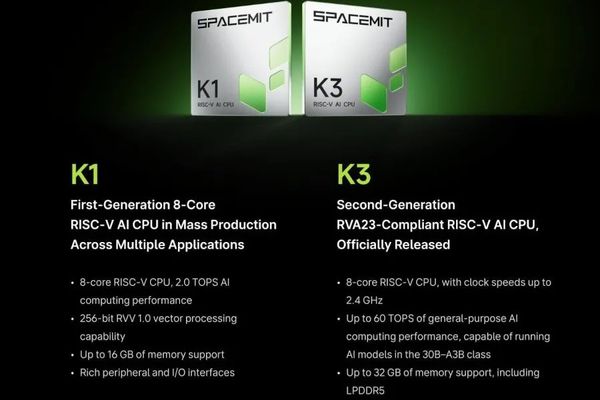
Chips
Ubuntu Embraces SpacemiT K3: First RVA23-Compliant RISC-V SoC Support Arrives
2/6/2026
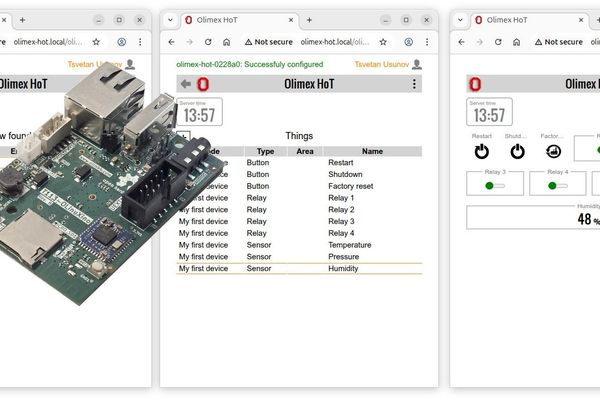
Hardware
The Minimalist's Smart Home: Olimex HoT and the Pursuit of Accessible Automation
2/6/2026

Mobile
Epic Games Store Launches Botany Manor as Free Mobile Game for Limited Time
2/6/2026

Privacy
Study Finds Chrome's Manifest v3 Update Doesn't Weaken Ad Blockers, Upholding User Privacy
2/6/2026

Hardware
Anycubic Kobra X Redefines Entry-Level Multicolor 3D Printing with Integrated ACE Gen 2 System
2/6/2026
Cloud
Microsoft Sets April 2027 Deadline to Retire Exchange Online EWS API
2/5/2026
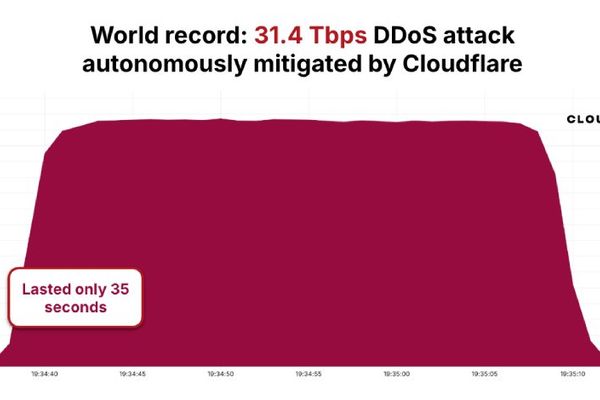
Cybersecurity
AISURU/Kimwolf Botnet Shatters Records with 31.4 Tbps DDoS Attack
2/5/2026

Hardware
Budget 1080p Gaming PC Deal: MSI Codex R2 with RTX 5060 for Under $1000
2/5/2026
Privacy
LinkedIn's Massive Chrome Extension Fingerprinting: What It Means for Privacy
2/5/2026

Regulation
Amazon's Q4 2025 Results Show Strong Growth, But AI Investment Concerns Weigh on Stock
2/5/2026
Regulation
FCC Opens Musk's 1M-Satellite DC Plan for Public Comment
2/5/2026

AI
The LLM Spectrum: Finding the Sweet Spot Between Manual Coding and AI Delegation
2/5/2026
Security
Cloudflare Security Check at Axios
2/5/2026