Threat actors are impersonating IT support staff to deliver the Havoc command-and-control framework through sophisticated social engineering, DLL sideloading, and persistence mechanisms across multiple organizations.
Threat hunters have uncovered a sophisticated campaign where cybercriminals impersonate IT support staff to deliver the Havoc command-and-control (C2) framework, marking a concerning evolution in social engineering tactics. The intrusions, identified by Huntress across five partner organizations last month, demonstrate how attackers are combining traditional spam campaigns with personalized phone calls to establish persistent access.
The Attack Chain: From Spam to Persistent Access
The campaign begins with a classic email bombing technique, overwhelming target inboxes with junk emails. However, what sets this apart is the follow-up phone call from someone claiming to be IT support. The caller contacts recipients directly, offering to help remediate the spam problem by establishing remote access through Quick Assist sessions or tools like AnyDesk.
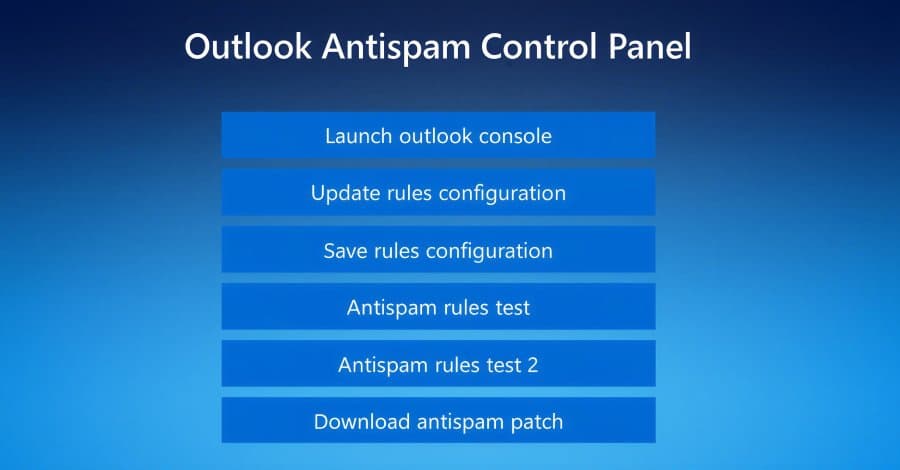
Once the victim grants access, the attacker wastes no time. They launch the web browser and navigate to a fake landing page hosted on Amazon Web Services that impersonates Microsoft. The counterfeit page instructs victims to enter their email address to access Outlook's anti-spam rules update system.
Clicking the "Update rules configuration" button triggers a script that displays an overlay asking for the user's password. This serves a dual purpose: harvesting credentials for the attacker's control panel while adding authenticity to convince the victim the process is legitimate.
Sophisticated Malware Delivery
The attack's sophistication becomes apparent in the malware delivery phase. Instead of delivering malware directly, the threat actor downloads what appears to be an anti-spam patch. This leads to the execution of legitimate binaries like "ADNotificationManager.exe" or "Werfault.exe" to sideload a malicious DLL.
The DLL payload implements multiple defense evasion techniques:
- Control flow obfuscation to complicate analysis
- Timing-based delay loops to evade sandbox detection
- Hell's Gate and Halo's Gate techniques to hook ntdll.dll functions
- Bypassing endpoint detection and response (EDR) solutions
The DLL then spawns a thread containing the Havoc Demon agent, establishing the initial foothold.
Rapid Lateral Movement and Persistence
Following successful deployment of the Havoc Demon on the initial host, the threat actors demonstrated aggressive lateral movement. In one organization, the adversary moved from initial access to nine additional endpoints within eleven hours. This speed strongly suggests the end goal was data exfiltration, ransomware, or both.
For persistence, the attackers employed multiple strategies:
- Creating scheduled tasks to launch the Havoc Demon payload on every reboot
- Deploying legitimate remote monitoring and management (RMM) tools like Level RMM and XEOX on some compromised hosts
- Diversifying persistence mechanisms to survive remediation attempts
Connection to Black Basta Playbook
The campaign's modus operandi shows striking similarities to email bombing and Microsoft Teams phishing attacks previously associated with the Black Basta ransomware operation. While Black Basta appears to have gone silent following a public leak of its internal chat logs last year, the continued presence of its playbook suggests two possibilities:
- Former Black Basta affiliates have moved to other ransomware operations, bringing their techniques with them
- Rival threat actors have adopted the same strategy for social engineering and initial access
Key Takeaways for Organizations
This campaign reveals several important trends in modern cyber attacks:
Social Engineering Evolution: Threat actors are increasingly willing to impersonate IT staff and call personal phone numbers if it improves success rates. The combination of automated spam with personalized phone calls creates a powerful social engineering vector.
Democratization of Advanced Techniques: Defense evasion techniques once limited to attacks on large firms or state-sponsored campaigns are becoming increasingly common in commodity malware. The use of Hell's Gate, Halo's Gate, and sophisticated DLL sideloading demonstrates this trend.
Customization of Commodity Malware: The Havoc framework is being customized to bypass pattern-based signatures, making traditional signature-based detection less effective.
Speed of Compromise: The rapid progression from initial compromise to lateral movement (eleven hours in one case) highlights the need for immediate incident response capabilities.
Persistence Diversity: The use of both custom malware and legitimate RMM tools for persistence shows attackers are planning for long-term access and anticipating remediation efforts.
The Bigger Picture
This campaign represents a case study in how modern adversaries layer sophistication at every stage. From social engineering to gain initial access, through DLL sideloading to maintain stealth, to diversified persistence mechanisms for survival, each component builds upon the last.
The attackers' willingness to combine multiple attack vectors – spam, phone calls, fake websites, legitimate software abuse, and custom malware – demonstrates the increasing professionalism of cybercrime operations. What begins as a phone call from "IT support" ends with a fully instrumented network compromise, with modified Havoc Demons deployed across endpoints and legitimate RMM tools repurposed as backup persistence.
Organizations must adapt their security strategies to address this multi-layered approach, focusing not just on technical controls but also on employee awareness and incident response readiness. The speed and sophistication of these attacks leave little room for error, making proactive defense and rapid detection more critical than ever.
Comments
Please log in or register to join the discussion