
Security
GNU C Library 2.43 Ships with ISO C23 Support, Memory Sealing, and Architectural Optimizations
1/24/2026

Security
Reddit's New API Rate Limits and Developer Token Requirements Spark Community Discussion
1/24/2026
Security
Reddit API Changes: How Network Security Blocks Are Affecting Developers and Community Bots
1/24/2026

Security
North Korean Hackers Deploy AI-Generated PowerShell Malware to Target Blockchain Engineers
1/24/2026
Security
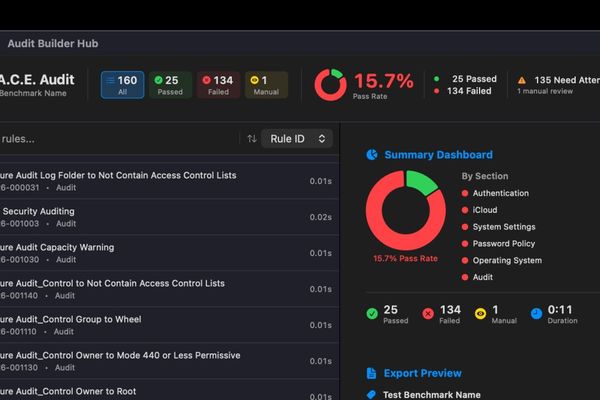
M.A.C.E. App Bridges the Gap Between Complex Security Standards and Everyday Mac Management
1/24/2026

Security
China's PLA Demonstrates 200-Unit AI Drone Swarm Controlled by a Single Operator
1/24/2026

Security
Reddit's New API Access Tiers and Developer Token Requirements
1/24/2026

Security
Reddit's New API Rate Limiting and Blocking Measures Spark Developer Backlash
1/24/2026
Security
The TechBeat: Third-Party Risks in 2026: Outlook and Security Strategies (1/24/2026)
1/24/2026

Security
Multi-Stage Phishing Campaign Targets Russia with Amnesia RAT and Ransomware
1/24/2026
Security
ACM Digital Library Access Blocked by Cloudflare Security Check
1/24/2026

Security
Why Short-Lived Certificates Are Revolutionizing Security in Modern Infrastructure
1/24/2026

Security
Reddit's New API Access Control: What It Means for Developers and Bots
1/24/2026