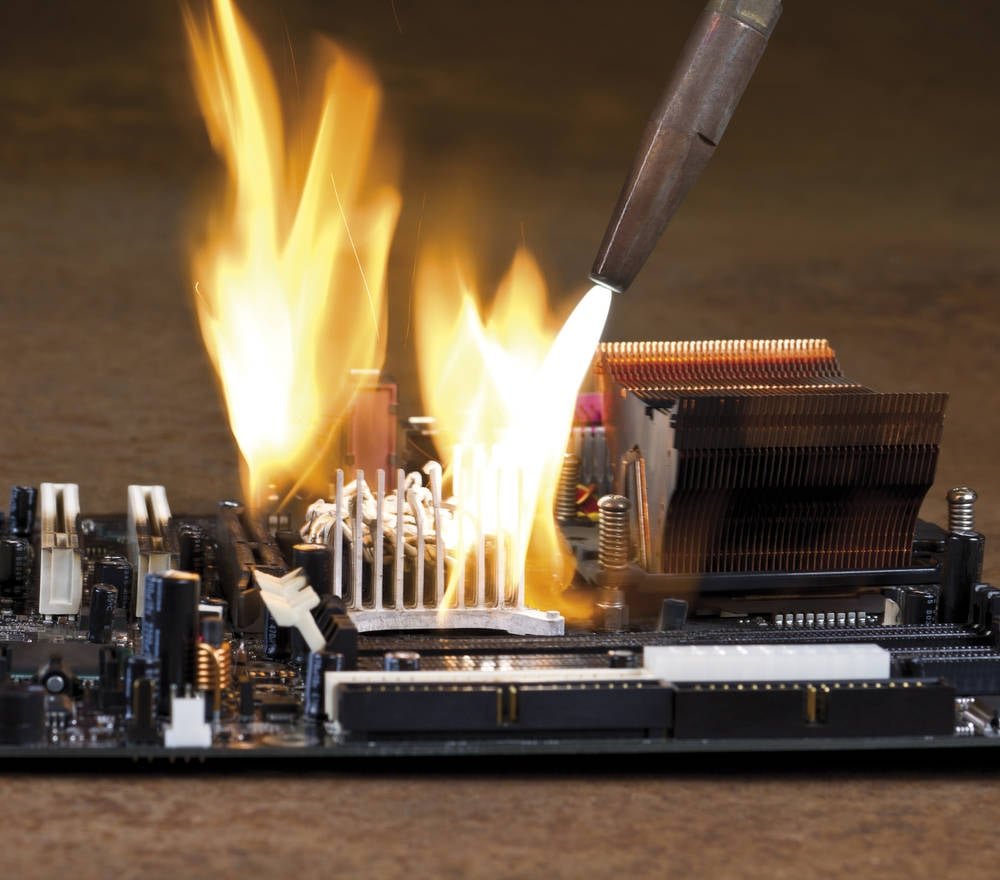
Security researchers reveal that Vect ransomware, used in recent supply chain attacks, actually destroys rather than encrypts large files, rendering ransom payments futile for victims.
Organizations hit by the recent wave of supply chain compromises involving Trivy and LiteLLM who paid ransoms to the Vect criminal group likely received little to no data in return, according to new research from Check Point Research. The disturbing finding is that Vect's so-called 'ransomware' is actually a wiper that permanently destroys any file larger than 128KB, making data recovery impossible for both victims and the attackers themselves.
The Vect-TeamPCP Partnership
Vect has emerged as one of the key crime crews partnering with TeamPCP to leak data and extort victims of ongoing attacks that have compromised major security and developer tools including Trivy, LiteLLM, Checkmarx, and Telnyx. After initially compromising these tools with self-propagating credential-stealing malware, the two groups announced their partnership on BreachForums, boasting that they would 'pull off even bigger supply chain operations' and 'chain these compromises into devastating follow-on ransomware campaigns.'
The collaboration extends to Vect's partnership with the BreachForums data leak site itself, where every registered user can access Vect's ransomware, negotiation platform, and according to researchers, a flawed malware builder.
Technical Analysis: Not Ransomware, But a Wiper
Check Point researchers opened a BreachForums account to gain access to Vect's panel and ransomware builder, allowing them to analyze the gang's malware. Their findings reveal that Vect's offerings are technically amateurish, with researchers describing the code as 'not technically sophisticated' and exhibiting 'amateur execution.'
