A Brazilian cybersecurity professional purchased what appeared to be a legitimate Ledger Nano S+ hardware wallet from a Chinese marketplace, only to discover it was an elaborate counterfeit designed to steal cryptocurrency through malicious software and command-and-control servers.
A Brazilian cybersecurity professional recently purchased what he believed to be a legitimate Ledger Nano S+ hardware wallet from a major Chinese marketplace, only to discover he had nearly fallen victim to an elaborate phishing scheme that could have cost him his cryptocurrency holdings.
Joje Mendes, who works in cybersecurity, decided to order the device while located in Shenzhen, China. Importing directly from Ledger as a non-Chinese citizen "comes with its own headaches," he explained, so he opted for what appeared to be a legitimate marketplace purchase at the same price as an official unit.
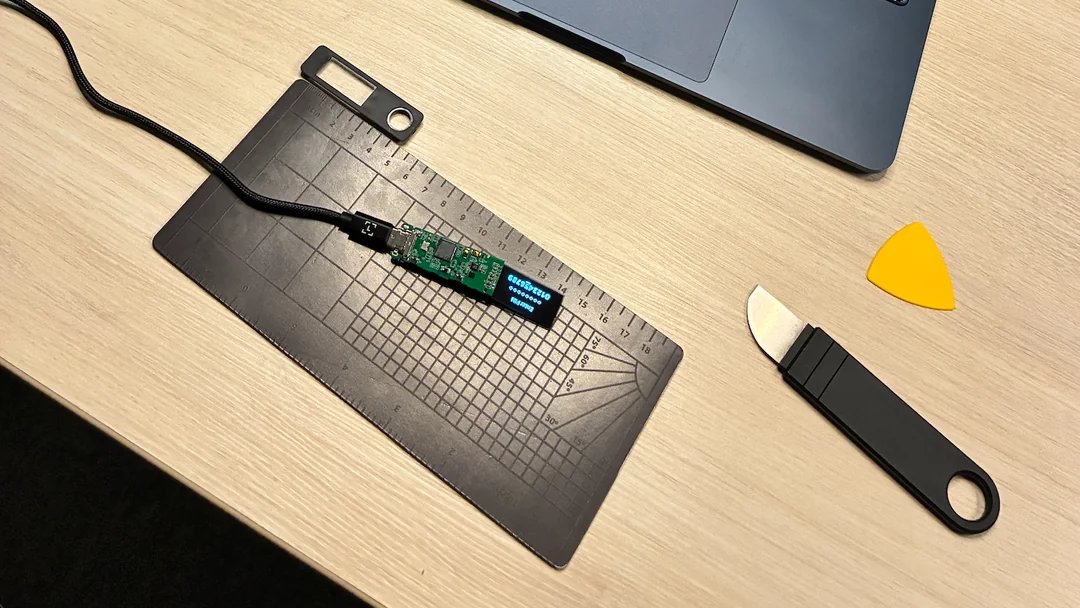
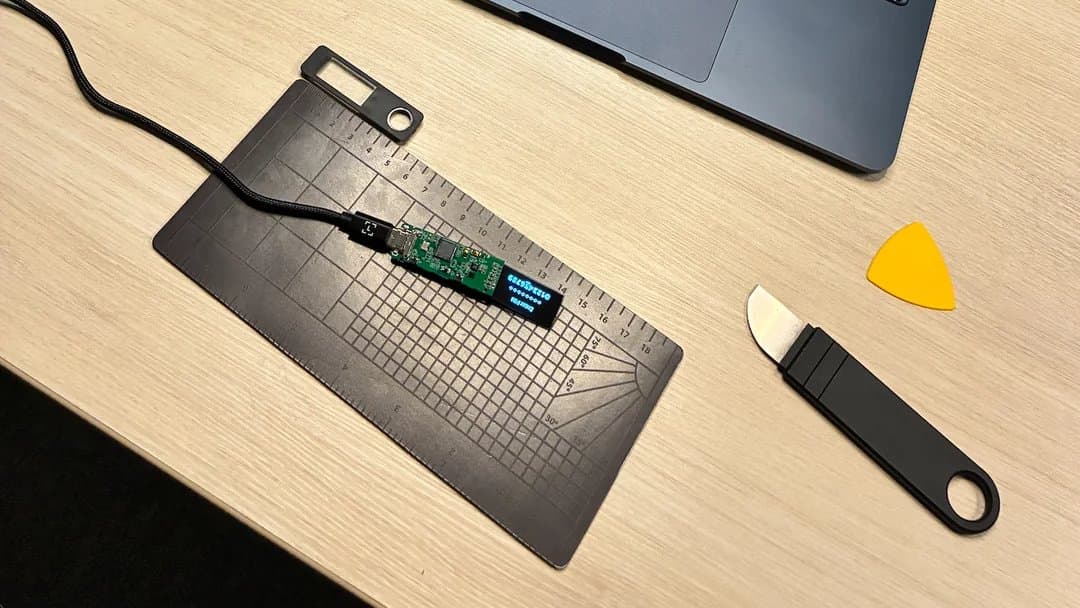
(Image credit: Joje Mendes)
Before the device even arrived, Mendes demonstrated proper security hygiene by installing Ledger's official software in advance. This precaution proved crucial when the hardware wallet arrived and he immediately noticed it was "clearly" a counterfeit. The Ledger software itself flagged the device as non-genuine, preventing any potential compromise of his actual cryptocurrency.
