A financially motivated threat group called Diesel Vortex has been stealing credentials from freight and logistics operators in the U.S. and Europe since September 2025, using 52 domains and a highly organized operation.
A financially motivated threat group dubbed "Diesel Vortex" is conducting a sophisticated phishing campaign targeting freight and logistics organizations across the United States and Europe, stealing credentials from critical industry platforms since September 2025.
Campaign Scale and Impact
The campaign has already compromised 1,649 unique credentials from platforms and service providers essential to the freight industry. Researchers at Have I Been Squatted discovered the operation after finding an exposed repository containing an SQL database from a phishing project the threat actor called "Global Profit" and marketed to other cybercriminals as "MC Profit Always."
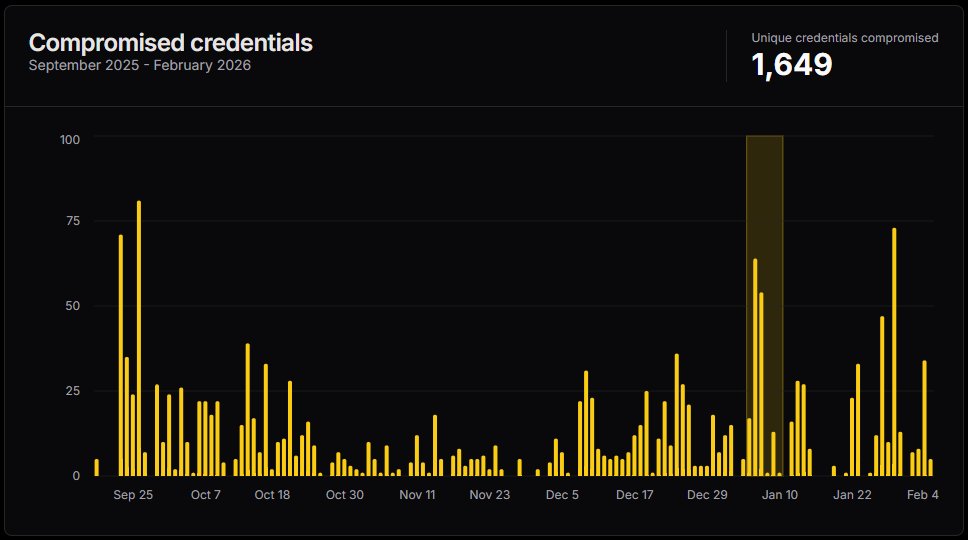
Volume of Diesel Vortex credential theft Source: Have I Been Squatted
The compromised platforms include major industry players such as DAT Truckstop, TIMOCOM, Teleroute, Penske Logistics, Girteka, and Electronic Funds Source (EFS). The threat actor operates 52 domains specifically designed to target these platforms.
Highly Organized Operation
Analysis reveals Diesel Vortex operates as a "highly organised operation" complete with dedicated roles including a call centre, mail support, programmers, and staff responsible for finding drivers, carriers, and logistics contacts. The group maintains detailed documentation including a mind map that outlines their operational structure and acquisition channels.
"The [Diesel Vortex] group built dedicated phishing infrastructure for platforms used daily by freight brokers, trucking companies, and supply chain operators," researchers noted. "Load boards, fleet management portals, fuel card systems, and freight exchanges were all in scope."
Technical Attack Methodology
The phishing attacks employ multiple sophisticated techniques:
- Email delivery: Uses Zoho SMTP and Zeptomail services
- Evasion tactics: Combines Cyrillic homoglyph tricks in sender and subject fields to bypass security filters
- Multi-channel approach: Includes voice phishing and infiltration of Telegram channels frequented by trucking and logistics personnel
- Cloaking process: Implements a 9-stage cloaking process on system domains (.top/.icu)
- Pixel-perfect replicas: Creates phishing pages that are exact clones of targeted logistics platforms
When victims click phishing links, they encounter minimal HTML pages on .com domains containing full-screen iframes that load the phishing content. The attack flow is controlled by operators who decide when to approve steps and activate subsequent phases via Telegram bots.
Data Collection Scope
Depending on the target platform, the phishing pages capture extensive information including:
- Credentials and passwords
- Multi-factor authentication codes and security tokens
- MC/DOT numbers and RMIS login details
- Payment amounts, payee names, and check numbers
- Permit data and PINs
The operators maintain direct control over the phishing process, with possible actions including requesting credentials for Google, Microsoft Office 365, and Yahoo accounts, managing 2FA methods, redirecting victims, or blocking them mid-session.
Attribution and Connections
Based on language analysis and infrastructure connections, researchers believe Diesel Vortex is an Armenian-speaking actor connected to Russian infrastructure. Ctrl-Alt-Intel's OSINT investigation revealed connections to individuals and companies in Russia involved in wholesale trade, transportation, and warehousing.
"The same email identified used to register phishing infrastructure appears in [Russian] corporate filings for logistics companies operating in the same vertical targeted by Diesel Vortex," researchers noted.
Beyond Credential Theft
The Diesel Vortex operation extends beyond simple credential theft. The group coordinates activities related to:
- Freight impersonation
- Mailbox compromise
- Double-brokering or cargo diversion
Double brokering involves using stolen carrier identities to book loads and then reassigning or diverting freight cargo to fraudulent pickup points, enabling cargo theft.
Disruption and Mitigation
The Diesel Vortex operation, including panel and phishing domains and GitLab repositories, was disrupted following coordinated action involving GitLab, Cloudflare, Google Threat Intelligence, CrowdStrike, and Microsoft Threat Intelligence Center.
For organizations in the freight and logistics sector, security experts recommend enhanced monitoring of email communications, implementing multi-factor authentication with hardware tokens where possible, and conducting regular security awareness training focused on phishing tactics specific to the transportation industry.
The full indicators of compromise (IoCs), including network, Telegram, infrastructure, email, and cryptocurrency addresses, are available in the complete Have I Been Squatted report.

Comments
Please log in or register to join the discussion