The critical flaw is that Vect 2.0 ransomware doesn't actually encrypt files larger than 131,072 bytes (128 KB). Instead, it permanently destroys them. As Check Point analysts noted, 'Full recovery is impossible for anyone, including the attacker.' At such a low threshold, this effectively makes Vect a wiper for virtually any file containing meaningful data, including enterprise assets such as VM disks, databases, documents, and backups.
The ransomware, as advertised, includes Windows, Linux, and ESXi variants. All share the same encryption design built on libsodium, the same file-size thresholds, and the same critical flaw: the encryption implementation discards three of four decryption nonces for every file larger than 128 KB. This means even if victims pay the ransom, they cannot recover their files.
Legal Implications and Regulatory Considerations
The Vect operation raises significant legal questions under various data protection regulations:
GDPR (General Data Protection Regulation): Organizations affected by Vect attacks face potential violations under GDPR's data processing principles and security requirements. Article 32 specifically requires appropriate technical measures to ensure a level of security appropriate to the risk, including protection against unauthorized or unlawful processing and accidental loss, destruction, or damage.
CCPA (California Consumer Privacy Act): Similar to GDPR, the CCPA requires businesses to implement reasonable security procedures and practices to protect personal information. A breach resulting from inadequate security measures could lead to penalties.
Notification Requirements: Under GDPR and various state laws, organizations must notify affected individuals and regulators within specific timeframes following a data breach. The destruction of data by Vect complicates breach notification processes.
The European Data Protection Board (EDPB) has consistently emphasized that organizations must implement appropriate technical and organizational measures to protect personal data, with failure to do potentially resulting in fines up to 4% of global annual turnover under GDPR.
Impact on Affected Organizations
Vect's leak site lists 25 organizations since January, with four listed since March when the supply chain attacks began. While it's unclear how many of these are tied to Trivy and LiteLLM compromises, the group claimed two larger victims in April: Guesty (700GB) and S&P Global (250GB), allegedly tied to TeamPCP compromises.
For organizations that have paid ransoms, the implications are particularly severe:
- Financial loss from ransom payments without data recovery
- Potential regulatory fines for data protection failures
- Reputational damage from the breach itself
- Operational disruption from data loss
- Increased insurance premiums following a ransomware incident
According to Check Point, the Vect authors 'know what features a professional ransomware tool should have, but demonstrably struggled to implement them correctly or at all.' Beyond the nonce-handling flaw, researchers identified 'multiple other bugs and design failures' across all ransomware variants.
Recommendations for Organizations
Given the Vect threat and similar supply chain attacks, organizations should consider the following measures:
Implement robust backup strategies: Ensure regular, offline backups of critical data to enable recovery without paying ransoms.
Supply chain security: Vet third-party vendors and dependencies thoroughly, focusing on their security practices and incident response capabilities.
Network segmentation: Limit the potential spread of ransomware across networks to contain damage.
Employee training: Educate staff about phishing and social engineering tactics commonly used in initial access attacks.
Incident response planning: Develop and regularly test incident response plans specifically for ransomware scenarios.
Legal consultation: Engage legal counsel familiar with data protection regulations to ensure compliance in the event of a breach.
Broader Implications for Cybersecurity
The Vect case highlights several concerning trends in the evolving threat landscape:
The blurring lines between ransomware and wiper malware: As seen with NotPetya and now Vect, the distinction between data destruction and extortion is becoming increasingly unclear.
Supply chain attacks as primary vectors: Compromising legitimate software and development tools provides attackers with trusted access to multiple victims simultaneously.
RaaS (Ransomware-as-a-Service) democratization: Platforms like BreachForums are making ransomware capabilities accessible to less technically sophisticated actors.
Technical incompetence in cybercrime: Even established criminal groups can make fundamental errors in their malware, potentially creating opportunities for defenders.
As organizations continue to grapple with these evolving threats, the importance of robust security measures, comprehensive backup strategies, and clear incident response procedures cannot be overstated. The Vect case serves as a stark reminder that paying ransoms is not only ethically questionable but may also be technologically futile when dealing with wiper malware disguised as ransomware.

Comments
Please log in or register to join the discussion