Rather than simply discarding the fake device, Mendes's professional curiosity led him to dismantle it completely. What he discovered was a sophisticated operation involving multiple layers of deception designed to harvest cryptocurrency from unsuspecting users.
Upon opening the case, Mendes found that all chip markings had been deliberately scraped off to prevent identification. Through careful analysis, he determined the central processing unit was an ESP32-S3 system-on-a-chip. The counterfeit device was programmed to spoof its identification, claiming to be a "Nano S+ 7704" manufactured at Ledger's factory, complete with a fabricated serial number.
The firmware analysis revealed particularly troubling findings. Mendes discovered test PIN codes and seed phrases for two cryptocurrency wallets already programmed into the device. Even more concerning were hard-coded credentials that connected the device to command-and-control (C2) servers designed to exfiltrate sensitive data.
Initially, Mendes suspected the device might use Wi-Fi or Bluetooth capabilities to transmit stolen data when connected to public networks, or perhaps employ a USB keylogger function. However, the actual attack vector proved even more insidious.
The counterfeit operation relies primarily on a fake Ledger application that users are directed to download. This malicious software presents itself as legitimate Ledger software but contains multiple layers of surveillance and data harvesting capabilities. The app is signed with an Android Debug certificate, tracks device location even after being closed, and continuously sends data to the C2 servers.
The attack chain begins with tainted QR codes, presumably printed on the device packaging or included paper instructions. Users scanning these codes are directed to websites that closely mimic ledger.com, where they download the malicious applications for Android, Windows, or macOS platforms.
Adding another layer of sophistication, the counterfeit firmware monitors account balances through public keys. This feature allows the attackers to receive real-time notifications when funds are deposited, essentially letting them "hear a ka-ching! sound" whenever victims add cryptocurrency to their compromised wallets.
Mendes believes this counterfeit hardware is specifically targeted at first-time cryptocurrency users seeking the enhanced security that hardware wallets provide. The attack's effectiveness is particularly concerning because even experienced users might be tempted to use the download link provided on the packaging rather than navigating directly to ledger.com, especially when tired or in a hurry.
The discovery highlights a growing trend in cryptocurrency-related cybercrime where attackers combine hardware counterfeiting with sophisticated software-based phishing attacks. This multi-layered approach makes detection significantly more difficult for average users who may not have the technical expertise to identify subtle discrepancies.
Ledger has been notified of this elaborate phishing operation, and Mendes has vowed to purchase additional devices to investigate how widespread this counterfeiting scheme might be. The level of effort involved in creating these fake devices suggests a well-resourced operation rather than opportunistic criminals.
This incident serves as a stark reminder about the importance of purchasing hardware security devices only from official manufacturers or authorized resellers. The convenience of marketplace purchases, even from seemingly reputable sources, can come with significant security risks when dealing with devices designed to protect valuable digital assets.
The sophistication of this attack also underscores the need for enhanced verification mechanisms in the cryptocurrency hardware wallet industry. As these devices become more mainstream, the incentive for creating convincing counterfeits will only increase, potentially putting millions of users' assets at risk.
For cryptocurrency users, the lessons are clear: always purchase hardware wallets directly from manufacturers, verify device authenticity through official software, and never trust download links or QR codes provided with third-party purchases. The combination of hardware and software verification remains the best defense against these evolving threats.
As the cryptocurrency market continues to mature, incidents like this highlight the ongoing arms race between security professionals and cybercriminals. The fact that a cybersecurity expert nearly fell victim to this scheme demonstrates how convincing these attacks have become, making vigilance and proper security practices more critical than ever for protecting digital assets.
Comments
Please log in or register to join the discussion