Security
New ClickFix Variant Uses WebDAV and Legitimate WorkFlowy App to Evade Detection
3/14/2026

Cybersecurity
FBI Investigation Targets Malware-Infected Steam Games Stealing User Data and Cryptocurrency
3/14/2026

Vulnerabilities
Zombie ZIP Vulnerability Exposes Critical Antivirus Blind Spot
3/14/2026
Security
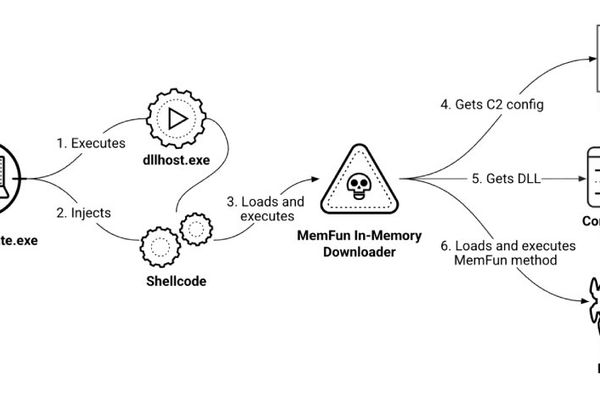
Chinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
3/13/2026

Security
Credential-stealing crew spoofs Ivanti, Fortinet, Cisco VPNs • The Register
3/13/2026

Cybersecurity
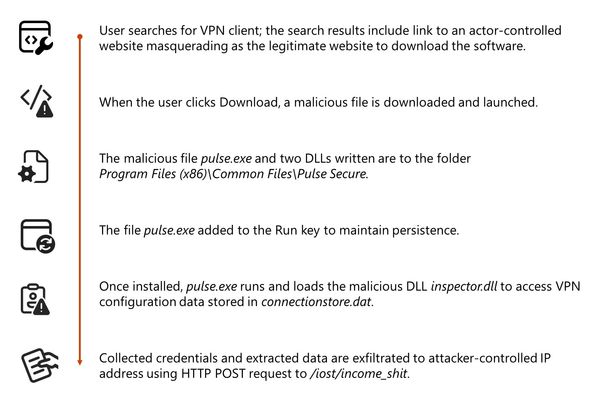
Storm-2561 Credential Theft Campaign Targets VPN Users Through SEO Poisoning
3/13/2026

Cybersecurity
Hive0163 Uses AI-Assisted Slopoly Malware for Persistent Access in Ransomware Attacks
3/12/2026

Cybersecurity
Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays
3/12/2026
Security
Storm-2561 Uses SEO Poisoning to Distribute Fake VPN Clients for Credential Theft
3/12/2026

Security
Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets
3/12/2026

Security
KadNap Malware Infects 14,000+ Edge Devices to Power Stealth Proxy Botnet
3/10/2026

Security
The New Turing Test: How Malware Uses Geometry to Prove 'Humanness'
3/10/2026

Cybersecurity
Fake job applications pack malware that disables EDR • The Register
3/10/2026