exploit. As organizations continue to adopt cloud-based management solutions, understanding and mitigating these risks becomes increasingly critical.
This incident may prompt other organizations to reevaluate their device management strategies and consider whether additional safeguards are needed to prevent their own security infrastructure from being turned against them. The balance between operational efficiency and security resilience remains a central challenge in enterprise cybersecurity.
Comments
Please log in or register to join the discussion