
Security
Azure AD B2C to Entra External ID Migration Kit: A Strategic Overview for Enterprise Architects
1/18/2026

Security
Understanding Reddit's Security Blocks: What Developers Need to Know
1/17/2026
Security
Understanding Network Security Blocks on Developer Platforms
1/17/2026

Security
Snap Store Security Crisis: Hijacked Publisher Domains Fuel Malware Surge
1/17/2026

Security
Third-Party Risks in 2026: Outlook and Security Strategies
1/17/2026

Security
Developer Fights AI Scraping Bots with Markov-Generated Garbage
1/17/2026
Security
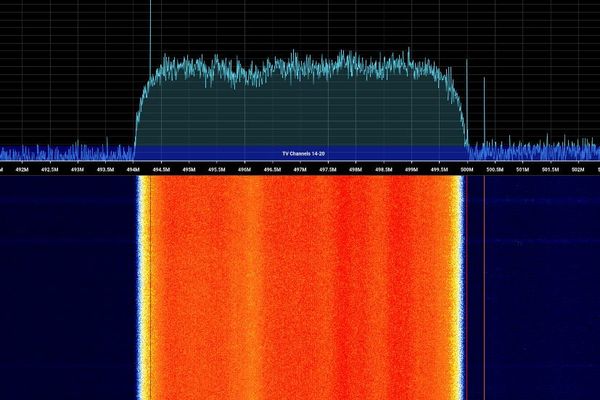
How Ordinary TV Signals Detect Movement Through Walls
1/17/2026

Security
Massive $282M Crypto Heist: Social Engineering Attack Drains Hardware Wallet, Funds Converted to Monero
1/17/2026

Security
Combating Cheating in Classic Doom 2 Deathmatch
1/17/2026

Security
How AI Is Being Used For Border Surveillance
1/17/2026
Security
Reddit Tightens Network Security: Blocks Prompt Login or Developer Token
1/17/2026

Security
Password Utility Solves FileVault Reboot Challenges for Remote Mac Management
1/17/2026

Security
Reddit's New API Access Controls Are Blocking Developers
1/17/2026