Attackers are increasingly sophisticated in their evasion techniques, employing mathematical analysis of human behavior and system performance to determine whether malware is running in a real environment or a security sandbox. This 'digital Turing test' represents a significant shift in malware behavior that traditional security tools struggle to detect.
The cybersecurity landscape is witnessing an unsettling evolution in malware tactics. Instead of the loud, disruptive breaches that once dominated headlines, attackers are now favoring stealthy, long-term infiltration. To support this shift toward remaining undetected, malware developers are advancing their evasion techniques with surprising mathematical sophistication, implementing what security researchers are calling a 'new Turing test' based on geometric analysis.
"Attackers are pivoting away from bold 'smash-and-grab' breaches in favor of sneakier 'Digital Parasite' tactics," explains Sila Ozeren Hacioglu, Security Research Engineer at Picus Security. "The Picus Red Report™ 2026 confirms this massive shift, with 80% of the top ten observed techniques now dedicated strictly to evasion and persistence."
The Rise of Virtualization Evasion
Driving this trend is the resurgence of Virtualization/Sandbox Evasion (T1497), a technique that had fallen from prominence but has now skyrocketed to become the #4 most-used technique in 2025. According to the Picus Red Report, which analyzed more than 1.1 million malicious files and 15.5 million actions mapped to MITRE ATT&CK® throughout 2025, this technique is now present in 20% of analyzed malware samples.

This means that one in five modern malware strains will simply 'play dead' if they detect that they're in an automated analysis environment, rendering traditional detection methods ineffective.
Three Advanced Evasion Techniques
1. System Checks (T1497.001): The Environment Gatekeeper
System Checks involve malware performing a series of observations to gather information about the host environment before executing its payload. These checks look for telltale artifacts that indicate a virtualized analysis environment:
- Disk drives named after VM vendors (like "VBOX" or "VMWare")
- MAC addresses tied to hypervisors
- Limited CPU cores
- Absence of audio/video devices
The Blitz malware exemplifies this approach. As detailed in the Red Report, Blitz executes specific programmatic checks:
- Processor Count: Aborting if the CPU count is fewer than four
- Screen Resolution: Exiting if the resolution matches standard default sandbox sizes
- Sandbox Drivers: Searching for specific driver strings associated with known analysis tools
"If these system checks indicate an artificially restricted environment, Blitz aborts execution," notes Hacioglu. "This ensures the malware only 'goes live' on legitimate, user-controlled systems."
2. User Activity Based Checks (T1497.002): The Trigonometry-Based Turing Test
This is where the 'new Turing test' truly emerges. Rather than simply checking whether the mouse moves, advanced malware now evaluates how it moves, using mathematical analysis to determine if a human is behind the keyboard.
The LummaC2 v4.0 malware, analyzed in November 2025, implements what Hacioglu calls a "Trigonometry-Based Turing Test." Here's how it works:
- Motion Capture: Using the GetCursorPos() Windows API, the malware records five consecutive (x,y) cursor positions with 50ms delays between each sample.
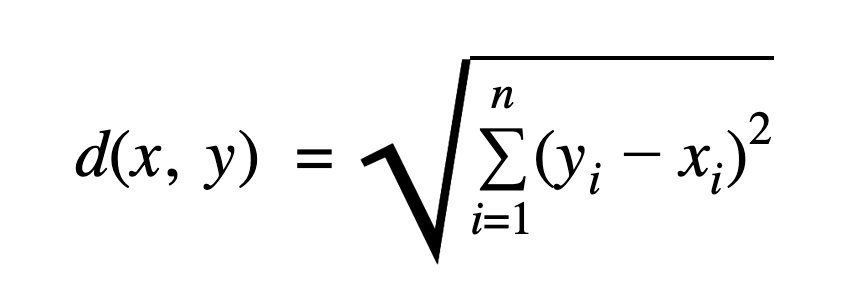
- Euclidean Distance: The malware calculates the length of each movement segment using the standard Euclidean distance formula to ensure motion is continuous and not "teleporting" (a common sandbox shortcut).
- Angular Validation: It computes the angle between consecutive vectors using the dot product formula. The resulting angle, converted to degrees, is compared against a hardcoded 45° threshold.
"Human motion, even when attempting a straight line, naturally introduces micro-curves and subtle variation," explains Hacioglu. "By mathematically measuring curvature and smoothness, LummaC2 applies a probabilistic filter to determine whether it is operating in a real user environment before releasing its payload."
3. Time Based Checks (T1497.003): Beating the Clock
The third advanced technique involves monitoring system performance to detect the "invisible drag" of a hypervisor. Modern implementations go beyond simple sleep timers, actively measuring how time passes on the CPU to identify anomalies characteristic of virtualized environments.
Blitz malware employs a sophisticated timing check by spinning up two concurrent threads:
- Main Thread: Executes a CPUID instruction loop 1,000,000 times (quick on bare metal but slower when intercepted by a VM)
- Secondary Thread: Executes complex floating-point calculations, incrementing a global_count variable with each success
Once the main thread finishes, the malware calculates a ratio to see how many floating-point operations the secondary thread completed in that timeframe. If the system is a physical machine, the concurrent threads run smoothly, and the resultant value exceeds 5.0. However, if a hypervisor is present, the overhead slows the secondary thread down, the resultant falls below 5.0, and the malware terminates itself.
Implications for Security Defenses
This evolution in malware tactics presents significant challenges for traditional security approaches.
"When malware checks hypervisor timing or inspects system artifacts before executing, traditional defenses often see nothing," warns Hacioglu. "Static signatures miss it. Sandboxes return clean results, and no alert is triggered because the payload never runs."
The fundamental problem is that attackers aren't just delivering malicious files—they're selectively executing malicious behavior based on environmental conditions. This requires a shift in security strategy:
- From File Analysis to Behavior Hunting: Security teams must move beyond analyzing static artifacts to validating adversarial behavior in their own environments.
- Adversarial Exposure Validation (AEV): Tools like Breach and Attack Simulation (BAS) and automated penetration testing can continuously and safely execute real-world attacker techniques against the actual security stack.
- Continuous Testing: Security controls must be regularly validated to ensure they prevent execution, trigger detections, and activate response mechanisms as expected.
"In a landscape increasingly defined by stealth and selective execution, theoretical risk scores are no longer enough," concludes Hacioglu. "Security teams need to move from simply identifying threats to validating that their defenses can actually stop these sophisticated evasion techniques in practice."
The Picus Red Report 2026 offers five threat templates to help organizations test their defenses against these advanced evasion techniques. As malware continues to evolve in sophistication, so too must our approaches to detection and prevention.
For more detailed analysis and mitigation strategies, organizations can refer to the Picus Red Report 2026 and explore Adversarial Exposure Validation methodologies.
Comments
Please log in or register to join the discussion